‘Copyright Violation’ Notices Lead to Facebook 2FA Bypass
Threatpost
OCTOBER 28, 2020
Fraudulent Facebook messages allege copyright infringement and threaten to take down pages, unless users enter logins, passwords and 2FA codes.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 copyright-notice
copyright-notice 
Threatpost
OCTOBER 28, 2020
Fraudulent Facebook messages allege copyright infringement and threaten to take down pages, unless users enter logins, passwords and 2FA codes.

CILIP
JANUARY 22, 2024
Copyright: The demise of ‘skill, labour and effort’? Is a photograph or digital image of a 2D artwork that is itself out of copyright, protected by copyright? Since copyright relies on a work being ‘original,’ it has long been argued that no new copyright can arise in a photographic copy of a 2D artwork.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Texas Record
MARCH 23, 2021
How long should you keep records documenting the copyright of an original work of authorship? Records documenting the copyright status of original works are administratively valuable when it comes to crafting licensing agreements, drafting acceptable use notices, responding to infringement lawsuits, etc.

Security Affairs
APRIL 11, 2020
The news was reported by the Reuters that seen a notice sent by the Italian bank to its customers. According to the notice, the attack took place on March 30 when some messages with voice mail attachments had been sent. “The notice to customers made no mention of any breach of company data. . ” reports the Reuters.

Security Affairs
NOVEMBER 4, 2020
The Notice Regarding Network Issues published by the company states that on the morning of November 2nd, 2020 is suffered a cyberattack, In response to the incident the game developer shut down portions of their corporate network to prevent the malware from spreading. ” reads the Notice Regarding Network Issues published by the company.

Security Affairs
APRIL 11, 2020
” continues the data breach notice. At the time of writing, the SFOConnect is up and running, SFOConstruction points to a copy of the Notice of Data Breach stored on an S3 bucket. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->.
Security Affairs
OCTOBER 7, 2020
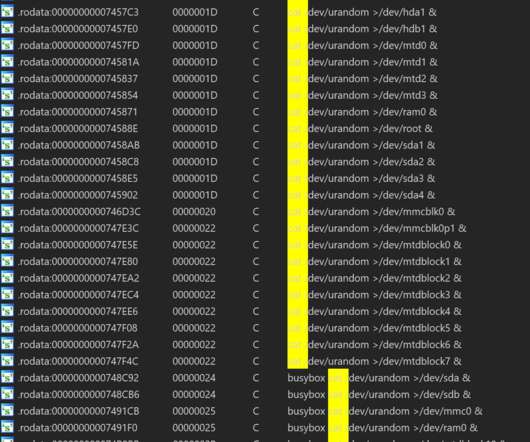
Experts noticed that the malware supports multiple CPU architectures, including x86(32/64), ARM(32/64), MIPS(MIPS32/MIPS-III) and PPC, it is written in the Go open-source programming language. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. We will see what the author comes up with the Attack feature.”
Security Affairs
NOVEMBER 2, 2020
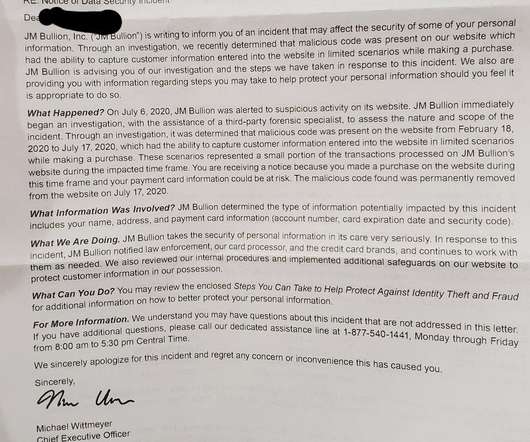
JM Bullion has sent a ‘ Notice of Data Security Incident ‘ to its customers, the security breach took place on February 18, 2020, when its staff discovered a malicious script on its website. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.

