Security Affairs newsletter Round 460 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.

Data Protection Report
OCTOBER 3, 2021
Connecticut’s amended statute follows the course of many other states in deeming as compliant with the statute any person who is subject to and in compliance with the Health Insurance Portability and Accountability Act (“HIPAA”) and the Health Information Technology for Economic and Clinical Health Act (“HITECH”). 1] [link]. [2] 2] C.R.S. §
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JULY 30, 2018
DataLocker honed its patented approach to manufacturing encrypted portable drives and landed some key military and government clients early on; the company has continued branching out ever since. DataLocker actually got traction, early on, selling to the military. Related: How DataLocker got its start h. Park: Exactly.
IT Governance
NOVEMBER 1, 2022
Mexico confirms hack of military records (unknown) Randolph-area school district disables its own website following transphobic hack (unknown) Australia’s Telstra hit by data breach, two weeks after attack on Optus (unknown) Patient details compromised in cyber attack on health provider Pinnacle (unknown) CHI Health faces ‘IT security incident’ impacting (..)

Security Affairs
AUGUST 17, 2021
“Total number of persons affected (including residents): 5,810” Exposed data includes names, birth dates, contact information, driver’s license information, Social Security numbers, government-issued ID (such as military ID and tax ID), and health-related information (including health insurance information).

ARMA International
JANUARY 30, 2020
On December 23, Yahoo News [1] reported on a Department of Defense memo [2] warning military personnel that using direct-to-consumer (DTC) DNA testing could pose “personal and operational risks.” In other words, the Pentagon is concerned about hostile entities using such biometric data to better surveil and track the military.

Information Governance Perspectives
APRIL 5, 2023
John Danenberger, CPCU, is Corporate Counsel at State Farm Insurance and specializes in addressing emerging issues around telematics. In 2015, he successfully transitioned from a military career as a trial attorney for the JAG Corps to working in telematics in corporate America for State Farm Insurance.

IT Governance
AUGUST 3, 2020
Canadian insurer Heartland Farm Mutual says an employee’s email account breached (unknown). Brazilian health insurer Hapvida discloses cyber attack (unknown). Four military schools in Canada targeted in ‘mysterious’ cyber attack (unknown). Western Australia government hacked, with COVID-19 communications intercepted (unknown).

Schneier on Security
FEBRUARY 28, 2024
In the first week of January, the pharmaceutical giant Merck quietly settled its years-long lawsuit over whether or not its property and casualty insurers would cover a $700 million claim filed after the devastating NotPetya cyberattack in 2017. The 9/11 attacks cost insurers and reinsurers $47 billion. 11, 2001, terrorist attacks.

Hunton Privacy
AUGUST 2, 2021
The safe harbor also applies in cases where the cybersecurity program conforms to applicable state or federal security laws and regulations ( e.g. , the security requirements of the Health Insurance Portability and Accountability Act and the Gramm-Leach Bliley Act). Cybersecurity Safe Harbor (HB 6607).

IT Governance
MARCH 1, 2022
First, Russia targeted banks and government departments, then Ukraine hit back, attacking the Moscow stock exchange. You can find out more about the cyber security implications of the Ukraine by registering for our special presentation hosted by IT Governance’s founder and executive chairman, Alan Calder.

IT Governance
JULY 1, 2021
If you find yourself facing a cyber security disaster, IT Governance is here to help. We found a comparatively low 9,780,931 breached records from publicly disclosed security incidents in June 2021. But don’t be fooled by that number – it comes from 106 incidents, which is roughly average for the year. million drivers’ details (3.3

IT Governance
SEPTEMBER 1, 2020
There were a massive 99 data breaches and cyber attacks in August, making it the third-biggest monthly total of the year by number of security incidents. But, by contrast, only 36,673,575 records were confirmed to have been leaked, which is the fewest we’ve recorded since May 2018. Cyber attacks. Hitachi Chemical Co. Cyber attacks. Data breaches.

eSecurity Planet
MARCH 3, 2023
The first is to rebalance responsibility for cybersecurity away from individuals, small businesses and local governments, and towards “the owners and operators of the systems that hold our data and make our society function, as well as of the technology providers that build and service these systems.”

IT Governance
FEBRUARY 14, 2024
Compromised data includes policyholders’ and their families’ civil status, dates of birth and social security numbers, as well as the name of their health insurer and information relating to their contracts. Compromised data included names, ID card numbers, phone numbers, emails, salaries and personal photographs.

KnowBe4
MARCH 28, 2023
"A leader tasked with cybersecurity can get ahead of the game by understanding where we are in the story of machine learning (ML) as a hacking tool," Tyson writes. "At At present, the most important area of relevance around AI for cybersecurity is content generation. Remember: Culture eats strategy for breakfast and is always top-down.

