Fake Smart Factory Honeypot Highlights New Attack Threats
Threatpost
JANUARY 24, 2020
The honeypot demonstrates the various security concerns plaguing vulnerable industrial control systems.

Threatpost
JANUARY 24, 2020
The honeypot demonstrates the various security concerns plaguing vulnerable industrial control systems.

Security Affairs
NOVEMBER 7, 2020
At least one ransomware operator appears to have exploited the recently patched CVE-2020-14882 vulnerability affecting Oracle WebLogic. At least one ransomware operator appears is exploiting the recently patched CVE-2020-14882 vulnerability in Oracle WebLogic. ” reads the analysis published by the expert. Pierluigi Paganini.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Dark Reading
MAY 5, 2022
Cloud containers are increasingly part of the cybercrime playbook, with researchers flagging ongoing scanning for Docker weaknesses along with rapid exploitation to infect systems with coin-miners, denial-of-service tools, and ransomware.
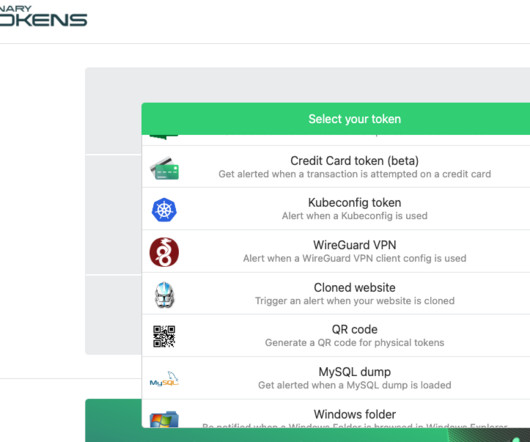
Krebs on Security
AUGUST 22, 2023
Security experts say this same tourist dynamic is a dead giveaway in virtually all computer intrusions that lead to devastating attacks like data theft and ransomware, and that more organizations should set simple virtual tripwires that sound the alarm when authorized users and devices are spotted exhibiting this behavior.

Dark Reading
JANUARY 21, 2020
A fictitious industrial company with phony employees personas, website, and PLCs sitting on a simulated factory network fooled malicious hackers - and raised alarms for at least one white-hat researcher who stumbled upon it.

Security Affairs
FEBRUARY 21, 2024
One of the honeypots used by Cado was targeted by an attack originating from the IP 103[.]79[.]118[.]221 Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – ransomware, miner) ” reads the report published by Cado Security. ” The main Migo payload (/tmp/.migo)

Security Affairs
DECEMBER 21, 2021
Uptycs researchers have observed attacks related to miners, DDOS malware and some variants of ransomware actively leveraging LogforShell flaw in log4j. So far we have observed attacks related to coinminers, DDOS malware and some variants of ransomware actively leveraging this vulnerability. Linux Ransomware.
Let's personalize your content