How To Delete Your Data From ChatGPT
WIRED Threat Level
MAY 8, 2023
OpenAI has new tools that give you more control over your information—although they may not go far enough.
WIRED Threat Level
MAY 8, 2023
OpenAI has new tools that give you more control over your information—although they may not go far enough.

Krebs on Security
MAY 9, 2023
The U.S. Federal Bureau of Investigation (FBI) this week seized 13 domain names connected to “ booter ” services that let paying customers launch crippling distributed denial-of-service (DDoS) attacks. Ten of the domains are reincarnations of DDoS-for-hire services the FBI seized in December 2022, when it charged six U.S. men with computer crimes for allegedly operating booters.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
MAY 9, 2023
Operation Medusa: FBI Tool Instructs Turla Group's Malware to Self-Destruct Federal officials say a global operation has disrupted Snake, the Russian government's "foremost cyberespionage tool," wielded by its Turla nation-state hacking group. The sophisticated malware has been tied to the theft of secret and classified information from numerous governments and businesses.

The Last Watchdog
MAY 8, 2023
There is no doubt there is a constant and growing concern amongst CEO’s, and particularly CISO’s, concerning the hiring of the cybersecurity talent their organizations require to safeguard against cyberattacks. According to Cybersecurity Ventures, by 2025 there will exist a gap of over 3.5 million unfilled cybersecurity positions. Moreover, of the current worldwide workforce, surveys conducted by PwC have shown that there is only a 38 percent ‘availability of key skills ’, considering the new an

Advertisement
After a year of sporadic hiring and uncertain investment areas, tech leaders are scrambling to figure out what’s next. This whitepaper reveals how tech leaders are hiring and investing for the future. Download today to learn more!

Data Breach Today
MAY 11, 2023
Beyond $25M in Estimated Cleanup Costs, The Game Remains Afoot for Victim Details In the annals of attempting to downplay the impact of a data breach, here's a new one: British outsourcing giant Capita says the hackers who hit it - steling data pertaining to customers, suppliers and employees - accessed "less than 0.1% of its server estate.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Hunton Privacy
MAY 11, 2023
On May 11, 2023, at a plenary session, the European Parliament voted to adopt a resolution on the adequacy of the protection afforded by the EU-U.S. Data Privacy Framework (the “Framework”) which calls on the European Commission (the “Commission”) to continue negotiations with its U.S. counterparts with the aim of creating a mechanism that would ensure equivalence and provide the adequate level of protection required by EU data protection law.

The Last Watchdog
MAY 11, 2023
Email remains by far the no.1 business communications tool. Meanwhile, weaponized email continues to pose a clear and present threat to all businesses. Related: The need for timely training At RSA Conference 2023 , I learned all about a new category of email security — referred to as integrated cloud email security ( ICES ) – that is helping companies more effectively keep email threats in check.
Data Breach Today
MAY 8, 2023
Leak Includes Intel Boot Guard and OEM Image Signing Keys for Over 200 Products The security of hundreds of MSI products is at risk due to hackers leaking private code signing keys stolen during a data breach last month. The signing keys allow an attacker to push malicious firmware updates under the guise of regular BIOS update processes with MSI update tools.

Schneier on Security
MAY 11, 2023
We will all soon get into the habit of using AI tools for help with everyday problems and tasks. We should get in the habit of questioning the motives, incentives, and capabilities behind them, too. Imagine you’re using an AI chatbot to plan a vacation. Did it suggest a particular resort because it knows your preferences, or because the company is getting a kickback from the hotel chain?

Speaker: Anindo Banerjea, CTO at Civio & Tony Karrer, CTO at Aggregage
When developing a Gen AI application, one of the most significant challenges is improving accuracy. This can be especially difficult when working with a large data corpus, and as the complexity of the task increases. The number of use cases/corner cases that the system is expected to handle essentially explodes. 💥 Anindo Banerjea is here to showcase his significant experience building AI/ML SaaS applications as he walks us through the current problems his company, Civio, is solving.

Dark Reading
MAY 10, 2023
While Intel is still investigating the incident, the security industry is bracing itself for years of potential firmware insecurity if the keys indeed were exposed.

The Last Watchdog
MAY 9, 2023
One meeting I had at RSA Conference 2023 , was a briefing about a new partnership , announced this morning, between a top-rung Silicon Valley tech giant and the leading provider of digital trust. Related: Centralizing control of digital certificates I had the chance to sit down with Deepika Chauhan , DigiCert’s Chief Product Officer, and Mike Cavanagh , Oracle’s Group Vice President, ISV Cloud for North America.

Data Breach Today
MAY 11, 2023
Also: Twitter Hacker Pleads Guilty, Seoul National University Hospital and Sysco In this week's data breach, the spotlight was on Dragos, a guilty plea from a Twitter hacker and cryptocurrency thief and North Korean hackers. Also, Sysco, a Ukrainian border truck queuing system and an update on Western Digital. Plus, a new tool for decrypting partially encrypted files.

