Fake Smart Factory Honeypot Highlights New Attack Threats
Threatpost
JANUARY 24, 2020
The honeypot demonstrates the various security concerns plaguing vulnerable industrial control systems.

Threatpost
JANUARY 24, 2020
The honeypot demonstrates the various security concerns plaguing vulnerable industrial control systems.

The Last Watchdog
MARCH 11, 2020
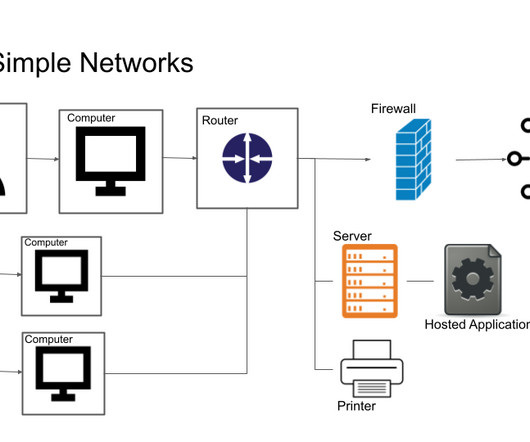
Organizations are increasingly outsourcing IT workloads to cloud service providers and looking to leverage IoT systems. To demonstrate this, Trend Micro set up a honeypot, imitating an industrial factory, to see how quickly and often it would get attacked. Speed is what digital transformation is all about.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
MARCH 16, 2023
This includes IoT devices. Sooner rather than later, you’ll want to perform an audit of your OT and IoT devices. It’s difficult to know which IoT devices are on what network, particularly if you have an extensive OT deployment. Read more about IoT security solutions for your enterprise devices. Segmentation.
eSecurity Planet
MARCH 14, 2023
The internet of things (IoT), operations technology (OT), and the industrial internet of things (IIoT) also now connect to networks. Deception technology using honeypots and similar subterfuge can trigger proactive alerts of both hackers and authorized users that might be attempting to perform malicious actions.

eSecurity Planet
APRIL 11, 2022
Decoys such as fake hosts or honeypots are hosted in a single area on-premises or in the cloud and are projected across the enterprise network, appearing as realistic local assets. Decoys mimic hosts running operating systems as well as IoT (Internet of Things) hosts. It can find signs of ransomware, even in encrypted files.

eSecurity Planet
MARCH 22, 2023
Two-Factor Authentication (2FA) : In today’s ransomware-riddled environment, two-factor authentication should also be considered a minimum requirement for all forms of remote access. IoT devices such as security cameras, temperature sensors, or heat monitors will be added to networks and often possess security flaws.

eSecurity Planet
APRIL 26, 2024
Endpoint: Enables access for human users and computer services and commonly includes PCs, laptops, Internet of Things (IoT), and operational technology (OT). Internet of Things (IoT) security: Encompasses a variety of tools and techniques to secure IoT, operations technology (OT), and other similar categories of endpoints.
Let's personalize your content