Educating Educators: Microsoft's Tips for Security Awareness Training
Dark Reading
FEBRUARY 28, 2020
Microsoft's director of security education and awareness shares his approach to helping train employees in defensive practices.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
FEBRUARY 28, 2020
Microsoft's director of security education and awareness shares his approach to helping train employees in defensive practices.

The Last Watchdog
JULY 11, 2023
Related: Preserving the privacy of the elderly As more traders and investors engage in these investment avenues, it is crucial to adopt robust security measures to safeguard sensitive and regulated information. Here are seven tips to protect investor data in alternative asset trading. Stay informed about security best practices.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
SEPTEMBER 20, 2020
National Cyber Security Centre (NCSC) has issued an alert about a surge in ransomware attacks targeting education institutions. National Cyber Security Centre (NCSC), has issued an alert about a surge in ransomware attacks against education institutions. SecurityAffairs – hacking, education institutions).

Dark Reading
OCTOBER 27, 2023
Try these tricks for devising an education program that gets employees invested — and stays with them after the training is over.

Dark Reading
JANUARY 17, 2023
Following these basic cybersecurity hygiene policies can help make data more secure and protect colleges and universities from becoming the next ransomware headline. The steps aren't complicated, and they won't break the bank.
IT Governance
APRIL 5, 2023
Malware is one of the most common cyber security threats that organisations and individuals face. In this blog, we explain everything you need to know about it, including our top 8 tips for preventing malware attacks. Make sure to keep backups in a secure location. However, those tools are not flawless. What is malware?

Security Affairs
NOVEMBER 29, 2022
In today’s technological world, educating people about cybersecurity awareness is an absolute necessity. Due to the increasing use of digital tools for business operations and reliance on employee conduct to ensure security, new solutions are required. Below are five tips to gamify your cybersecurity awareness training program.
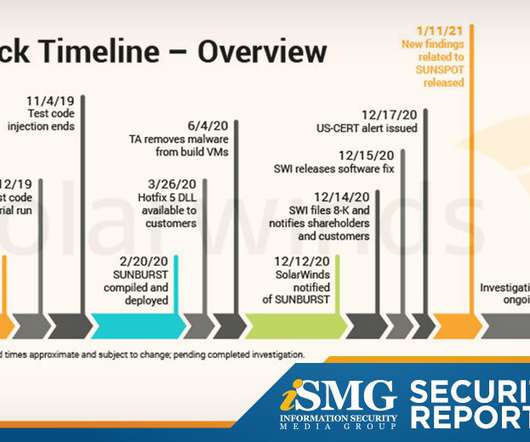
Data Breach Today
JANUARY 15, 2021
The latest edition of the ISMG Security Report describes new details emerging from the SolarWinds supply chain hack investigation. Also featured: A discussion of why security education is so crucial in 2021 and tips on how to retain SOC analysts.

Thales Cloud Protection & Licensing
JUNE 26, 2023
Small and Medium Businesses Day: Tips on Securing the Backbone of National Economies madhav Tue, 06/27/2023 - 05:46 The United Nations General Assembly designated 27 June as Micro-, Small, and Medium-sized Enterprises Day to raise awareness of these businesses’ contribution to national economies. Strong access control through MFA 2.

IT Governance
OCTOBER 6, 2022
This October is Cyber Security Awareness Month, an event designed to educate people about information security and the steps they can take to stay safe online. Now in its nineteenth year, the campaign provides tools and resources to help people learn more about the cyber security industry and the ways they can get involved.

The Last Watchdog
JULY 1, 2022
This raises the concerns of corporate data security in remote working that still stand as a key challenge that organizations are trying to navigate, workforce productivity being the second. Managing endpoints securely . This is also why looking for a solution with a holistic approach can be such a tipping point.

IT Governance
APRIL 28, 2020
If you’re among the millions of people working from home while also trying to entertain and educate your kids during the coronavirus pandemic, we imagine things have been pretty chaotic. The Internet can be a dangerous place, which is why we talk so often about the importance of secure browsing. Install antivirus software.

IT Governance
NOVEMBER 24, 2021
But as is often the case with technological solutions, the benefits of convenience comes with security risks. In this blog, we look at the top five Cloud security challenges that organisations face, and provide tips on how to overcome them. Data breaches. The website is simply designed to look like the real thing.
eSecurity Planet
AUGUST 22, 2022
Twenty years ago, Saturday Night Live nailed a tendency in IT to be overly absorbed in tech-speak and to do a poor job of educating users. A recent experience highlighted that security awareness training and most alerts to users about unsafe practices may be making the error of being too general. I wanted to get to the bottom of it.

eDiscovery Daily
AUGUST 4, 2023
Privacy and security concerns with sensitive and confidential information and staying compliant with jurisdiction-specific laws and regulations like the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA) is an ongoing challenge. Educate and train staff.

Archive Document Data Storage
JANUARY 2, 2018
2018 is here, and it’s time to revisit your data security strategy. In this blog post, we offer our tips for keeping your information safe all year long. Setup a Virtual Private Network (VPN) for secure, remote access to network applications. Design a Secure Destruction Plan. secure loading and unloading areas.

