Ransomware Trained on Manufacturing Firms Led Cyberattacks in Industrial Sector
Dark Reading
FEBRUARY 23, 2022
Meanwhile, a few "alarming" infiltrations of OT networks by previously unknown threat groups occurred last year as well.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
FEBRUARY 23, 2022
Meanwhile, a few "alarming" infiltrations of OT networks by previously unknown threat groups occurred last year as well.

KnowBe4
APRIL 23, 2024
Global optics manufacturer Hoya had business operations at its headquarters and several business divisions impacted and is now facing a “No Negotiation / No Discount Policy” $10 million ransom decision to make.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IT Governance
SEPTEMBER 30, 2022
UK organisations suffer the third highest rate of ransomware attacks globally, with small businesses most at risk, a report by NordLocker has found. The other most vulnerable sectors were business services (23), construction (22), manufacturing (19) and transport (18). What else should organisations do?

Security Affairs
MAY 11, 2021
The FBI and Australian Australian Cyber Security Centre (ACSC) warn of an ongoing Avaddon ransomware campaign targeting organizations worldwide. “The Australian Cyber Security Centre (ACSC) is aware an ongoing ransomware campaign utilising the Avaddon Ransomware malware. . ” reads the alert published by ACSC.
Security Affairs
MAY 10, 2020
Stadler, a Swiss manufacturer of railway rolling stock disclosed a data breach, hackers attempted to blackmail the company. International rail vehicle manufacturer, Stadler , disclosed a security breach that might have also allowed the attackers to steal company data. SecurityAffairs – hacking, ransomware). Pierluigi Paganini.

KnowBe4
OCTOBER 19, 2023
The joint guide outlines phishing techniques malicious actors commonly use and provides guidance for both network defenders and software manufacturers to reduce the impact of phishing techniques used in obtaining credentials and deploying malware. We could not agree more.
Security Affairs
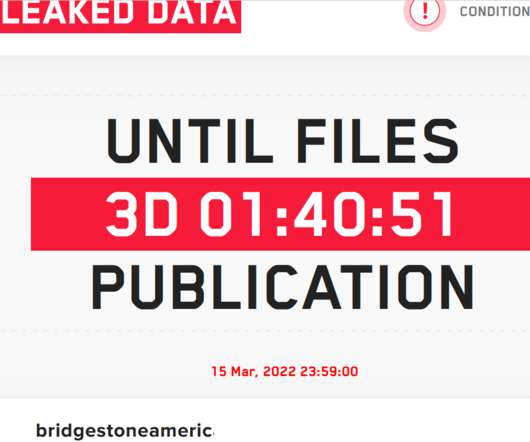
MARCH 13, 2022
LockBit ransomware gang claimed to have hacked Bridgestone Americas, one of the largest manufacturers of tires. LockBit ransomware gang claimed to have compromised the network of Bridgestone Americas, one of the largest manufacturers of tires, and stolen data from the company. Pierluigi Paganini.

Security Affairs
MARCH 19, 2022
The Federal Bureau of Investigation (FBI) reported that AvosLocker ransomware is being used in attacks targeting US critical infrastructure. The Federal Bureau of Investigation (FBI) published a joint cybersecurity advisory warning of AvosLocker ransomware attacks targeting multiple US critical infrastructure. Pierluigi Paganini.

eSecurity Planet
OCTOBER 5, 2021
Malware has been around for nearly 40 years, longer even than the World Wide Web, but ransomware is a different kind of threat, capable of crippling a company and damaging or destroying its critical data. Ransomware Protection and Recovery Steps. Ransomware removal tools. Ransomware recovery services. Data backup.

Security Affairs
SEPTEMBER 3, 2021
FBI warns ransomware gangs are actively targeting organizations in the food and agriculture sector. Small farms, large producers, processors and manufacturers, and markets and restaurants are particularly exposed to ransomware attacks. ” reads the FBI’s PIN.

