NEW TECH: Circadence deploys ‘gamification’ training to shrink cybersecurity skills gap
The Last Watchdog
APRIL 22, 2019
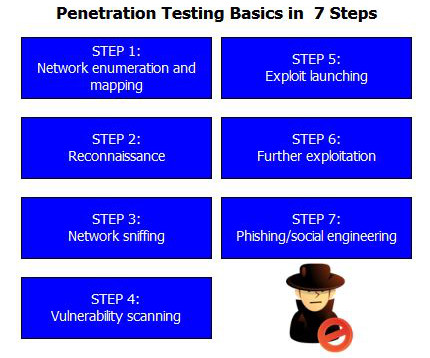
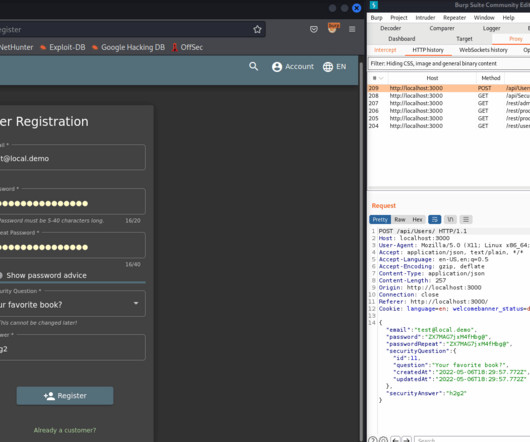
It’s clear that closing the cybersecurity skills gap has to happen in order to make our internet-centric world as private and secure as it ought to be. Related: The need for diversity in cybersecurity personnel One of the top innovators in the training space is Circadence ®. And everyone wants to be successful.













































Let's personalize your content