Designing Tabletop Exercises That Actually Thwart Attacks
Dark Reading
APRIL 4, 2023
Have you ever wondered how they design blue team exercises? One ransomware and cyber extortion simulation demonstrates the best practices.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
APRIL 4, 2023
Have you ever wondered how they design blue team exercises? One ransomware and cyber extortion simulation demonstrates the best practices.
Security Affairs
OCTOBER 13, 2023
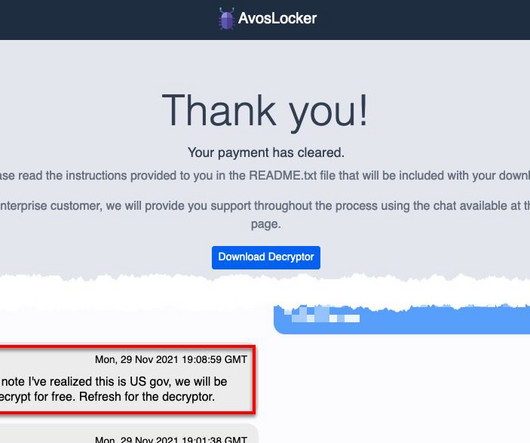
FBI and CISA published a joint Cybersecurity Advisory (CSA) to disseminate IOCs, TTPs, and detection methods associated with AvosLocker ransomware. The joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort aimed at sharing technical details associated with various ransomware operations.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
DECEMBER 13, 2023
A Joint Committee on the National Security Strategy (JCNSS) warns of the high risk of a catastrophic ransomware attack on the UK government. The British government is accused of failing to mitigate the risk of ransomware attacks. Beckett recommends the UK government consider defense from ransomware attacks a top political priority. “in

The Last Watchdog
APRIL 11, 2022
From financial institutions to meat producers, it seems every industry has been impacted by ransomware in the past year — maybe even the past week. Related: Tech solutions alone can’t stop ransomware. Put simply, ransomware attacks are on the rise because of profits. Why the stark increase? Low cost attacks.

Krebs on Security
JULY 19, 2021
Browse the comments on virtually any story about a ransomware attack and you will almost surely encounter the view that the victim organization could have avoided paying their extortionists if only they’d had proper data backups. That’s why tabletop exercises are incredibly important.

KnowBe4
JUNE 1, 2022
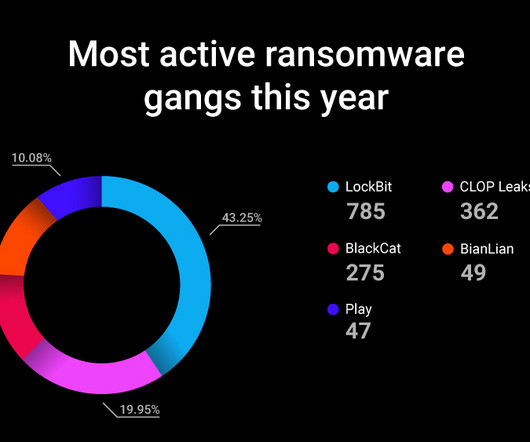
The rise of Ransomware-as-a-Service has given rise to a number of more successful groups who have their “business” down to a simple exercise of playing the numbers.

Dark Reading
JULY 19, 2023
The ransomware-as-a-service offering was first assumed to be a red-team exercise before being detected for true malicious activity.
Security Affairs
OCTOBER 17, 2023
What is the impact of ransomware on organizations? Based on Ransomlooker, a free Cybernews tool for monitoring the dark web and other hidden areas of the internet, 64% of organizations have already suffered from a ransomware attack. One employee’s mistake can cost a company millions of dollars.

Security Affairs
NOVEMBER 22, 2021
US CISA and the FBI issued a joint alert to warn critical infrastructure partners and public/private organizations of ransomware attacks during holidays. The Cybersecurity and Infrastructure Security Agency (CISA) and the FBI warn critical infrastructure partners of ransomware attacks during the holiday season. Pierluigi Paganini.

