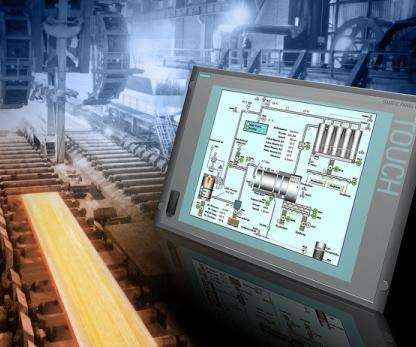
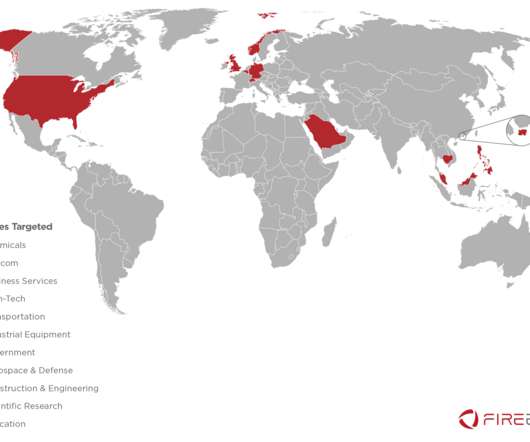
Hackers targeted ICS/SCADA systems at water facilities, Israeli government warns
Security Affairs
APRIL 27, 2020
. “The system calls on companies and entities in the energy and water sectors to immediately exchange passwords from the Internet to the control systems, reduce Internet connectivity and ensure that the most up-to-date version of controllers is installed.”

























Let's personalize your content