Microsoft: North Korea-linked Zinc APT targets security experts
Security Affairs
JANUARY 29, 2021
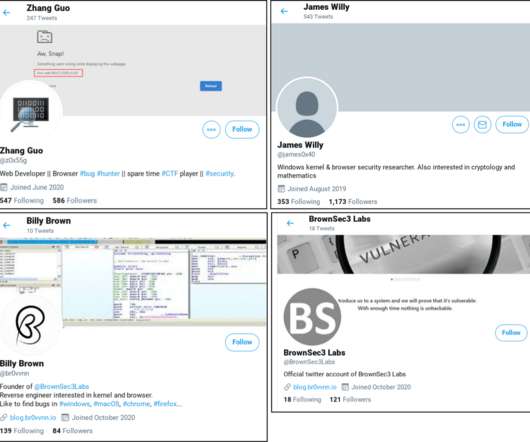
Microsoft, like Google TAG, observed a cyber espionage campaign aimed at vulnerability researchers that attributed to North Korea-linked Zinc APT group. ” This week, Google Threat Analysis Group (TAG) also warned of North Korea-linked hackers targeting security researchers through social media.





















Let's personalize your content