Security Affairs
DECEMBER 5, 2021
German BSI warns of ransomware attacks over the Christmas and end-of-year holidays, fearing Emotet return and attacks on Microsoft Exchange servers. The German cybersecurity authority BSI warns of ransomware attacks over the Christmas holidays, fearing the return of the Emotet botnet return. ” reads the BSI’s alert.

Security Affairs
AUGUST 21, 2021
The US Cybersecurity and Infrastructure Security Agency (CISA) released guidance on how to prevent data breaches resulting from ransomware attacks. Over the past several years, government agencies and its partners have responded to a significant number of ransomware attacks, including recent attacks against Colonial Pipeline and and U.S.

Thales Cloud Protection & Licensing
JUNE 14, 2022
Ransomware – To Pay, or Not to Pay? And when thinking about criminal innovation, ransomware attacks clearly fall into that definition of “disruptive”, especially for any business on the receiving end of that “innovation”. While ransomware attacks are not new, they remained largely underreported in the mainstream media for many years.
eSecurity Planet
JUNE 30, 2021
Virtual machines are becoming an increasingly popular avenue cybercriminals are taking to distribute their ransomware payloads onto compromised corporate networks. In order to avoid raising suspicions or triggering antivirus software , the ransomware payload will ‘hide’ within a VM while encrypting files on the host computer.”
Hunton Privacy
JULY 12, 2021
On June 30, 2021, the New York State Department of Financial Services (“NYDFS,” the “Department”) issued guidance to all New York state regulated entities on ransomware (the “Guidance”), identifying controls it expects regulated companies to implement whenever possible.

Security Affairs
OCTOBER 8, 2021
The Dutch government will not tolerate ransomware attacks that could threaten national security, it will use intelligence or military services to curb them. “For several years, the threat of ransomware attacks has been increasing around the world.

Security Affairs
FEBRUARY 12, 2022
CISA, FBI and NSA published a joint advisory warning of ransomware attacks targeting critical infrastructure organizations. and Australia have published a joint advisory warning of an increased globalised threat of ransomware worldwide in 2021. Cybersecurity agencies from the U.K., ” reads the joint advisory.

The Last Watchdog
AUGUST 1, 2023
To highlight ransomware precursors and how the attacks evade common cyber defenses, Lumu has also released an update to its 2023 Ransomware Flashcard.

The Last Watchdog
JANUARY 31, 2019
A report co-sponsored by Lloyd’s of London paints a chilling scenario for how a worldwide cyberattack could trigger economic losses of some $200 billion for companies and government agencies ill-equipped to deflect a very plausible ransomware attack designed to sweep across the globe. Related: U.S. cyber foes exploit government shutdown.

Thales Cloud Protection & Licensing
NOVEMBER 24, 2020
Mitigating Ransomware Attacks – Decoupling Encryption Keys From Encrypted Data. While ransomware attacks have been around for decades, their frequency has exponentially increased in the last few years, let alone the past several months during the pandemic. The potency of a ransomware attack lies in its diabolical ingenuity.
Security Affairs
JANUARY 13, 2024
Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

Adam Levin
FEBRUARY 24, 2020
Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory following a ransomware attack on a natural gas compression facility. The threat actor then deployed commodity ransomware…on both networks,” adding that the facility was out of commission for two days. .

Security Affairs
DECEMBER 17, 2023
CISA and ENISA enhance their Cooperation CISA adds Qlik bugs to exploited vulnerabilities catalog Report: 2.6 CISA and ENISA enhance their Cooperation CISA adds Qlik bugs to exploited vulnerabilities catalog Report: 2.6
Hunton Privacy
FEBRUARY 2, 2022
Attorney General Weiser also announced that, by this fall, his office will exercise its new rulemaking authority under the CPA to post a formal Notice of Proposed Rulemaking, including a proposed set of model rules. Lastly, it will examine the degree to which the company vets and monitors its vendors’ data security practices.
Thales Cloud Protection & Licensing
OCTOBER 23, 2023
However, simple actions like adopting multi-factor authentication (MFA) or encrypting sensitive data everywhere should be exercised throughout the year and not just during that month. Reducing the risk of attacks such as ransomware and malware on CNI will be paramount to the stability of national economies for the years to come.