The Last Watchdog
FEBRUARY 15, 2021
In response to continuing waves of data breaches and network disruptions, companies have made a concerted effort and poured substantial resources into promoting data security awareness among employees, suppliers and clients. Cybersecurity education for kids is therefore a smart investment. Tools and approaches. Offer employee perks?
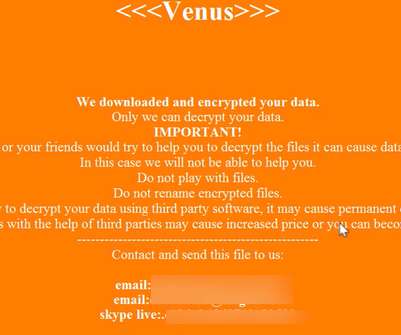
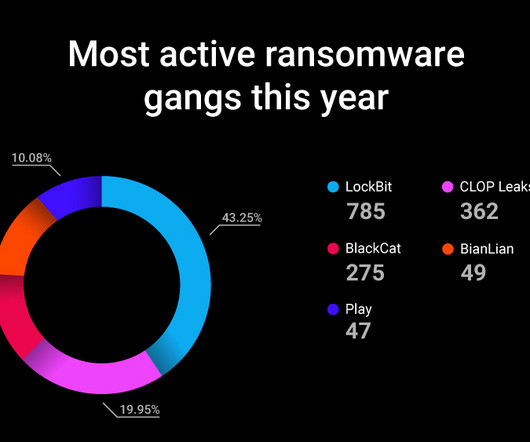
Krebs on Security
DECEMBER 8, 2022
Alex Holden is founder of Hold Security , a Milwaukee-based cybersecurity firm. Security firm Tripwire points out that the HHS advisory on Venus says multiple threat actor groups are likely distributing the Venus ransomware. “ Cl0p ” a.k.a. “ TA505 “), and a newer ransom group known as Venus. .

Rippleshot
SEPTEMBER 20, 2019
We also recognize the reality that data breaches happen when gaps exist in other organization's security protocols, which can leave your own customer's sensitive data vulnerable. That's why we're also here: To help you educate your customers and members when the next big data breach happens — and what to do about it.

The Last Watchdog
AUGUST 2, 2018
Claire McCaskill by Russian intelligency agency hackers, as she runs for re-election, underscores the need for each individual and organization to take online privacy and security as a core part of our everyday lives. Related: Using ‘gamification’ for security training. A large retailer may spend millions on cyber security.

eSecurity Planet
OCTOBER 16, 2023
Public cloud security refers to protections put in place to secure data and resources in cloud environments shared by multiple users or organizations. Major cloud service providers have generally had good security , so cloud users can be pretty confident in the security of their data and applications if they get their part right.

OneHub
JULY 18, 2019
Unfortunately, for many small to medium-sized companies, the up-front capital expenses of cyber security are out of reach. If you’re researching cloud service providers, we suggest checking for the following must-have security features. 4 Security Features Only the Best Business Cloud Storage Providers Use.

Schneier on Security
OCTOBER 13, 2023
who filled in the questionnaire’s “name” field with “No, no, no,” said the 50 percent floor and “NO attendance enforcement” leads to a scenario where “we get students who skip over 100 days, have a 50 percent, complete a couple of assignments to tip over into 59.5 percent and then pass.”

IT Governance
MAY 27, 2021
For all the talk of criminal hacking, ransomware infections and the technologies to prevent them, the key to protecting your organisation is cyber security awareness training. The importance of cyber security staff awareness. Cyber security awareness best practices. Implementing cyber security awareness training.
IT Governance
OCTOBER 23, 2023
Secure remote working tips and VPN insights from our senior penetration tester Leon Teale is a senior penetration tester at IT Governance. He’s also been featured in various articles relating to cyber security. So how can organisations efficiently secure their remote infrastructure? We sat down to chat to him.

The Last Watchdog
MAY 5, 2022
Let’s walk through some practical steps organizations can take today, implementing zero trust and remote access strategies to help reduce ransomware risks: •Obvious, but difficult – get end users to stop clicking unknown links and visiting random websites that they know little about, an educational challenge. Food for thought, eh!
Security Affairs
OCTOBER 17, 2023
With 85% of campaigns targeting victims with phishing emails containing malicious links, another form of a social engineering attack, education and cyber vigiliance remain a high priority. Why should employers educate employees about cyber security? For large businesses, those costs may be a drop in the ocean.

AIIM
APRIL 29, 2021
8 Tips for Fighting Money, Focus, and Cultural Restraints Around Change Management. Here are six tips for fighting money, focus, and cultural restraints around change management projects: 1. Educate potentially stressed individuals on why changes need to occur. "Senior executives seem uninterested in information management.