Krebs on Security
SEPTEMBER 21, 2018
In addition, the law requires the big three bureaus to offer free electronic credit monitoring services to all active duty military personnel. It is now free in every U.S. But it also includes a silver lining. Today, those fees no longer exist. view your credit file).

IT Governance
JUNE 27, 2019
The ransomware was accompanied by a note: “Your files are encrypted with the strongest military algorithms. Cyber security experts and governments urge victims to never pay the ransom. Earlier this month, Norsk Hydro published its first quarterly report since it fell victim to a devastating ransomware attack in March.

eSecurity Planet
OCTOBER 5, 2021
Malware has been around for nearly 40 years, longer even than the World Wide Web, but ransomware is a different kind of threat, capable of crippling a company and damaging or destroying its critical data. And the threat is growing. No sector has been spared from its ravages. Ransomware recovery services. Respond fast to new security threats.

DLA Piper Privacy Matters
JUNE 4, 2021
China is a leading marketing for connected and autonomous vehicles, and use and analytics of connected vehicle data has been encouraged by Chinese Government support of big data and AI technology. valid contact information for the person/role responsible for handling data subject rights; express consent must be obtained.
Hunton Privacy
JUNE 22, 2020
heath records or records of a wellness program or similar program of health promotion or disease prevention, a health care professional’s medical diagnosis or treatment of the consumer or a health insurance policy number. The law is enforceable by the Vermont Attorney General.

ForAllSecure
MAY 17, 2023
Chris Gray of Deep Watch talks about the view from the inside of a virtual SOC, the ability to see threats against a large number of SMB organizations, and the changes to cyber insurance we’re seeing as a result. VAMOSI: Something has changed in the last five years, and demonstrably so. And why is that?

The Security Ledger
AUGUST 1, 2019
» Related Stories Israeli Group Exploited WhatsApp to Spy on Users Episode 158: How NotPetya has Insurers grappling with Systemic Cyber Risk Episode 149: How Real is the Huawei Risk? Also: Adam Meyers of CrowdStrike joins us to talk about that company's first ever report on mobile malware, which is. Read the whole entry. »

Hunton Privacy
JUNE 14, 2018
Attorney General Notification: If an entity must notify Colorado residents of a data breach, and reasonably believes that the breach has affected 500 or more residents, it must also provide notice to the Colorado Attorney General.

eSecurity Planet
FEBRUARY 16, 2021
The internet is fraught with peril these days, but nothing strikes more fear into users and IT security pros than the threat of ransomware. A ransomware attack is about as bad as a cyber attack can get. Here, then, is a comprehensive look at ransomware, what it is, how to prevent it, and what to do if you become one of its unfortunate victims.

Thales Cloud Protection & Licensing
FEBRUARY 15, 2018
Affecting big companies and small in virtually every vertical and hitting government institutions at the local, state and federal level, sensitive data is routinely exfiltrated, stolen and leveraged with shocking regularity. It’s sarcastic, it’s comical, but it’s also real. Barely a day goes by where we don’t hear of a data breach.

Krebs on Security
SEPTEMBER 10, 2018
There are dozens of private companies that specialize in providing consumer credit reports and scores to specific industries, including real estate brokers, landlords, insurers, debt buyers, employers, banks, casinos and retail stores. If that accurately describes your views on the matter, this post may well change your mind. citizens.
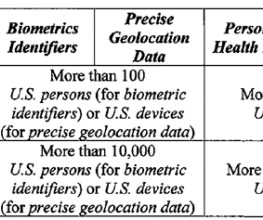
Data Protection Report
MARCH 7, 2024
The proposed definition of “listed identifier” is Full or truncated government identification or account number (such as a Social Security Number, driver’s license or state identification number, passport number, or Alien Registration Number) [Note that this definition apparently includes truncated Social Security Numbers.]

IT Governance
APRIL 9, 2024
Other databases contained health insurance data, such as patents’ names, dates of birth, addresses and medical data. Cybernews has now discovered that the company has, once again, exposed highly sensitive children’s data because of configuration errors. The company is yet to comment. EyeCare Services Partners exposes more 3.5

Security Affairs
NOVEMBER 29, 2019
According to Group-IB’s experts, the most frustrating trend of 2019 was the use of cyberweapons in military operations. As for 2019, it has become the year of covert military operations in cyberspace. The threat actor mainly targets insurance, consulting, and construction companies.

KnowBe4
MAY 9, 2023
The payload is a cryptojacking Monero miner. A cryptojacker is bad enough since it will drain power and degrade device performance. This one also carries the potential for compromising sensitive information, particularly credentials, and serving as staging for further attacks. This campaign may be more effective for its routine, innocent look.

