CISA, NSA, FBI, and MS-ISAC Release Phishing Prevention Guidance
KnowBe4
OCTOBER 19, 2023
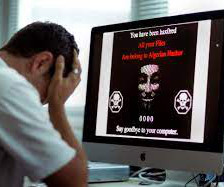
October 18, 2023, the Cybersecurity Infrastructure and Security Agency (CISA), the National Security Agency (NSA), the Federal Bureau of Investigation (FBI), and the Multi-State Information Sharing and Analysis Center (MS-ISAC) released a joint guide, Phishing Guidance: Stopping the Attack Cycle at Phase One. We could not agree more.

































Let's personalize your content