Panasonic Warns That IoT Malware Attack Cycles Are Accelerating
WIRED Threat Level
AUGUST 9, 2023
The legacy electronics manufacturer is creating IoT honeypots with its products to catch real-world threats and patch vulnerabilities in-house.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

WIRED Threat Level
AUGUST 9, 2023
The legacy electronics manufacturer is creating IoT honeypots with its products to catch real-world threats and patch vulnerabilities in-house.

Threatpost
JANUARY 24, 2020
The honeypot demonstrates the various security concerns plaguing vulnerable industrial control systems.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
SEPTEMBER 19, 2018
Security experts from Kaspersky have published an interesting report on the new trends in the IoT threat landscape. What is infecting IoT devices and how? The researchers set up a honeypot to collect data on infected IoT devices, the way threat actors infect IoT devices and what families of malware are involved.

Threatpost
SEPTEMBER 18, 2018
A honeypot set up to sniff out data on infected IoT devices found a broad array of compromised devices – from Mikrotik routers to dishwashers.

Security Affairs
NOVEMBER 12, 2018
The author of an IoT botnet is distributing a backdoor script for ZTE routers that also includes his own backdoor to hack script kiddies. A weaponized IoT exploit script is being used by script kiddies, making use of a vendor backdoor account to hack the ZTE routers. Backdooring rival IoT botnet operator can have several purposes.

Security Affairs
SEPTEMBER 2, 2019
Akamai researcher Larry Cashdollar reported that a cryptocurrency miner that previously hit only Arm-powered IoT devices it now targeting Intel systems. The researchers revealed that one of his honeypots was hit by this IoT malware that targets Intel machines running Linux. “This one seems to target enterprise systems.”

Dark Reading
DECEMBER 19, 2018
While you prepare your defenses against the next big thing, also pay attention to the longstanding threats that the industry still hasn't put to rest.
Security Affairs
NOVEMBER 19, 2020
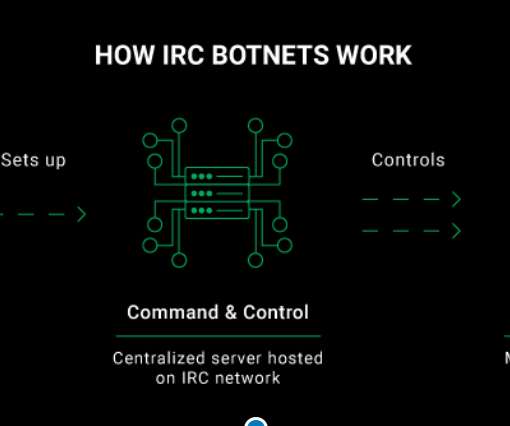
To conduct this investigation, a CyberNews researcher infiltrated an IRC botnet that we captured in one of our honeypots. Our honeypot setup. In cybersecurity terms, a honeypot is a decoy service or system that poses as a target for malicious actors. Here’s how it all happened. About this investigation.

Security Affairs
OCTOBER 23, 2018
Security experts from Sophos Labs have spotted a new piece of IoT malware tracked as Chalubo that is attempting to recruit devices into a botnet used to launch DDoS attacks. These types of simple attacks on our honeypots are quite common, but what made this stand out was the libsdes sample.” ” continues the analysis.

Security Affairs
NOVEMBER 5, 2018
“The group distributes the bot by exploiting a common command injection vulnerability on internet of things (IoT) devices and Linux servers. The post Shellbot Botnet Targets IoT devices and Linux servers appeared first on Security Affairs. ” reads the analysis published by TrendMicro. Pierluigi Paganini.

Security Affairs
NOVEMBER 26, 2021
Below is the video PoC of the zero-day exploitation: According to Resecurity, the vulnerability was identified by the cause of abnormal traffic monitoring which consisted of a network of “honeypot” sensors to emulate common IoT devices developed by Resecurity are to hunt for malice on the internet.
Security Affairs
DECEMBER 17, 2023
Similar to the initial two zero-days, the compromised devices could exploit OS command injection vulnerabilities in NTP settings on the affected Internet of Things (IoT) and NVR devices. “Once again, our custom honeypot network deployment has provided valuable insights into cyberattacks, revealing previously unknown vulnerabilities.

