MY TAKE: Why monetizing data lakes will require applying ‘attribute-based’ access rules to encryption
The Last Watchdog
JUNE 2, 2021
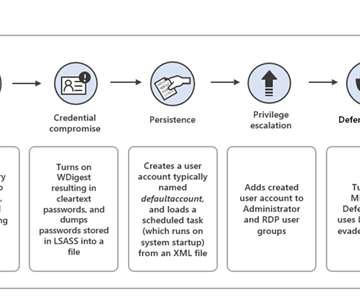
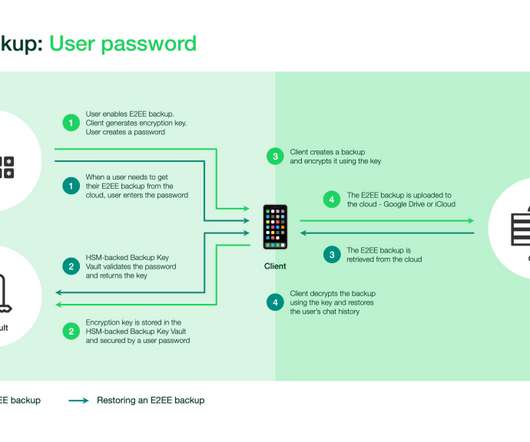
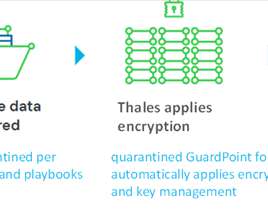
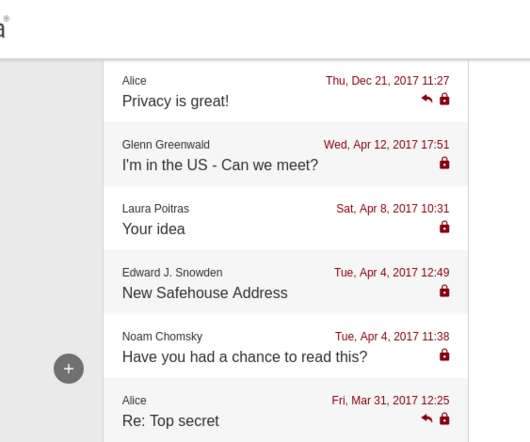
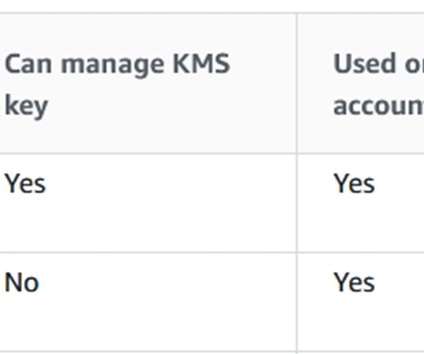
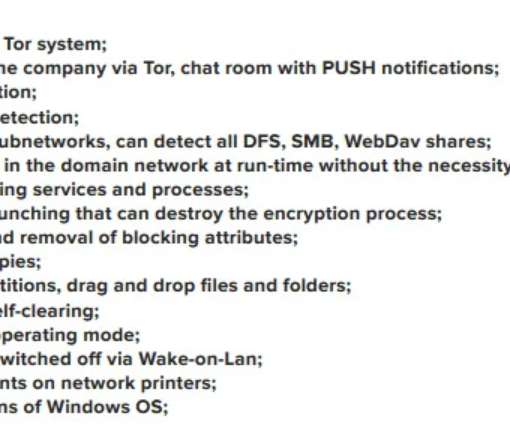
A new form of agile cryptography must get established in order to robustly preserve privacy and security as all this raw data gets put to commercial use. PKI is the authentication and encryption framework on which the Internet is built. Attribute-based access. In order to get there, one big technical hurdle must be surmounted.



































Let's personalize your content