Security Affairs
OCTOBER 23, 2020
French IT outsourcer Sopra Steria hit by ‘cyberattack’, Ryuk ransomware suspected. French IT outsourcer Sopra Steria has been hit by a ransomware attack, while the company did not reveal the family of malware that infected its systems, local media speculate the involvement of the Ryuk ransomware. “A
Security Affairs
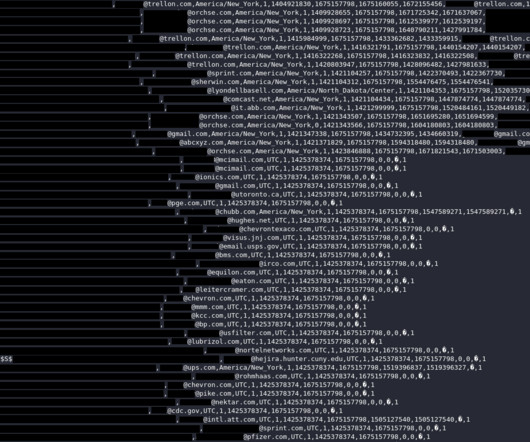
AUGUST 31, 2023
The National Safety Council (NSC) is a non-profit organization in the United States providing workplace and driving safety training. Also, the credentials could have been used to gain initial access into corporate networks to deploy ransomware, steal or sabotage internal documents, or gain access to user data.

Security Affairs
MAY 13, 2021
FBI and DHS’s CISA have published a joint alert on DarkSide ransomware activity after the disruptive attack on Colonial Pipeline. FBI and DHS’s CISA have published a joint alert to warn of ransomware attacks conducted by the DarkSide group. The group provides Ransomware-as-a-Service (RaaS) to a network of affiliates.

KnowBe4
MAY 23, 2023
CyberheistNews Vol 13 #21 | May 23rd, 2023 [Double Trouble] 78% of Ransomware Victims Face Multiple Extortions in Scary Trend New data sheds light on how likely your organization will succumb to a ransomware attack, whether you can recover your data, and what's inhibiting a proper security posture. This puts your network in jeopardy!

IT Governance
APRIL 29, 2024
Source (New) Manufacturing Taiwan Yes 4,715,133 Mustafa Centre Source 1 ; source 2 (Update) Retail Singapore Yes >3,5000,000 TRAXERO Source (New) Software USA Yes 2,634,753 Piping Rock Health Products Source 1 ; source 2 ; source 3 (New) Manufacturing USA Yes 2,103,100 FBCS, Inc.

Security Affairs
AUGUST 8, 2021
ransomware gang BlackMatter ransomware also targets VMware ESXi servers Conti ransomware affiliate leaked gang’s training material and tools Conti Leak Indicators – What to block, in your SOC…. If you want to also receive for free the international pre ss subscribe here.

Adam Levin
JUNE 30, 2020
We’re not even halfway through 2020, and already it’s been a record-breaking year for ransomware attacks. Manufacturing giant Honda had its networks brought to a standstill by just such an attack. Manufacturing giant Honda had its networks brought to a standstill by just such an attack. What can CEOs do?

IT Governance
MARCH 1, 2023
We offer a variety of resources to help understand and mitigate threats, from training courses and consultancy services to free guides. IT Governance is dedicated to helping organisations tackle the threat of cyber crime and other information security weaknesses. You can find the full list of data breaches and cyber attacks below.

The Last Watchdog
JULY 13, 2023
The data shows how perceptions around cyber and technology risks, from ransomware and other cyber-attacks to the threats posed by AI, are changing the global business risk landscape. The economic impact of cybercrime on business across the globe continues to reach new levels, with the cost predicted to reach US$10.5

IT Governance
SEPTEMBER 1, 2020
Ransomware. British Dental Association records leaked on the dark web (5,524) Australian aged care firm Regis hit by ransomware (unknown) ?Canon Cyber attacks. million) CO-based Mental Health Partners says an employee’s account was hacked (unknown) Sumitomo Forestry Co., Hitachi Chemical Co. Cyber attacks. Hitachi Chemical Co.

