OS upgrades 2023: Jamf Pro 11.0
Jamf
OCTOBER 10, 2023
Paired with new exciting features that ensure that MacAdmins of all experience levels feel right at home with the latest iteration of the best-in-breed, Apple-first, Apple-best MDM solution.
Jamf
OCTOBER 10, 2023
Paired with new exciting features that ensure that MacAdmins of all experience levels feel right at home with the latest iteration of the best-in-breed, Apple-first, Apple-best MDM solution.

Reltio
JUNE 20, 2023
When done well, master data management (MDM) transforms enterprise data from a chronic source of frustration to its most valuable asset. At Reltio, we call this approach modern MDM, which we pioneered back in 2011 with the launch of the industry’s first cloud-native SaaS platform.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Jamf
OCTOBER 5, 2023
Check new features in your MDM coming with macOS Sonoma upgrades 2023. Return to Service, FileVault keys support and more.

Reltio
DECEMBER 15, 2023
Here are some 2023 highlights that I am proud of: We started the year with a bold vision to revolutionize data unification and management by launching our velocity packs , which are out-of-the-box solutions with prepackaged configurations and integrations.

Reltio
APRIL 18, 2023
Unsurprisingly, a recent Gartner survey has identified a high demand for master data management (MDM) solutions. Modern MDM solutions can help tame the mess. Nevertheless, there is hope as MDM technology continues to evolve into the main data hub and a crucial component for enterprise data unification.

Security Affairs
AUGUST 1, 2023
US Cybersecurity and Infrastructure Security Agency (CISA) added the second actively exploited Ivanti ‘s Endpoint Manager Mobile (EPMM, formerly MobileIron Core) vulnerability, tracked as CVE-2023-35081 , to its Known Exploited Vulnerabilities Catalog. “Ivanti released a patch for CVE-2023-35078 on July 23, 2023. .
Security Affairs
AUGUST 4, 2023
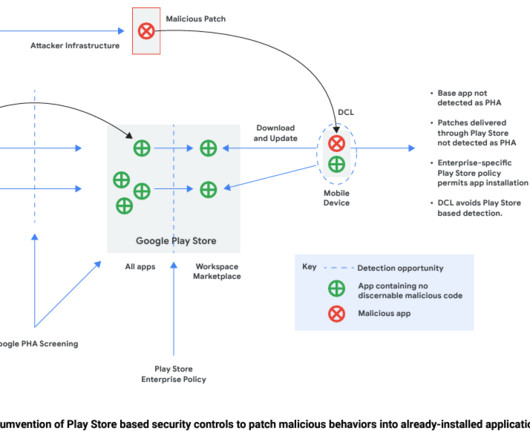
.” reads the Google Cybersecurity Action Team’s August 2023 Threat Horizons Report. ” Attackers rely on dynamic code loading (DCL) to push a malicious update.
Let's personalize your content