OilRig APT group: the evolution of attack techniques over time
Security Affairs
AUGUST 7, 2019
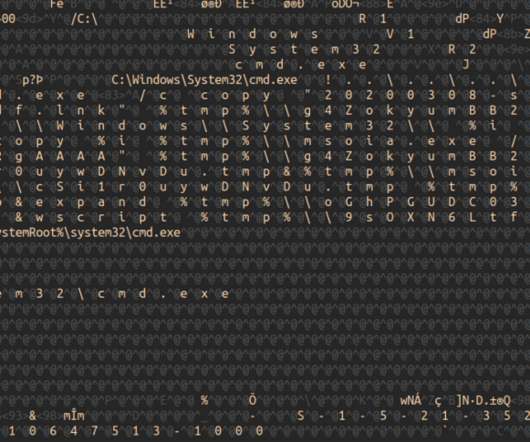
Security researcher Marco Ramilli presents a comparative analysis of attacks techniques adopted by the Iran-Linked OilRig APT group. I would define this group of references as reports. Those reports have been divided into 4 timing groups in order to simplify the evaluation process. and more personal thoughts.

























Let's personalize your content