Security Affairs
SEPTEMBER 14, 2020
The popular security expert Troy Hunt , who runs the data breach notification service HaveIBeenPwned published on Twitter the incident notice sent out by the company to its customers. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.
Security Affairs
SEPTEMBER 29, 2020
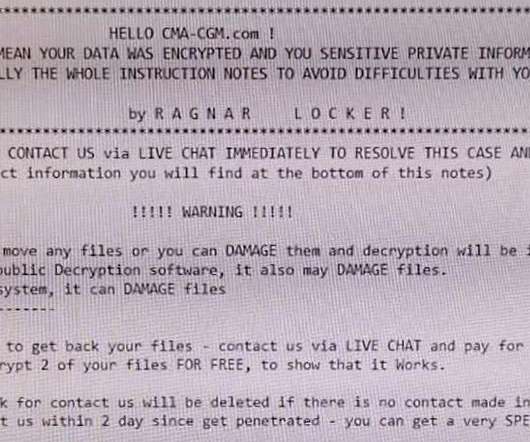
” reads the security notice published by the company. “An investigation is underway, conducted by our internal experts and by independent experts,” continues the notice. ” ~ Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.

Security Affairs
MAY 5, 2020
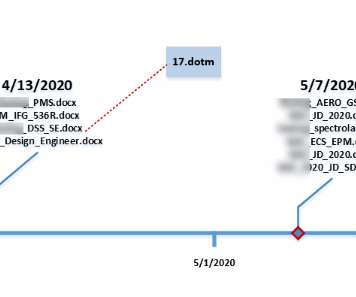
The hosting provider submitted a data breach notice with the California Attorney General, it revealed that the intrusion took place in October 2019. ” reads the data breach notice submitted by the company. ” continues the notice. ” concludes the notice. Pierluigi Paganini.
Security Affairs
DECEMBER 2, 2019
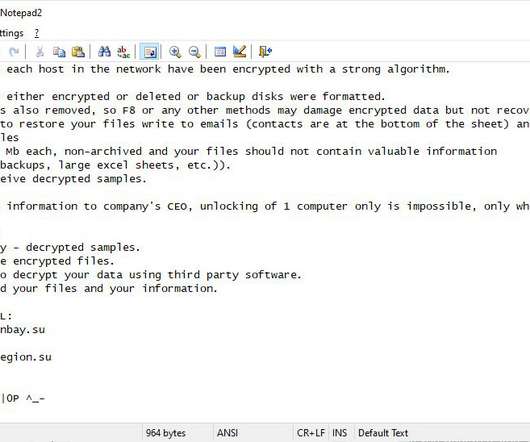
Experts noticed that the TA505 cybercrime group has been using the CryptoMix ransomware after compromising a network in similar attacks as Ryuk , BitPaymer , and DoppelPaymer. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->.
Security Affairs
JANUARY 25, 2022
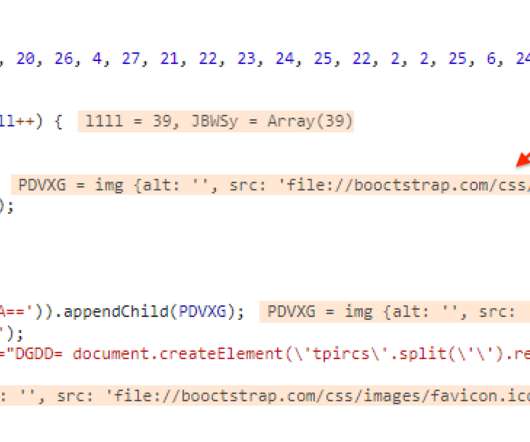
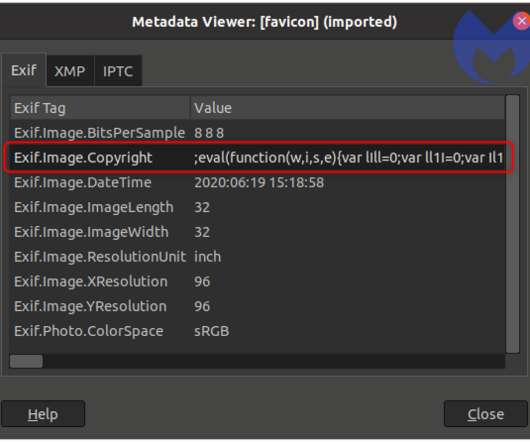
Researchers noticed the Segway store was contacting a known skimmer domain (booctstrap[.]com) Attackers added JavaScript to Segway’s online store that pretended to display the site’s copyright, but that was used to load an external favicon that contained the e-skimming code.
Security Affairs
MARCH 20, 2020
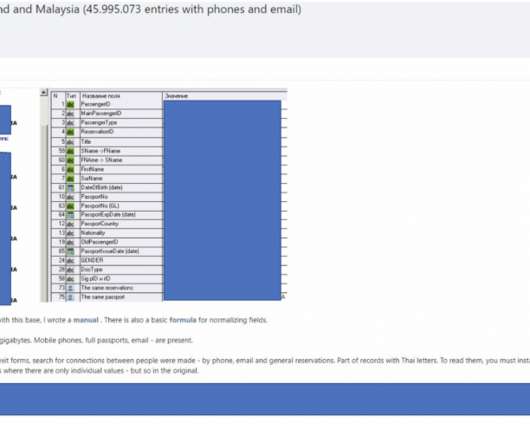
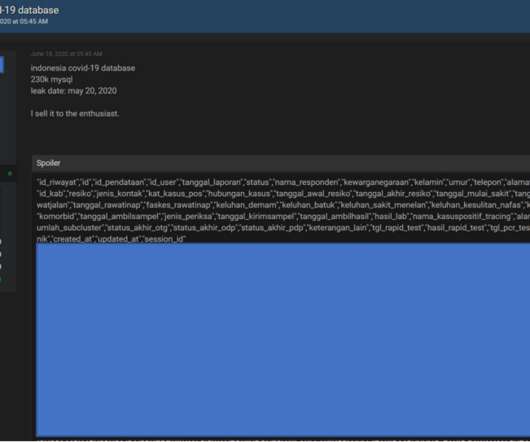
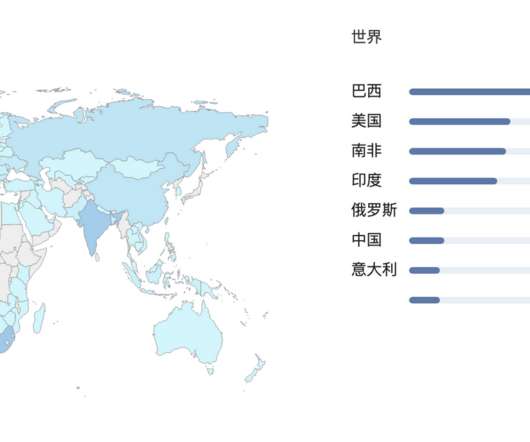
“There are potentially over 100,000 users affected by this data leak, with implications not only for copyright violations, but also American and British military data exposure.” Military documents belong to the US and UK military, experts noticed that the incident also impacted Doxzoo customers from India, Nigeria and Sri Lanka.

