Cyber Insurance: Higher Premiums, Limited Coverage
Data Breach Today
MAY 24, 2021
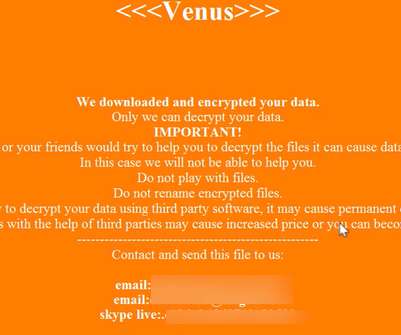
GAO Report Summarizes Market Trends The increasing number of cyberthreats, especially ransomware attacks, is leading some cyber insurers to raise premiums and limit some coverage in hard-hit sectors, such as healthcare and education, according to a report from the Government Accountability Office.













































Let's personalize your content