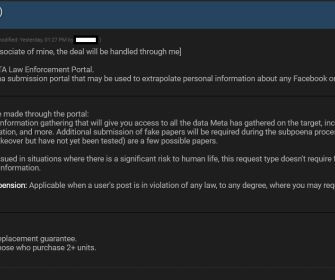
'Log in with.' Feature Allows Full Online Account Takeover for Millions
Dark Reading
OCTOBER 24, 2023
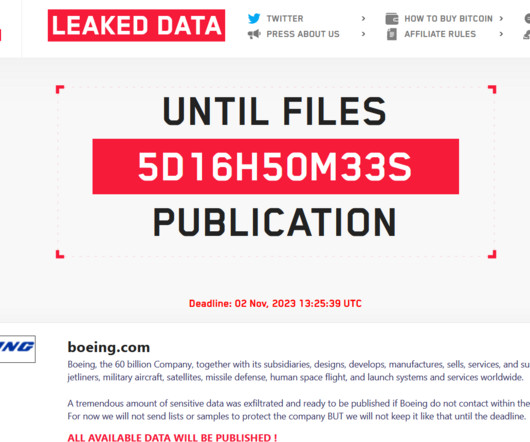
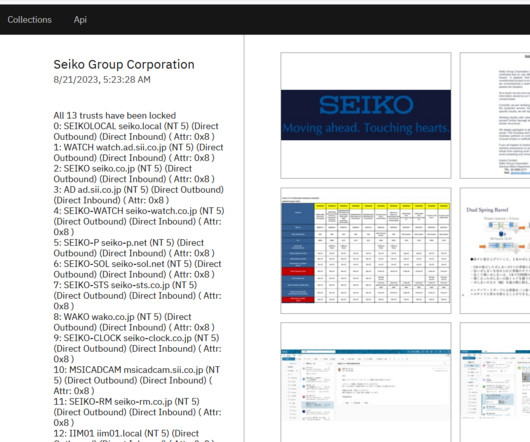
Hundreds of millions of users of Grammarly, Vidio, and the Indonesian e-commerce giant Bukalapak are at risk for financial fraud and credential theft due to OAuth misfires -- and other online services likely have the same problems.



































Let's personalize your content