Security Affairs
NOVEMBER 4, 2020
Ahead of the 2020 Presidential election a mysterious transaction was noticed by cyber security experts and researchers. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.
Security Affairs
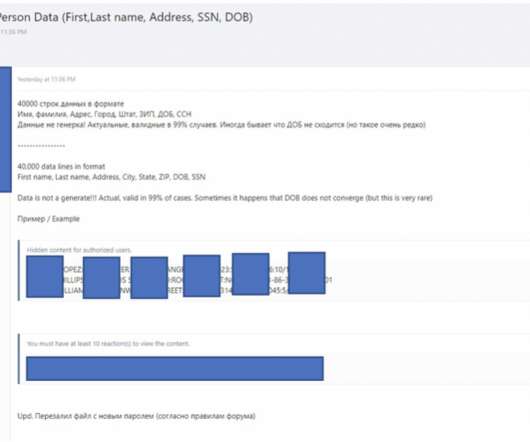
AUGUST 4, 2020
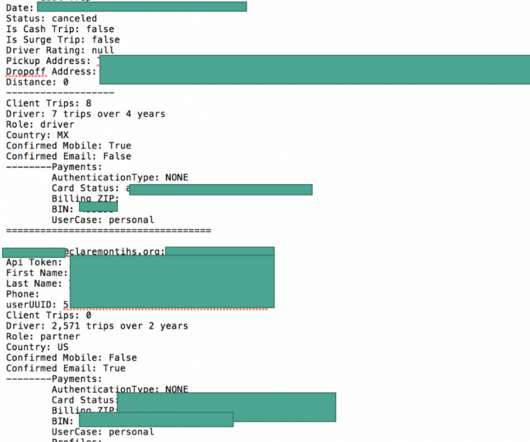
Cyble researchers provided the following recommendations: Never share personal information, including financial information over the phone, email or SMSs Use strong passwords and enforce multi-factor authentication where possible Regularly monitor your financial transaction, if you notice any suspicious transaction, contact your bank immediately.
Security Affairs
JULY 13, 2020
Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.

