Securing OT and IoT Assets in an Interconnected World
Data Breach Today
JUNE 6, 2023
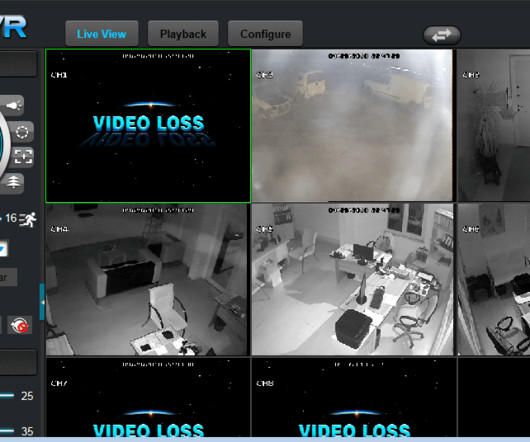
In this episode of "Cybersecurity Insights," Antoinette Hodes of Check Point Research discusses the need to consolidate an organization's cybersecurity posture, gain visibility into OT and IT assets, and use cybersecurity education to increase worker safety.








































Let's personalize your content