Security Affairs
NOVEMBER 21, 2018
Netscout observed tens of thousands of exploit attempts daily targeting it honeypots, in November attackers attempted to deliver some 225 unique malicious payloads exploiting the Hadoop YARN vulnerability. These versions of Mirai behave much like the original but are tailored to run on Linux servers and not underpowered IoT devices.”

The Security Ledger
JULY 3, 2019
In this week’s podcast episode, #152: we talk with Akamai researcher Larry Cashdollar about his discovery of Silex, a new example of IoT killing malware allegedly authored by a 14 year old. Buried in a binary file that turned up in his honeypot was an apologetic message from an unknown malware author for hacking and then bricking his device.
Security Affairs
JANUARY 21, 2020
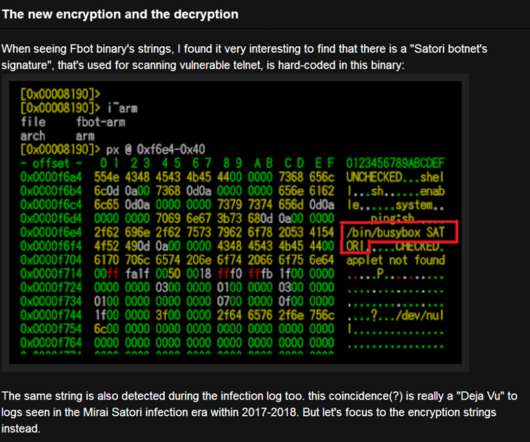
This is not the first time Fbot analysis has been published, and also Fbot binaries have been actively infecting the IoT devices since way before 2018. This wave is a significant timeline as a technology step-up for DDoS botnet and IoT malware development. And will discuss the mysteries that can be seen after Fbot has been detected.
Security Affairs
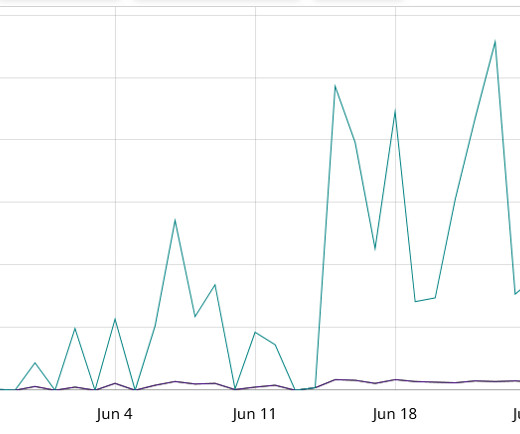
JULY 22, 2023
Internet-wide sweeps seen by over 700 of our IKEv2 aware honeypot sensors, since May 26th. “Targeting vulnerable devices has always been a primary objective for threat actors, and the prevalence of remote code execution attacks poses a major concern for IoT devices and Linux servers. ” concludes the report.

Security Affairs
NOVEMBER 21, 2019
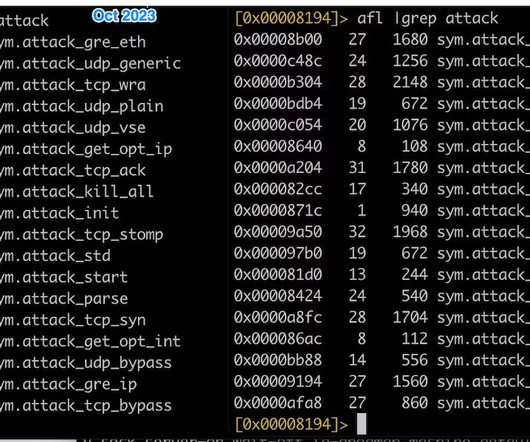
In October one of the honeypots of the company captured the bot, its downloader , and some bot modules. “Fast forwarded to October 11, 2019, our Anglerfish honeypot captured another suspicious ELF sample, and it turned out to be the Downloader of the previous suspicious ELF sample.”