Schneier on Security
JULY 21, 2023
A Digital Millennium Copyright Act takedown notice is a present-day example of a microdirective. A DMCA takedown notice is tailored to the recipient’s specific legal circumstances. It also directs action—remove the targeted content or prove that it’s not infringing—based on the law.
Security Affairs
NOVEMBER 26, 2019
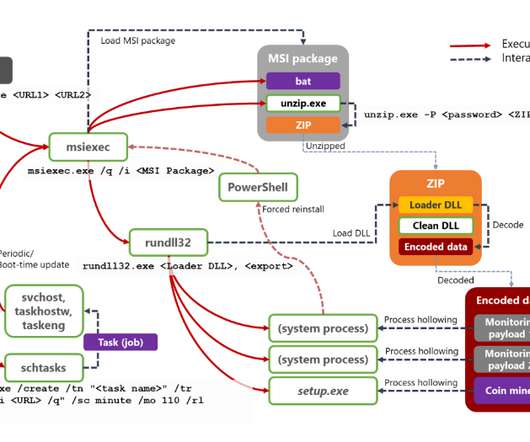
The experts noticed that the installer uses two URLs to download malicious payloads, the same two URLs are used by Dexphot to establish persistence, update the malware, and re-infect the device. In the specific case, experts noticed that Dexphot operators attempted to deploy files that changed every 20-30 minutes on thousands of devices. .
Security Affairs
JUNE 21, 2020
The company recommends people to: Never share personal information, including financial information over the phone, email or SMSs Use strong passwords and enforce multi-factor authentication where possible Regularly monitor your financial transaction, if you notice any suspicious transaction, contact your bank immediately. Pierluigi Paganini.
Security Affairs
JULY 9, 2020
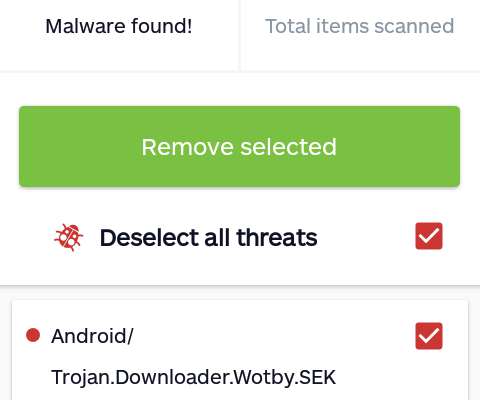
” Like the UMX U686CL model, also the ANS UL40 comes with malicious programs masquerades as Settings and Wireless Update apps, but experts noticed that the malware families involved in the two cases are different. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. ” concludes the post.

Security Affairs
FEBRUARY 29, 2020
” reads the data breach notice issued by the company. According to the data breach notice send sent by email to the affected individuals, the attack took place on January 30 and February 7. “We are committed to helping those who may have been impacted by this unfortunate situation,” continues the notice.
Security Affairs
JUNE 26, 2020
Experts noticed that the script would load a favicon file that is identical to the one used by the compromised website. The attackers loaded the e-skimmer from the ‘Copyright’ field in the metadata of this image. ” ~ Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->.

