The Link Between AWM Proxy & the Glupteba Botnet
Krebs on Security
JUNE 28, 2022
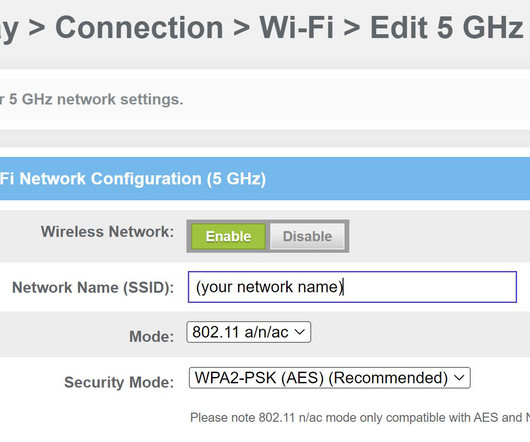
Security experts had long seen a link between Glupteba and AWM Proxy, but new research shows AWM Proxy’s founder is one of the men being sued by Google. AWMproxy, the storefront for renting access to infected PCs, circa 2011. An example of a cracked software download site distributing Glupteba. Image: Google.com.


















Let's personalize your content