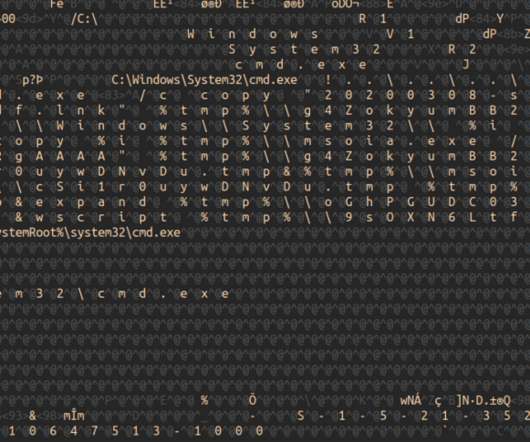
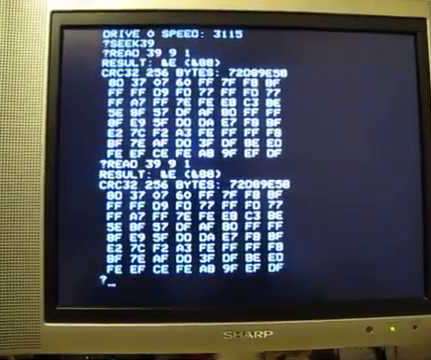
Step By Step Office Dropper Dissection
Security Affairs
APRIL 5, 2019
Malware researcher and founder of Yoroi Marco Ramill described a step-by-step procedure that shows how to dissect an Office dropper. During the past few weeks, I received several emails asking how to dissect Office Payloads. If you are interested on follow a full detailed analysis path, please take a look to Yoroi’s Blog.





































Let's personalize your content