Security Affairs
JUNE 26, 2020
Once compromised the system, the attacker can execute arbitrary commands on the infected device, experts noticed that the bot could target Windows hosts on both the internet and intranet. Unit42 researchers noticed that the attacker is leveraging certutil utility in the payload for malware propagation. Pierluigi Paganini.

Security Affairs
AUGUST 30, 2020
Experts noticed that the malicious package was designed to steal only specific sensitive information from the infected developers’ systems. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. ” concludes the advisory.
Security Affairs
OCTOBER 5, 2020
” When the botnet was first detected in 2019, experts noticed it was exploiting the Tenda zero-day flaw tracked as CVE-2020-10987. ” ~ Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. ” concludes the report.

Security Affairs
JULY 8, 2020
The experts noticed that the bogus app was initially used as a dropper, and was updated later. In the last couple of days, researchers from Threat Labs noticed that the malicious code was receiving command from a C2 to download a Cerberus banker in the form of an APK. Avast researchers already reported to Google their findings.
Security Affairs
JULY 30, 2020
The researchers noticed that the infrastructure and TTPs (Techniques, Tactics, and Procedures) used in this campaign overlaps with the ones previously associated with Hidden Cobra. McAfee ATR noticed several different types of implants were used by the adversary in the 2020 campaigns.” Pierluigi Paganini.

Security Affairs
APRIL 30, 2020
Chegg employees,” reads the notice of data breach published on the California Attorney General’s website. We believe that your information may have been obtained, which is why you are receiving this notice.” Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.
Security Affairs
MARCH 5, 2020
” continues the notice. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Customers who believe they might have been impacted by the data breach could contact Customer Care for additional information and assistance.
Security Affairs
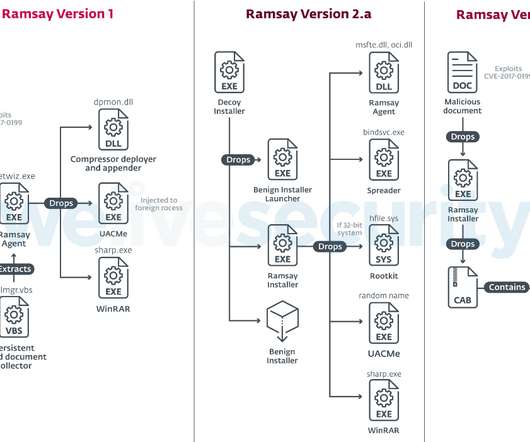
MAY 14, 2020
b samples have been compiled on March 8 and March 27, respectively, both include a rootkit component, but experts noticed that only 2.a ESET did not attribute the Ramsay malware to a specific threat actor, researchers only notice some similarities with the Retro malware family employed by the DarkHotel APT group. Pierluigi Paganini.
Security Affairs
JULY 13, 2020
Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.
Security Affairs
DECEMBER 1, 2019
On Saturday, Mixcloud disclosed the incident breach, the security notice published by the company confirms the hack, but highlights that accessed systems do not store data such as full credit card numbers or mailing addresses. ” reads the security notice published by the company. Pierluigi Paganini.

Security Affairs
FEBRUARY 16, 2020
The attack took place on February 12, 2020, the incident was confirmed via Twitter by the foundation: We are currently investigating a suspicious situation with Trinity, please do not open or use Trinity on Desktop until further notice. To protect users, we have paused the Coordinator and advise users not to open Trinity until further notice.

Security Affairs
SEPTEMBER 17, 2020
Experts also noticed that systems infected with SunCrypt connect to an IP address previously associated with Maze ransomware operations. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.
Security Affairs
FEBRUARY 14, 2020
According to a Notice of Payment Card Incident published by the company, attackers have stolen some payment card data from cards used on point-of-sale (POS) devices from convenience stores and fuel pumps. . ” reads the notice issued by the company. ” continues the notices. Pierluigi Paganini.