IT Governance
DECEMBER 9, 2021
Cloud security is an essential part of today’s cyber security landscape. To mitigate these risks, the NCSC (National Cyber Security Centre) created the Cloud Security Principles , which outline 14 guidelines for protecting information stored online.

The Last Watchdog
JANUARY 13, 2021
The question isn’t whether we should educate children about online safety, but how we can best inspire them to learn to be thoughtful, careful, and safe in the cyber world for their lifetime. Teaching children about good cyber security habits starts with helping them realize their power to learn to make smart choices.

eSecurity Planet
AUGUST 22, 2023
Cybersecurity can be difficult to implement, and to make matters worse, the security professionals needed to do it right are in short supply. Managed IT security service providers (MSSPs) make life easier for organizations by providing outsourced expertise and tools at a fraction of the cost, time, and trouble of doing it yourself.

IT Governance
JANUARY 24, 2022
It’s why, for the past fifteen years, 28 January has marked Data Privacy Day – an international event raises awareness about online privacy and educates people on the ways they can protect their personal information. Another tip offered by the campaign is to review the privacy and security settings on web services and apps that you use.

OneHub
JANUARY 3, 2019
With 2019 upon us, many businesses are beginning to consider their data security practices for the new year. Whether your company operates primarily in the online space, or simply uses a secure cloud storage platform to manage and share your business files, data security is incredibly important.

Adam Levin
AUGUST 26, 2020
Schools and companies should consider the following: Set up accounts with competing services: While Zoom holds a dominant position, it is by no means the only video conferencing platform for meetings or for education. If your school or educator hasn’t provided these, check online for one of several free resources for education. .

The Security Ledger
SEPTEMBER 30, 2021
Max gives us some tips about how best to respond to ransomware threats and attacks. As always, you can check our full conversation in our latest Security Ledger podcast at Blubrry. There are many contributing factors, but one of the most important is the shortage of cyber security talent in the trenches of modern organizations.
Krebs on Security
NOVEMBER 17, 2022
In an interview with KrebsOnSecurity, James said Unit 221B was wary of advertising its ability to crack Zeppelin ransomware keys because it didn’t want to tip its hand to Zeppelin’s creators, who were likely to modify their file encryption approach if they detected it was somehow being bypassed. This is not an idle concern.

IG Guru
JUNE 9, 2020
Policies and Procedures, Tools and Tips, can all be found here regarding Work From Home (WFH). The post Remote Working and Mobile Device Security and Privacy Resources via Privacy & Security Brainiacs appeared first on IG GURU.

Data Matters
APRIL 20, 2021
The Cybersecurity Guidance is directed at plan sponsors and fiduciaries regulated by the Employee Retirement Income Security Act of 1974 (ERISA) as well as plan participants and beneficiaries. The Cybersecurity Guidance is set forth in three parts: Tips for Hiring a Service Provider , directed toward plan sponsors and fiduciaries.
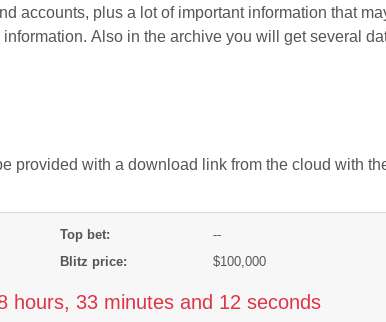
Krebs on Security
JUNE 2, 2020
” The FBI and multiple security firms have advised victims not to pay any ransom demands, as doing so just encourages the attackers and in any case may not result in actually regaining access to encrypted files. Filter all email: Invest in security systems that can block executable files at the email gateway.

The Security Ledger
OCTOBER 18, 2021
Eric Goldstein, Executive Assistant Director for Cybersecurity for the Cybersecurity and Infrastructure Security Agency (CISA), says the agency is all about helping companies and local government to keep hackers at bay. As always, you can check our full conversation in our latest Security Ledger podcast at Blubrry. As the U.S.

ForAllSecure
APRIL 27, 2023
It wasn’t long before security followed, with DevSecOps now shorthand for modern application security—and everything from SAST, DAST and SCA shoehorned into developers’ toolchains and workflows. Instead of treating security as an afterthought, the DevSecOps process makes it a priority from the very beginning.

The Last Watchdog
JUNE 1, 2021
Primarily the Pharming attack is planned to gain sensitive data like login credentials, personally identifiable information (PII), social security numbers, bank details, and more. An SSL certificate ensures that the website is encrypted and secure. A few more tips. However, you can change it with a more secure one.

IT Governance
OCTOBER 13, 2023
October is both Cybersecurity Awareness Month in the US and European Cyber Security Month in the EU – twin campaigns on either side of the Atlantic that aim to improve awareness of the importance of cyber security both at work and at home, and provide tips on how to stay secure.

IT Governance
SEPTEMBER 30, 2022
Across the UK, the education sector was the most frequently targeted, with 24 incidents. Small businesses are vulnerable to cyber attacks because they lack the resources to address cyber security. Smaller companies justifiably prioritise growing their operation, leaving cyber security on the sidelines,” he said. Get started.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content