eSecurity Planet
FEBRUARY 26, 2024
Furthermore, threat actors use the authentication bypass issue to spread LockBit ransomware on infiltrated networks, specifically targeting vulnerable ScreenConnect servers. The problem: LockBit ransomware, formerly known as “ABCD” ransomware, has gained traction in recent months as a separate threat in the extortion tool market.
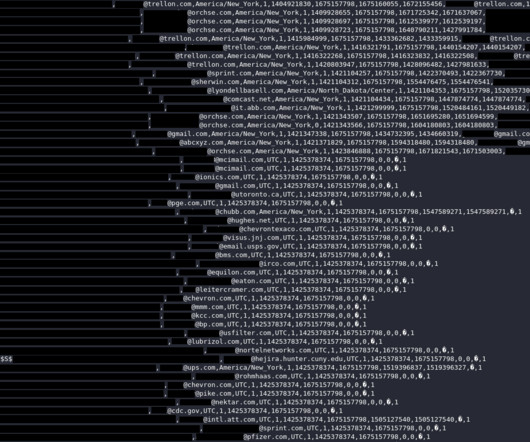
Security Affairs
AUGUST 31, 2023
Also, the credentials could have been used to gain initial access into corporate networks to deploy ransomware, steal or sabotage internal documents, or gain access to user data. It’s advisable for them to externally verify the information contained in emails and exercise caution when clicking links or opening attachments.

The Last Watchdog
OCTOBER 9, 2019
That’s the dilemma hundreds of organizations caught in the continuing surge of crippling ransomware attacks have faced. Related: How ransomware became such a scourge The FBI discourages it, as you might have guessed. That pay or not to pay debate aside, there’s a more central question raised by the ransomware plague.
Security Affairs
FEBRUARY 26, 2023
If you want to also receive for free the newsletter with the international press subscribe here.

Thales Cloud Protection & Licensing
MARCH 29, 2023
Exercising the principle of least privilege is always recommended: every user, app, program, and device should be able to access only the areas and data that are necessary for their function. Backup Data Backing up your data is the number one most effective method of protecting against ransomware, by a long shot.

Hunton Privacy
NOVEMBER 23, 2022
The proposed amendments provides three new cybersecurity events that Covered Entities must report to NYDFS via the NYDFS online cybersecurity portal within 72 hours: Unauthorized access to privileged accounts; Deployment of ransomware within a material part of the Covered Entity’s systems; and.
Security Affairs
MAY 6, 2023
Twitter confirmed that a security incident publicly exposed Circle tweets FBI seized other domains used by the shadow eBook library Z-Library WordPress Advanced Custom Fields plugin XSS exposes +2M sites to attacks Fortinet fixed two severe issues in FortiADC and FortiOS Pro-Russia group NoName took down multiple France sites, including the French (..)
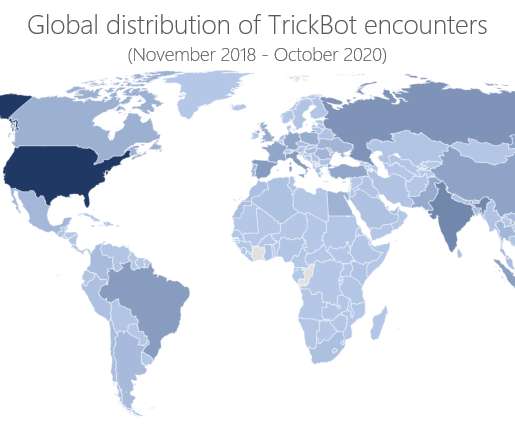
Security Affairs
SEPTEMBER 6, 2021
Threat actors leverage the botnet to distribute a broad range of malware including info-stealer and ransomware such as Conti and Ryuk. “If you send him to the United States, it will be very difficult to exercise your right of defense and there is a high possibility that you will be subjected to excessive punishment.”

eSecurity Planet
NOVEMBER 6, 2023
Other major flaws appeared in the NGINX Ingress Controller for Kubernetes, Atlassian Confluence Data Center and Server, and Apache ActiveMQ — and the latter two have already been targeted in ransomware attacks. 3 to report that the vulnerability is being actively exploited, which Rapid7 said includes ransomware attacks.

eSecurity Planet
DECEMBER 9, 2021
For cybersecurity personnel, our scope of responsibility may be limited to cyberattacks on IT systems, such as ransomware attacks, phishing attacks, and DDoS attacks. See the Best Ransomware Removal and Recovery Services. See Best Backup Solutions for Ransomware Protection. Incident Response Preparation. Document contingencies.

