10 Tips for Security Awareness Training That Hits the Target
Dark Reading
OCTOBER 27, 2023
Try these tricks for devising an education program that gets employees invested — and stays with them after the training is over.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
OCTOBER 27, 2023
Try these tricks for devising an education program that gets employees invested — and stays with them after the training is over.

Security Affairs
NOVEMBER 29, 2022
In today’s technological world, educating people about cybersecurity awareness is an absolute necessity. These errors are not always entirely preventable, as some level of human error is inevitable, but proper training in cybersecurity awareness can greatly decrease the likelihood of human mistakes leading to data breaches.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Dark Reading
FEBRUARY 28, 2020
Microsoft's director of security education and awareness shares his approach to helping train employees in defensive practices.
eSecurity Planet
AUGUST 22, 2022
Twenty years ago, Saturday Night Live nailed a tendency in IT to be overly absorbed in tech-speak and to do a poor job of educating users. A recent experience highlighted that security awareness training and most alerts to users about unsafe practices may be making the error of being too general. That’s a good start.

The Last Watchdog
JULY 11, 2023
Related: Preserving the privacy of the elderly As more traders and investors engage in these investment avenues, it is crucial to adopt robust security measures to safeguard sensitive and regulated information. Here are seven tips to protect investor data in alternative asset trading. Stay informed about security best practices.

Security Affairs
SEPTEMBER 20, 2020
National Cyber Security Centre (NCSC) has issued an alert about a surge in ransomware attacks targeting education institutions. National Cyber Security Centre (NCSC), has issued an alert about a surge in ransomware attacks against education institutions. SecurityAffairs – hacking, education institutions).
IT Governance
APRIL 5, 2023
Malware is one of the most common cyber security threats that organisations and individuals face. In this blog, we explain everything you need to know about it, including our top 8 tips for preventing malware attacks. Make sure to keep backups in a secure location. However, those tools are not flawless. What is malware?

IT Governance
OCTOBER 6, 2022
This October is Cyber Security Awareness Month, an event designed to educate people about information security and the steps they can take to stay safe online. Now in its nineteenth year, the campaign provides tools and resources to help people learn more about the cyber security industry and the ways they can get involved.

eDiscovery Daily
AUGUST 4, 2023
Privacy and security concerns with sensitive and confidential information and staying compliant with jurisdiction-specific laws and regulations like the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA) is an ongoing challenge. Educate and train staff.

The Last Watchdog
FEBRUARY 15, 2021
Cybersecurity training has steadily gained traction in corporate settings over the past decade, and rightfully so. In response to continuing waves of data breaches and network disruptions, companies have made a concerted effort and poured substantial resources into promoting data security awareness among employees, suppliers and clients.

IT Governance
OCTOBER 29, 2018
Yet staff awareness and education are key components of any organisation’s GDPR compliance framework. . one of the biggest cyber security threats is inside your organisation , there’s never been a better time to ensure your organisation has an effective GDPR staff awareness training programme in place. . 3 ) Be thorough

IT Governance
OCTOBER 29, 2018
Yet staff awareness and education are key components of any organisation’s GDPR compliance framework. . one of the biggest cyber security threats is inside your organisation , there’s never been a better time to ensure your organisation has an effective GDPR staff awareness training programme in place. . 3 ) Be thorough

IT Governance
MAY 27, 2021
For all the talk of criminal hacking, ransomware infections and the technologies to prevent them, the key to protecting your organisation is cyber security awareness training. The importance of cyber security staff awareness. Cyber security awareness best practices. Training should occur multiple times a year.

IT Governance
NOVEMBER 24, 2021
But as is often the case with technological solutions, the benefits of convenience comes with security risks. In this blog, we look at the top five Cloud security challenges that organisations face, and provide tips on how to overcome them. You can find out how to get started with our Phishing Staff Awareness Training Programme.

IT Governance
OCTOBER 30, 2018
Staff awareness training is a core component of GDPR compliance, yet many organisations haven’t implemented the necessary measures. For all the attention that organisations pay to information security, the biggest threat continues to come from employees. Staff training under the GDPR.

IT Governance
OCTOBER 30, 2018
Staff awareness training is a core component of GDPR compliance, yet many organisations haven’t implemented the necessary measures. For all the attention that organisations pay to information security, the biggest threat continues to come from employees. Staff training under the GDPR.