Security Affairs
AUGUST 24, 2020
We continue to meet most customer shipping needs and we are not aware of any misuse of client information,” reads the notices from the company. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.
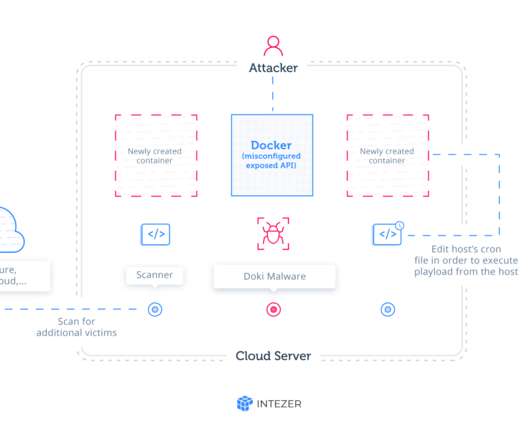
Security Affairs
JULY 29, 2020
” The botnet is scanning the Internet for misconfigured Docker API endpoints, Experts noticed that the Ngrok malware has already infected many vulnerable servers. Experts noticed that the script can install a fully undetected backdoor, dubbed by the researchers Doki. China, Austria, and the United Kingdom). Pierluigi Paganini.

Security Affairs
MAY 1, 2019
This week Citrix submitted a notice of data breach to the California Office of the Attorney General explaining that attackers had intermittent access to its network between October 13, 2018, and March 8, 2019. . ” reads the notice of data breach sent by Citrix. ” continues the notice. . Pierluigi Paganini.

Security Affairs
JANUARY 26, 2020
In the meantime, we ask for your patience in all matters relating to the citizen service facilities, ” “We put our systems offline for security reasons, because we have to assume an illegal cyberattack ,” The IT staff noticed “numerous inconsistencies” in central access to the capital of the state. Pierluigi Paganini.

Security Affairs
AUGUST 17, 2020
Experts at Cylance noticed that the decoy document titled “Pyongyang e-mail lists – April 2017, presents many similarities with a document used in a campaign that experts at Bitdefender linked to DarkHotel. . Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.
Security Affairs
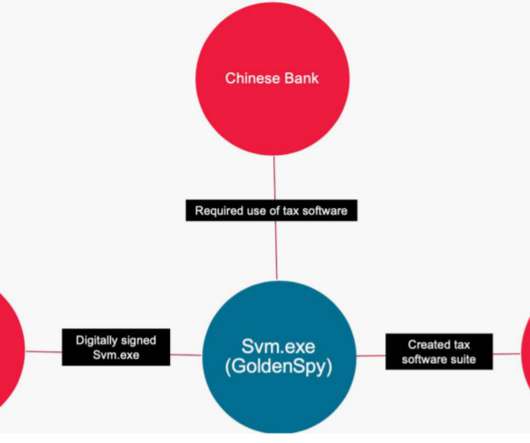
JUNE 29, 2020
” Experts noticed that the software covertly installs the hidden GoldenSpy backdoor (svm.exe) two hours after the tax software is installed. Experts noticed that once installed GoldenSpy is independent of the tax software, this means that even installing the Intelligent Tax software, the GoldenSpy will continue to work.

Security Affairs
NOVEMBER 22, 2019
” reads the data breach notice published by the company. “Rate plan and features of your voice calling service are ‘customer proprietary network information’ (‘CPNI’) under FCC rules, which require we provide you notice of this incident,” continues T-Mobile. Pierluigi Paganini.
Security Affairs
APRIL 5, 2020
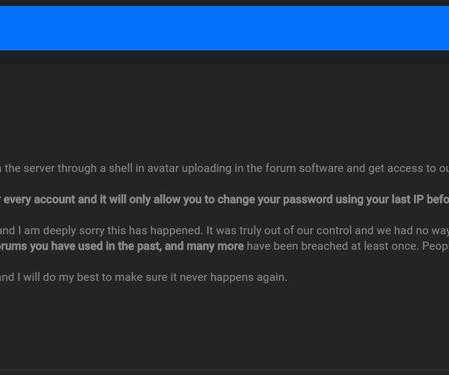
The data breach notice discovered by the data breach monitoring service Under the Breach. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini. SecurityAffairs – OGUsers forum, hacking).
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content