Ransomware Reportedly Hits Ventilator Maker
Data Breach Today
AUGUST 10, 2020
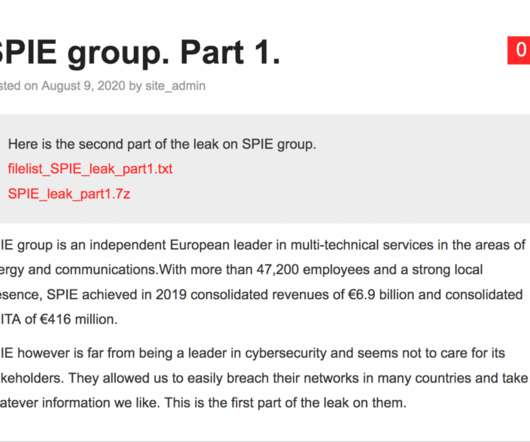
Incident Reflects Threats Facing Those Involved in COVID-19 Response A manufacturer of transit communication systems that pivoted to build ventilators during the COVID-19 pandemic is reportedly the latest victim of the DoppelPaymer ransomware gang.







































Let's personalize your content