Archive Document Data Storage
JANUARY 2, 2018
2018 is here, and it’s time to revisit your data security strategy. In this blog post, we offer our tips for keeping your information safe all year long. Setup a Virtual Private Network (VPN) for secure, remote access to network applications. Design a Secure Destruction Plan. secure loading and unloading areas.
Security Affairs
OCTOBER 17, 2023
This is happening despite an exponential increase in organizational cyber training over the past decade. With 85% of campaigns targeting victims with phishing emails containing malicious links, another form of a social engineering attack, education and cyber vigiliance remain a high priority.
IT Governance
OCTOBER 23, 2023
Secure remote working tips and VPN insights from our senior penetration tester Leon Teale is a senior penetration tester at IT Governance. He’s also been featured in various articles relating to cyber security. So how can organisations efficiently secure their remote infrastructure? We sat down to chat to him.

AIIM
APRIL 29, 2021
8 Tips for Fighting Money, Focus, and Cultural Restraints Around Change Management. Here are six tips for fighting money, focus, and cultural restraints around change management projects: 1. Educate potentially stressed individuals on why changes need to occur. "Senior executives seem uninterested in information management.

eSecurity Planet
OCTOBER 16, 2023
Public cloud security refers to protections put in place to secure data and resources in cloud environments shared by multiple users or organizations. Major cloud service providers have generally had good security , so cloud users can be pretty confident in the security of their data and applications if they get their part right.

The Last Watchdog
AUGUST 2, 2018
Claire McCaskill by Russian intelligency agency hackers, as she runs for re-election, underscores the need for each individual and organization to take online privacy and security as a core part of our everyday lives. Related: Using ‘gamification’ for security training. Schrade r: Absolutely.

IT Governance
SEPTEMBER 30, 2022
Across the UK, the education sector was the most frequently targeted, with 24 incidents. Small businesses are vulnerable to cyber attacks because they lack the resources to address cyber security. Smaller companies justifiably prioritise growing their operation, leaving cyber security on the sidelines,” he said.

IT Governance
DECEMBER 9, 2021
Cloud security is an essential part of today’s cyber security landscape. To mitigate these risks, the NCSC (National Cyber Security Centre) created the Cloud Security Principles , which outline 14 guidelines for protecting information stored online.

The Schedule
MAY 18, 2017
Several weeks ago the University Archivist and I conducted our bi-annual University Archives and Records Management training session, part of our Office of Human Resources Faculty and Staff Development Program. So how to improve participation in records management training (RM)? Make it hard to miss. Focus your approach.

eSecurity Planet
AUGUST 22, 2023
Cybersecurity can be difficult to implement, and to make matters worse, the security professionals needed to do it right are in short supply. Managed IT security service providers (MSSPs) make life easier for organizations by providing outsourced expertise and tools at a fraction of the cost, time, and trouble of doing it yourself.

The Security Ledger
SEPTEMBER 30, 2021
Max gives us some tips about how best to respond to ransomware threats and attacks. As always, you can check our full conversation in our latest Security Ledger podcast at Blubrry. There are many contributing factors, but one of the most important is the shortage of cyber security talent in the trenches of modern organizations.

Data Matters
APRIL 20, 2021
The Cybersecurity Guidance is directed at plan sponsors and fiduciaries regulated by the Employee Retirement Income Security Act of 1974 (ERISA) as well as plan participants and beneficiaries. The Cybersecurity Guidance is set forth in three parts: Tips for Hiring a Service Provider , directed toward plan sponsors and fiduciaries.

Thales Cloud Protection & Licensing
NOVEMBER 22, 2022
But negative blowback from major breaches in the 2000s, fines imposed by regulators, and strict cyber security mandates such as PCI-DSS, helped retailers dramatically improve cyber security and slow down the wave of attacks. Despite the above findings, retailers are pretty serious about the security of their businesses.

KnowBe4
APRIL 4, 2023
But, according to security researchers at Abnormal Security, cybercriminals are becoming brazen and are taking their shots at very large prizes. According to Abnormal Security, nearly every aspect of the request looked legitimate. Get a look at THREE NEW FEATURES and see how easy it is to train and phish your users.

IT Governance
OCTOBER 13, 2023
October is both Cybersecurity Awareness Month in the US and European Cyber Security Month in the EU – twin campaigns on either side of the Atlantic that aim to improve awareness of the importance of cyber security both at work and at home, and provide tips on how to stay secure.