Security Affairs
DECEMBER 23, 2018
An attacker could use IoT search engines such as ZoomEye or Shodan to scan the internet for devices having default passwords. This information could be used by attackers to query IoT search engines and retrieve a list of devices and associated login. “CVE-2018–7900 makes the process of attacking a router even more simplified.

Thales Cloud Protection & Licensing
FEBRUARY 28, 2022
This honeypot of information puts manufacturers at major risk from cyber attacks. Understand how to deploy innovations such as digital car keys, Over-the-Air communications or the cloud while protecting sensitive data, IoT devices and implementing secure manufacturing. Data security.

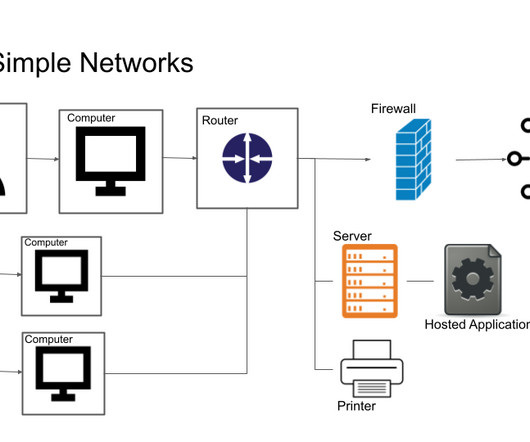
The Last Watchdog
MARCH 11, 2020
Organizations are increasingly outsourcing IT workloads to cloud service providers and looking to leverage IoT systems. To demonstrate this, Trend Micro set up a honeypot, imitating an industrial factory, to see how quickly and often it would get attacked. Speed is what digital transformation is all about.

Security Affairs
DECEMBER 25, 2018
Experts at Bad Packets observed a scan targeting their honeypot, further investigation allowed them to discover that they were leaking the local network access details. “On Friday, December 21, 2018, our honeypots observed an interesting scan consisting of a GET request for /get_getnetworkconf.cgi.

Security Affairs
JUNE 22, 2019
In September 2018, researchers observed the Hide and Seek (HNS) IoT botnet targeting Android devices with ADB option enabled. The malicious code attempt to determine if it is running in a honeypot , then it downloads the payload and changes its permission settings to allow its execution. The script for a.

Threatpost
MAY 17, 2018
Deception technology is an emerging category of cyber defense that is particularly useful when it comes to IoT devices, SCADA systems and medical devices.

Security Affairs
APRIL 6, 2019
“Over the last three months, our honeypots have detected DNS hijacking attacks targeting various types of consumer routers.” They've also detected additional rogue DNS servers: 195.128.124.150 ( ) 195.128.124.181 ( ) — Bad Packets Report (@bad_packets) April 5, 2019. ” reads the report published by Bad Packets.

Security Affairs
SEPTEMBER 30, 2019
After 2 years of waiting, MalwareMustDie returns with an excellent page of malware analysis of a new IoT malware: Linux/AirDropBot. The beginning of the story: another IoT malware in the wild? Coming to the core topic: IoT botnet threat and their ecosystem.

Thales Cloud Protection & Licensing
JUNE 12, 2018
Because behavioral biometric data can contain confidential and personal information, and reveal sensitive insight, it can also be a high value target and represent a honeypot for attackers. With such a high adoption rate, big data is already transforming many areas of business, including identity management at the individual and device level.

