Security Outlook 2023: Cyber Warfare Expands Threats
eSecurity Planet
JANUARY 5, 2023
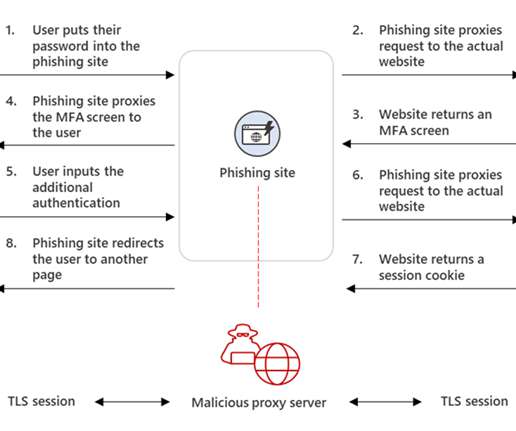
After a year that saw massive ransomware attacks and open cyber warfare, the biggest question in cybersecurity for 2023 will likely be how much of those attack techniques get commoditized and weaponized. Wiper Malware, Critical Infrastructure Threats Unleashed by War. Also read: Ransomware Protection: How to Prevent Ransomware Attacks.










































Let's personalize your content