National Safety Council data leak: Credentials of NASA, Tesla, DoJ, Verizon, and 2K others leaked by workplace safety organization
Security Affairs
AUGUST 31, 2023
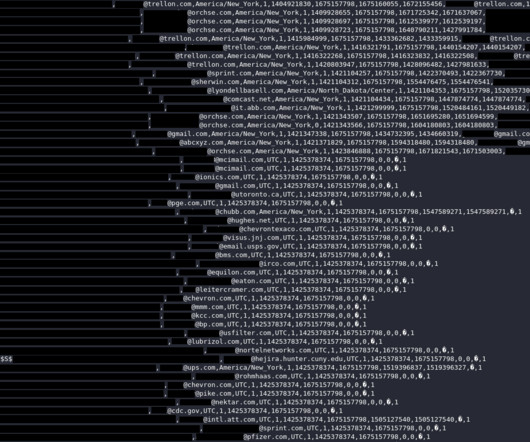
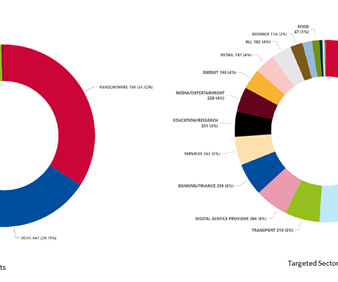
The National Safety Council leaked thousands of emails and passwords of their members, including companies such as NASA and Tesla. The National Safety Council has leaked nearly 10,000 emails and passwords of their members, exposing 2000 companies, including governmental organizations and big corporations.

















Let's personalize your content