IT Governance
JANUARY 30, 2024
Source (New) Retail USA Yes 2,588,849 Keenan & Associates Source 1 ; source 2 (Update) Insurance USA Yes 1,509,616 AGC Group Source (New) Manufacturing Japan Yes 1.5 TB Four Hands Source (New) Manufacturing USA Yes 1.5 TB UK forex customers Source (New) Finance UK Yes 1,001,214 A.N.S. Source (New) Non-profit USA Yes 25,908.62

KnowBe4
MAY 16, 2023
Ransomware by far the leading cause of cyber insurance losses Cyber Insurer Munich Re recently released their "Cyber insurance: Risks and Trends 2023" report which provides us with some insight into the state of attacks and the impact on cyber insurance. billion in 2022 and projected to reach $33.3 billion by 2027. "3x
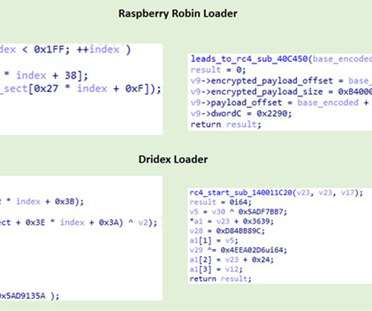
Security Affairs
SEPTEMBER 2, 2022
The malware was first spotted on September 2021, the experts observed it targeting organizations in the technology and manufacturing industries. The DEV-0206-associated FakeUpdates activity on affected systems has since led to follow-on actions resembling DEV-0243 pre-ransomware behavior.”. Search for the IOCs in your environment.

eSecurity Planet
SEPTEMBER 14, 2022
According to the 2021 IBM Threat Force Intelligence Index , Manufacturing was the industry most likely to be attacked last year, comprising 23.2% Given how lucrative and necessary both sectors are to daily life, they make prime targets for ransomware. Further reading: Best Cybersecurity Awareness Training for Employees.

eSecurity Planet
NOVEMBER 6, 2023
Other major flaws appeared in the NGINX Ingress Controller for Kubernetes, Atlassian Confluence Data Center and Server, and Apache ActiveMQ — and the latter two have already been targeted in ransomware attacks. 3 to report that the vulnerability is being actively exploited, which Rapid7 said includes ransomware attacks.

IT Governance
JANUARY 23, 2024
Source (New) Manufacturing Saudi Arabia Yes 86.16 GB JSP Pharmaceutical Manufacturing (Thailand) PCL Source (New) Manufacturing Thailand Yes >80 GB TREZOR Source (New) Crypto France Yes Nearly 66,000 Oak View Group Source (New) Leisure USA Yes 58,935 Innefu Labs Pvt.

KnowBe4
MARCH 7, 2023
New-school security awareness training teaches your employees to recognize social engineering tactics so they can avoid falling for phishing attacks. That's why training your end-users is so important. "These chats will even respond to messages if the reader chooses to participate, but these are all automated and fabricated.

Security Affairs
APRIL 13, 2019
The association promotes federal and law enforcement leadership and training located at the FBI training academy in Quantico, VA. Yesterday I wrote an article to announce the availability of a decryptor for the CryptoPokemon ransomware that was developed by EMSISOFT.

IT Governance
SEPTEMBER 4, 2018
For life sciences and pharmaceutical companies, this includes data on the development and testing of new therapies and details of how therapies are manufactured. In the 2017 WannaCry attack, for example, cyber criminals used ransomware to prevent victims from accessing their IP unless a ransom was paid. What are the threats?

eSecurity Planet
AUGUST 22, 2023
Jump ahead to: Prioritize Data Protection Document Your Response Process Make Users Part of the Process Understand Business Context Be Thorough Proactively Collect and Organize Data Don’t Forget Network Analysis Train and Drill Enlist Outside Help Go on the Offensive 1. See the Top Cybersecurity Employee Training Programs 4.
IT Governance
JANUARY 5, 2024
This real estate training and tool provider left a database containing more than 1.5 The manufacturing sector suffered an impressive 113 incidents this month, with only 6 of them originating from the supply chain. For Q4 2023 (October – December 2023), 26% of all incidents were ransomware attacks.

