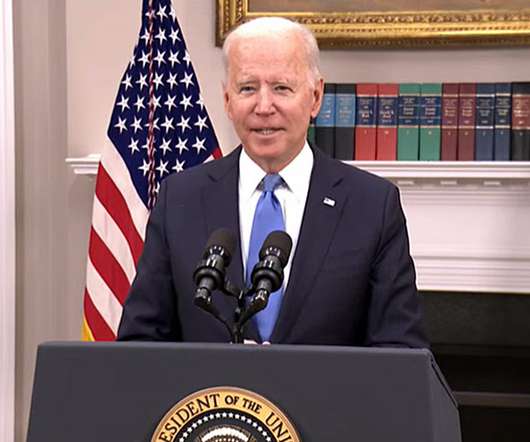
Biden Signs Sweeping Executive Order on Cybersecurity
Data Breach Today
MAY 13, 2021
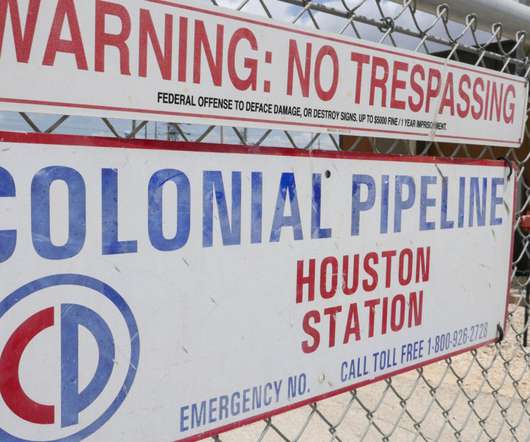
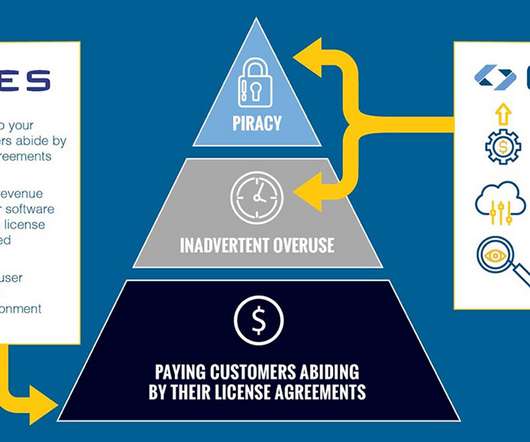
Order Emphasizes Partnerships, IT Modernization and Supply Chain Security President Joe Biden signed an extensive executive order Wednesday, detailing the government's plan to increase cybersecurity protection across the public and private sectors, as well as securing the nation's infrastructure against the type of attack that targeted SolarWinds and its customers.






































Let's personalize your content