Threat actors leverages DLL-SideLoading to spread Qakbot malware
Security Affairs
JULY 26, 2022
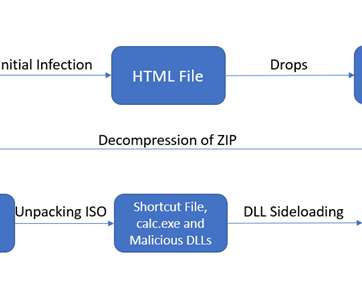
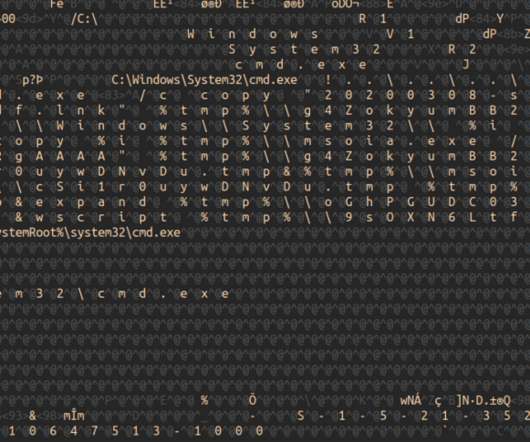
Security expert ProxyLife and Cyble researchers recently uncovered a Qakbot campaign that was leveraging the Windows 7 Calculator app for DLL side-loading attacks. Dynamic-link library (DLL) side-loading is an attack method that takes advantage of how Microsoft Windows applications handle DLL files. Pierluigi Paganini.















Let's personalize your content