Elie
DECEMBER 2, 2017
What’s remarkable about these record-breaking attacks is they were carried out via small, innocuous Internet-of-Things (IoT) devices like home routers, air-quality monitors, and personal surveillance cameras. At its peak, Mirai enslaved over 600,000 vulnerable IoT devices, according to our measurements. self-propagating worm.
Security Affairs
APRIL 28, 2020
The Outlaw Botnet uses brute force and SSH exploit (exploit Shellshock Flaw and Drupalgeddon2 vulnerability ) to achieve remote access to the target systems, including server and IoT devices. The first version spotted by TrendMicro includes a DDoS script that could be used by botmaster to set-up DDoS for-hire service offered on the dark web.

eSecurity Planet
MARCH 16, 2023
This includes IoT devices. Sooner rather than later, you’ll want to perform an audit of your OT and IoT devices. It’s difficult to know which IoT devices are on what network, particularly if you have an extensive OT deployment. Read more about IoT security solutions for your enterprise devices. Segmentation.
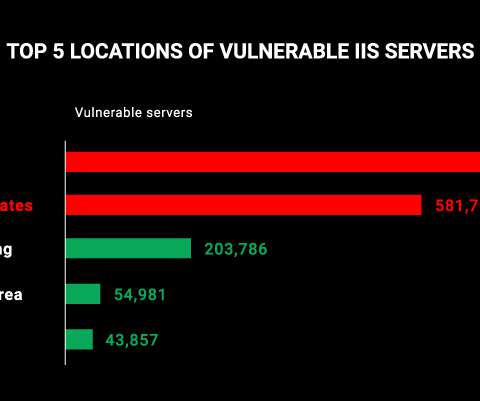
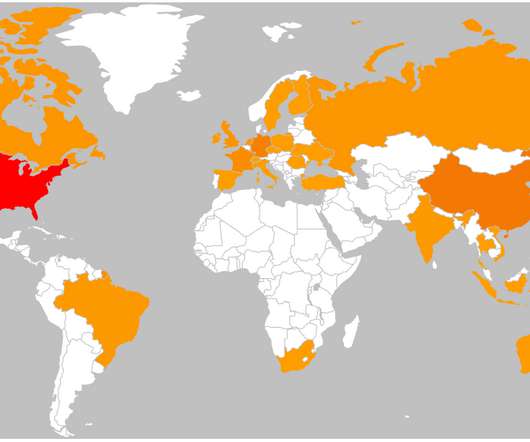
Security Affairs
SEPTEMBER 9, 2021
We then used an IoT search engine to look for open unpatched IIS web servers that were susceptible to known CVEs and investigated the results for statistical data. From the initial results, we filtered out honeypots, which are decoy services or systems set up by security teams and researchers as bait for threat actors.

eSecurity Planet
APRIL 11, 2022
Decoys such as fake hosts or honeypots are hosted in a single area on-premises or in the cloud and are projected across the enterprise network, appearing as realistic local assets. Decoys mimic hosts running operating systems as well as IoT (Internet of Things) hosts. The solution offers support for IT, OT, IoT, SCADA, ICS, and SWIFT.

Security Affairs
MAY 16, 2019
Let’s also include all information by the IOT devices that are connected online by that that cannot be accessed for obvious reasons. The dark web is full of honeypots. It is also impossible to determine the diffusion of honeypots. Or is the Dark Web itself a honeypot for criminals, anarchists, terrorists and.

eSecurity Planet
JULY 28, 2021
For modern networks, the introduction of new endpoints – be it remote laptops for personnel or client IoT devices – is a roadblock being actively addressed. Decentralized data storage that removes the need for a honeypot. Types of Endpoints Matter. Distributed PKI and multi-signature login capabilities. Block Armour.

eSecurity Planet
MARCH 22, 2023
Some applications, cloud infrastructure, networking equipment, or Internet of Things (IoT) devices may require more sophisticated ITAM or additional tools to detect them. IoT devices such as security cameras, temperature sensors, or heat monitors will be added to networks and often possess security flaws.
eSecurity Planet
MARCH 14, 2023
The internet of things (IoT), operations technology (OT), and the industrial internet of things (IIoT) also now connect to networks. Deception technology using honeypots and similar subterfuge can trigger proactive alerts of both hackers and authorized users that might be attempting to perform malicious actions.

eSecurity Planet
MARCH 17, 2023
These tools support data streamlining and filtering across network technologies and applications, consolidating and uniting data evidence across IoT devices, mobile devices, email and SaaS applications, and other endpoints. With DFS, relevant data can quickly be sorted through and brought to light for investigative purposes.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content