Meet Ika & Sal: The Bulletproof Hosting Duo from Hell
Krebs on Security
JANUARY 8, 2024
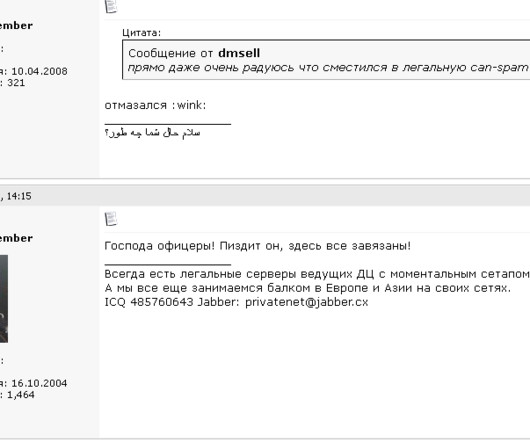
Spamit), an invite-only community for Russian-speaking people in the businesses of sending spam and building botnets of infected computers to relay said spam. ” We are glad to present you our services! From January 2005 to April 2013, there were two primary administrators of the cybercrime forum Spamdot (a.k.a



















Let's personalize your content