Krebs on Security
DECEMBER 29, 2022
One of those is Mark Sokolovsky , a 26-year-old Ukrainian man who operated the popular “ Raccoon ” malware-as-a-service offering; Sokolovsky was busted in March after fleeing Ukraine’s mandatory military service orders. A single bitcoin is trading at around $45,000.
Krebs on Security
DECEMBER 13, 2021
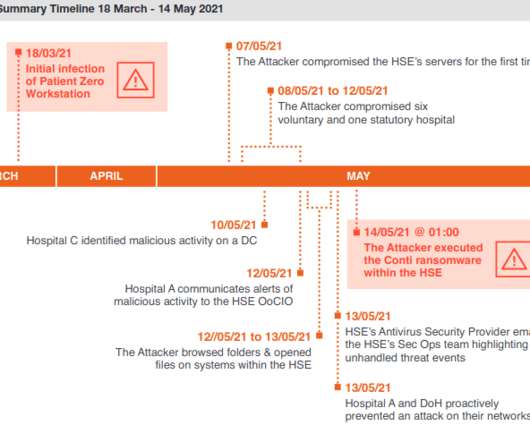
The HSE ultimately enlisted members of the Irish military to bring in laptops and PCs to help restore computer systems by hand. The unusually candid post-mortem found that nearly two months elapsed between the initial intrusion and the launching of the ransomware. By then it was too late.

IT Governance
AUGUST 1, 2023
IT Governance found 87 publicly disclosed security incidents in June 2023, accounting for 146,290,598 breached records. You can find the full list below, divided into four categories: cyber attacks, ransomware, data breaches, and malicious insiders and miscellaneous incidents.

IT Governance
APRIL 22, 2024
million records from World-Check, a screening database used to screen potential customers for links to illegal activity and government sanctions. Publicly disclosed data breaches and cyber attacks: in the spotlight Criminal hackers threaten to leak World-Check screening database A criminal group known as GhostR claims to have stolen 5.3

IT Governance
MARCH 11, 2024
We also found 14 organisations providing a significant update on a previously disclosed incident. Organisation(s) Sector Location Data breached? Source 1 ; source 2 (Update) IT services Taiwan Yes 2,451,197 RMH Franchise Corporation Source (New) Hospitality USA Yes 1.5 TB Paysign, Inc. TB Paysign, Inc.

IT Governance
JANUARY 23, 2024
VF Corporation confirms 35.5 million customers’ data. Data breached: 35,500,000 records. O’Hara & Sons, Inc.

IT Governance
MARCH 28, 2019
There’s a new compiler at the helm of our monthly list of data breaches, following the departure of IT Governance stalwart Lewis Morgan, who leaves me with some mighty big shoes to fill. Chinese hackers target universities in pursuit of maritime military secrets (unknown). Chinese government website shut down by ransomware (unknown).

Collibra
NOVEMBER 2, 2020
Characteristics of protected classifications under California or federal law such as race, ancestry, national origin, religion, age, mental and physical disability, sex, sexual orientation, gender identity, medical condition, genetic information, marital status, or military status. What is personal information? Biometric information.

ForAllSecure
JANUARY 19, 2022
For example, here’s Jerry Lewis in a scene from a 1950s film, where he’s trying to break into a Nazi German military base. One of the eight required domains in the current CISSP certification process is Identity and Access Management, or IAM. Fact is, we’ve long had passwords as a credential. Lewis: Good. Other: Wait.

Data Matters
APRIL 23, 2018
Increasingly, thought leaders, professional organizations, and government agencies are beginning to provide answers. Creating an enterprise-wide governance structure. More and more, directors are viewing cyber-risk under the broader umbrella of corporate strategy and searching for ways to help mitigate that risk.

KnowBe4
JUNE 6, 2023
China's People's Liberation Army (PLA) is increasingly focused on "Cognitive Warfare," a term referring to artificial intelligence (AI)-enabled military systems and operational concepts. This involves influencing the thinking of decision-makers, military commanders, and the general public in rival countries.
IT Governance
SEPTEMBER 6, 2023
IT Governance found 73 publicly disclosed security incidents in August 2023, accounting for 79,729,271 breached records. You can find the full list below, divided into four categories: cyber attacks, ransomware, data breaches, and malicious insiders and miscellaneous incidents.

The Last Watchdog
JUNE 1, 2020
The basic notion is that in today’s complex operating environment, it is important for businesses to proactively identify operational hazards and have a plan in place to account for them. I had the chance to drill down on this with Clinton. We had a most lively discussion. Here are excerpts, edited for clarity and length.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content