Data Protection Report
FEBRUARY 23, 2024
Alongside the Executive Order, the Biden administration announced a plan to invest in the domestic manufacturing of port cranes to reduce reliance on foreign-built infrastructure potentially used by nation-state and financially motivated attackers to disrupt U.S. organizations. These proposed rules are open to public comments.

Data Matters
MARCH 21, 2022
Congress has passed a significant new cybersecurity law that will require critical infrastructure entities to report material cybersecurity incidents and ransomware payments to the Cybersecurity and Infrastructure Security Agency (CISA) within 72 and 24 hours, respectively. a supply chain compromise.
eSecurity Planet
APRIL 6, 2023
Ransomware is a type of malicious program, or malware, that encrypts files, documents and images on a computer or server so that users cannot access the data. Ransomware is the most feared cybersecurity threat and with good reason: Its ability to cripple organizations by locking their data is a threat like no other.

IT Governance
DECEMBER 20, 2022
In the midst of all this, organisations across Europe reported delays as a result of alleged state-sponsored attacks – including Toyota’s Japanese plants and a kettle manufacturer in the Isle of Man. By comparison, a report published last year found that US firms pay $6 million on average in ransomware demands.

eSecurity Planet
SEPTEMBER 2, 2021
Now it may have an even more important role to play: preventing ransomware attacks. Rampant Ransomware Attacks. Ransomware attacks have been surging in 2021, with the highest-profile one the Colonial Pipeline attack that nearly shut down the U.S. Many ransomware attacks seem brutal, cruel, and deceptive. East Coast.

eSecurity Planet
AUGUST 9, 2021
Too often manufacturers prioritize releasing their products to market and interface connectivity rather than effective controls, all of which is made more difficult by the weak implementation of IoT standards, frameworks and basic security in designs. Spending on Digital Display Ads Increasing.

eSecurity Planet
SEPTEMBER 22, 2021
Ransomware is one of the fastest-growing and most destructive cyber threats today. Cybersecurity researchers largely agree that ransomware growth has been astronomical; the only question is by how much. Given how high profile ransomware attacks have become, you may be wondering if you, too, could become a target. Valuable Data.

ForAllSecure
MAY 30, 2023
Say you’re an organization that’s been hit with ransomware. At what point do you need to bring in a ransomware negotiator? Mark Lance, the VP of DFIR and Threat intelligence for GuidePoint Security, provides The Hacker Mind with stories of ransomware cases he’s handled. The same is true with ransomware.

The Last Watchdog
SEPTEMBER 20, 2019
However, at this moment in history, two particularly worrisome types of cyber attacks are cycling up and hitting local government entities hard: ransomware sieges and election tampering. population 12,046, paid $460,000, respectively, for ransomware decryption keys. Ransomware attacks are trendy again,” Weller told me. “If

eSecurity Planet
AUGUST 10, 2023
The goal of this threat intelligence community is to share useful threat information back and forth: Private sector leaders can benefit from access to FBI insider knowledge, training, and best practices, while the FBI and other governmental bodies gain additional eyes on different areas of U.S. critical infrastructure.

eSecurity Planet
FEBRUARY 16, 2021
Ransomware. Boost your organization’s IT literacy with ongoing cybersecurity training so they recognize the threats posed by malware attacks. Most device or software manufacturers place backdoors in their products intentionally and for a good reason. Email is also usually how ransomware works. Jump ahead: Adware.

The Last Watchdog
MAY 1, 2019
Related: Why diversity in training is a good thing. He came up with a new approach to testing and training the bank’s employees – and the basis for a new company, LucySecurity. People tend to be very resistant to training,” Bastable told me. How much better? But as soon as you stop, the number quickly goes back up.”

eSecurity Planet
MARCH 23, 2022
These attacks focus on financially-rewarding exploitation such as cryptojacking , botnet proliferation, business email compromise, or ransomware. For example, the Cuba ransomware gang exploited ProxyShell and ProxyLogon vulnerabilities in Windows exchange servers to plant backdoors into the exchange server and deliver additional malware.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content