Data Matters
JANUARY 28, 2022
A few days after the Advisory, Ukrainian government websites were attacked by Russian actors while the Russian government simultaneously arrested members of the notorious ransomware gang REvil. Create, Maintain, and Exercise a Cyber Incident Response, Resilience, and Continuity of Operations Plan.

The Security Ledger
JULY 10, 2018
That after researchers in the Netherlands discovered that data from the Polar fitness app revealed the homes and habits of those exercising in clandestine locations around the world, including intelligence agencies, military bases, nuclear. Read the whole entry. »
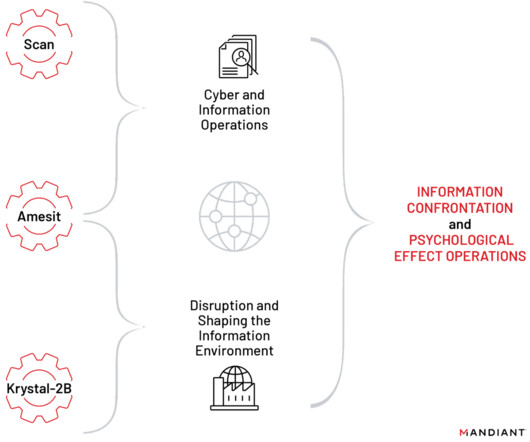
Security Affairs
APRIL 2, 2023
The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017. These projects include tools, training programs, and a red team platform for exercising various types of offensive cyber operations, including cyber espionage, IO, and operational technology (OT) attacks.”

Data Protection Report
NOVEMBER 8, 2023
Requirements The Amendment includes a new requirement to report to the superintendent of NYDFS when a ransomware event has been deployed in a material part of the covered entity’s information system (500.1(g)(3)).

IT Governance
DECEMBER 20, 2022
Although Vladimir Putin and his sympathisers assured the world that they were simply conducting military exercises, the inevitable occurred on 24 February, when troops mobilised and war was declared. By comparison, a report published last year found that US firms pay $6 million on average in ransomware demands.

IBM Big Data Hub
FEBRUARY 16, 2024
Like a red team exercise, breach and attack simulations use the real-world attack tactics, techniques, and procedures (TTPs) employed by hackers to proactively identify and mitigate security vulnerabilities before they can be exploited by actual threat actors.

IT Governance
OCTOBER 23, 2019
Brexit is clearly a pressing issue for many organisations, but we urge you to exercise caution whenever you receive communications out of the blue relating to the UK’s departure from the EU. Scammers and attackers are using attention-grabbing headlines about Brexit to try to trick users into handing over personal data or downloading malware.

IT Governance
SEPTEMBER 25, 2019
Phishing attacks are often used to deliver ransomware , which locks users out of their system until they pay money, often in bitcoin, to regain access. Cyber criminals often plant ransomware and other malware on organisations’ systems by exploiting security weaknesses in wireless networks. Preventing data breaches. Train staff.

eSecurity Planet
JULY 21, 2023
This entails completing frequent testing exercises, giving staff members thorough training, and making a proactive investment in the creation of new response capabilities. Organizations continually hone their methods for successful crisis response through this dynamic and iterative process.

KnowBe4
APRIL 4, 2023
Grimes Teaches Ransomware Mitigation Cyber-criminals have become thoughtful about ransomware attacks; taking time to maximize your organization's potential damage and their payoff. Join Roger for this thought-provoking webinar to learn what you can do to prevent, detect, and mitigate ransomware.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content