IT Governance
JUNE 30, 2022
Although Wiltshire Farm Foods has revealed few details about the incident, cyber security experts believe that it bears the hallmarks of ransomware. Education is the key to ransomware prevention. As such, employees are often the last line of defence, and it’s why we recommend enrolling them on regular staff awareness training courses.

KnowBe4
MARCH 28, 2023
Security awareness training still has a place to play here." Email and other elements of software infrastructure offer built-in fundamental security that largely guarantees we are not in danger until we ourselves take action," Tyson writes. Get a look at THREE NEW FEATURES and see how easy it is to train and phish your users.

AIIM
DECEMBER 28, 2018
Empowerment, education and engagement. Demonstrate value: You need to clearly demonstrate and communicate the added value of digitizing your content in order to engage and educate employees. Training: You need to use a variety of methods and styles of training to support your employees.

IT Governance
JULY 29, 2019
Protecting your organisation against cyber crime can sometimes feel like a never ending game of security whack-a-mole. Just as soon as you’ve secured one weakness, it seems as though another vulnerability rears its head. In this post, we outline five essential ways of keeping your organisation secure.

IT Governance
SEPTEMBER 8, 2021
In this blog, we take a look at some of the problems you will encounter and provide tips to help you address them. Educate employees on their responsibilities. So how should organisations approach employee education? As we’ve previously discussed, hybrid working introduces new cyber security risks.

IT Governance
MARCH 7, 2023
This month, we’re dedicating our feature to a topic that has been circling the cyber security sector – and many others besides – for some time: AI (artificial intelligence). Cyber security is no exception. Fighting fire with fire It’s not only the good guys that are using AI in the cyber security landscape.

Rocket Software
SEPTEMBER 27, 2021
Now, companies are struggling to find new talent to fill this skills vacuum, and when they do, it is difficult to properly train them without those established experts to offer guidance. Here are three tips companies can use to highlight the opportunities available in the mainframe space. . Don’t Limit the Candidate Pool .

IT Governance
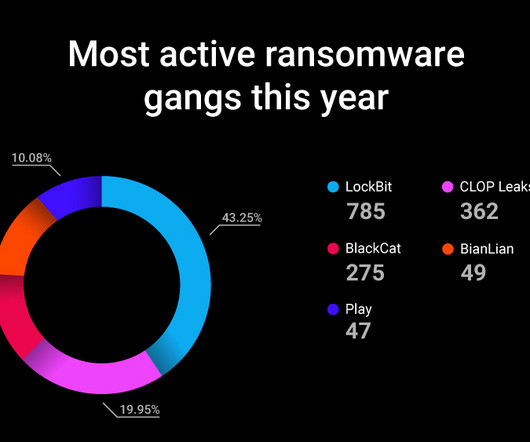
MAY 11, 2021
Our Q1 2021 review of data breaches found that almost one in three publicly disclosed security incidents was a ransomware attack, and in April alone, we discovered 53 cases. And that’s just the tip of the iceberg; there are plenty of organisations who fall victim and don’t disclose the damage. Find out more.

Thales Cloud Protection & Licensing
JANUARY 5, 2022
During the latest Thales Security Sessions podcast , hosted by Neira Jones, I had the pleasure to discuss what we can expect in 2022 with Andy Green, CISO at Gemserv, and how the many changes have impacted the security landscape. What are the key security challenges for 2022? Data security.

ForAllSecure
APRIL 27, 2023
It wasn’t long before security followed, with DevSecOps now shorthand for modern application security—and everything from SAST, DAST and SCA shoehorned into developers’ toolchains and workflows. Instead of treating security as an afterthought, the DevSecOps process makes it a priority from the very beginning.

Preservica
NOVEMBER 30, 2022
Digital Preservation tips from the Canadian Museum of Immigration at Pier 21. Learn more about Preservica and AWS hosting options in Canada at Secure Digital Preservation, Archiving & Storage Software | Preservica.

The Texas Record
AUGUST 27, 2019
The Texas State Operations Center released a 56 minute educational webinar on protective measures and response activities related to ransomware. To protect themselves and their organizations, individuals should remember these cybersecurity tips : It is everyone’s responsibility to remain cyber aware and practice information safety.

eSecurity Planet
APRIL 9, 2024
SaaS security checklists are frameworks for protecting data and applications in cloud-based environments. They serve as benchmarks for upholding strong security requirements, evaluating existing tools, and assessing potential solutions. We’ve designed a customizable template to help you develop your own SaaS security checklist.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content