How to handle a ransomware attack
IBM Big Data Hub
JANUARY 22, 2024
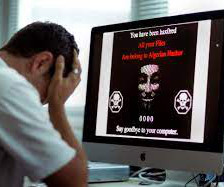
The photo will expedite the recovery process and help when filing a police report or a possible claim with your insurance company. Hackers know this might be your first instinct, and some types of ransomware notice restart attempts and cause additional harm, like damaging Windows or deleting encrypted files.




































Let's personalize your content