E-Verify’s “SSN Lock” is Nothing of the Sort
Krebs on Security
JULY 4, 2020
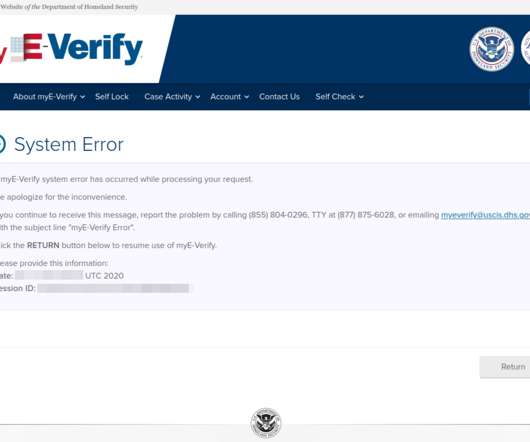
But KrebsOnSecurity recently discovered that this is not the case with all federal government sites built to help you manage your identity online. After verifying my email address, I was asked to pick a strong password and select a form of multi-factor authentication (MFA). It just reported that my SSN was now unlocked.


















Let's personalize your content