Security Affairs newsletter Round 431 by Pierluigi Paganini – International edition
Security Affairs
AUGUST 6, 2023
It’s Testing U.S.

 12
12 
Security Affairs
AUGUST 6, 2023
It’s Testing U.S.
Security Affairs
FEBRUARY 21, 2020
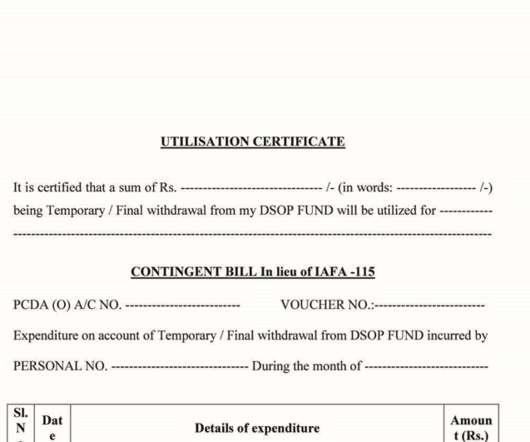
The Operation Transparent Tribe was first spotted by Proofpoint Researchers in Feb 2016, in a series of espionages operations against Indian diplomats and military personnel in some embassies in Saudi Arabia and Kazakhstan. The method used to send the information to the C2 is the following: Figure 11: C2 communication routine.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IT Governance
DECEMBER 13, 2018
This week, in our last podcast of the year, we revisit some of the biggest information security stories from the past 12 months. As is now traditional, I’ve installed myself in the porter’s chair next to the fire in the library, ready to recap some of the year’s more newsworthy information security events.

Data Matters
APRIL 23, 2018
A high-profile cyber incident may cause substantial financial and reputational losses to an organization, including the disruption of corporate business processes, destruction or theft of critical data assets, loss of goodwill, and shareholder and consumer litigation. Encrypting critical data assets. Using appropriate access controls.

ForAllSecure
JANUARY 15, 2021
Listen to EP 12: Hacking Healthcare. For example, in March of 2016, two researchers, Mike Ahmadi and Billy Rios independently reported an astounding fourteen hundred vulnerabilities to CareFusion's Pyxis SupplyStation, an automated, networked, supply cabinet used to store and dispense supplies. Apple Podcasts. Google Podcasts.

ForAllSecure
JANUARY 15, 2021
Listen to EP 12: Hacking Healthcare. For example, in March of 2016, two researchers, Mike Ahmadi and Billy Rios independently reported an astounding fourteen hundred vulnerabilities to CareFusion's Pyxis SupplyStation, an automated, networked, supply cabinet used to store and dispense supplies. Apple Podcasts. Google Podcasts.

Security Affairs
JANUARY 3, 2020
16 Defense Department Cyber Awareness Message identifying “TikTok as having potential security risks associated with its use,” according to the message.” ” The company behind TikTok attempted to reassure the US authorities explaining that all US user data are located outside China, and not subject to Chinese law. .
Let's personalize your content