AIIM
MAY 8, 2023
The AIIM 2023 Conference boasted a first-time attendee percentage of 61% and was graced by representatives from 28 countries. The overall agenda featured more than 80 sessions, so many topics and perspectives enriched the attendee experience. All the keynotes and general sessions were well-attended and ranged from discussing orthodox beliefs in the industry; the value of storytelling in IM; perspectives on artificial intelligence; and the C-Suite's take on Information Management.

Advertisement
Leverage the Cloud Development Environment Maturity Model to elevate your software development practices with scalable, secure cloud-based workspaces. This model offers a structured approach to modernizing development, aligning technology, developer experience, security, and workflows. By implementing Cloud Development Environments (CDEs), teams can boost efficiency, improve security, and streamline operations through centralized governance.

Schneier on Security
MAY 10, 2023
Reuters is reporting that the FBI “had identified and disabled malware wielded by Russia’s FSB security service against an undisclosed number of American computers, a move they hoped would deal a death blow to one of Russia’s leading cyber spying programs.” The headline says that the FBI “sabotaged” the malware, which seems to be wrong.

Hunton Privacy
MAY 11, 2023
On May 10, 2023, the Texas Senate passed H.B. 4 , also known as the Texas Data Privacy and Security Act (“TDPSA”). The TDPSA now heads to Texas Governor Greg Abbott for a final signature. If the TDPSA is signed into law, Texas could become the tenth state to enact comprehensive privacy legislation. The final text of the TDPSA closely follows H.B. 1844 , which we previously reported on when it was introduced in the Texas House in February.
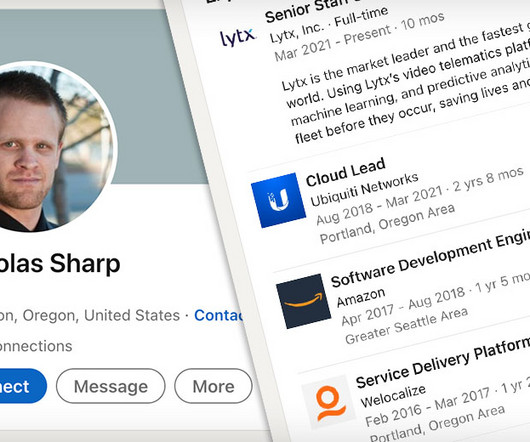
Data Breach Today
MAY 10, 2023
Nickolas Sharp, 37, Must Also Pay $1.6 Million In Restitution Nickolas Sharp, a one-time employee of Ubiquity who pleaded guilty to insider hacking received Wednesday a six year prison sentence. He admitted guilt on Feb. 2 to three criminal counts including transmitting a program to a protected computer that intentionally caused damage.
IBM Big Data Hub
MAY 9, 2023
We stand on the frontier of an AI revolution. Over the past decade, deep learning arose from a seismic collision of data availability and sheer compute power, enabling a host of impressive AI capabilities. But we’ve faced a paradoxical challenge: automation is labor intensive. It sounds like a joke, but it’s not, as anyone who has tried to solve business problems with AI may know.

Speaker: Aindra Misra, Senior Manager, Product Management (Data, ML, and Cloud Infrastructure) at BILL
Join us for an insightful webinar that explores the critical intersection of data privacy and AI governance. In today’s rapidly evolving tech landscape, building robust governance frameworks is essential to fostering innovation while staying compliant with regulations. Our expert speaker, Aindra Misra, will guide you through best practices for ensuring data protection while leveraging AI capabilities.

Schneier on Security
MAY 12, 2023
Ted Chiang has an excellent essay in the New Yorker : “Will A.I. Become the New McKinsey?” The question we should be asking is: as A.I. becomes more powerful and flexible, is there any way to keep it from being another version of McKinsey? The question is worth considering across different meanings of the term “A.I.” If you think of A.I. as a broad set of technologies being marketed to companies to help them cut their costs, the question becomes: how do we keep those technologies fro

Hunton Privacy
MAY 8, 2023
On May 4, 2023, the Court of Justice of the European Union (“CJEU”) issued a judgment in the Österreichische Post case (C-300/21). In the decision, the CJEU clarified that a mere infringement of the EU General Data Protection Regulation (“GDPR”) is not sufficient to give data subjects the right to receive compensation under Article 82 of the GDPR. Article 82 provides that “ any person who has suffered material or non-material damage as a result of an infringement of this Regulation shall have th

Data Breach Today
MAY 10, 2023
Akamai Says Exploit Sidesteps Patched Vulnerability Exploited by Russian Hackers Security researchers say a slight modification to a Microsoft Exchange zero day attack used by Russian state hackers can bypass a patch the computing giant introduced in March. Microsoft patched the modified attack during this month's dump of fixes, rating the bug as "important" but not "critical.

Lenny Zeltser
MAY 11, 2023
Too many people are unsure how to enter or grow in the cybersecurity industry. It's a relatively young field, and we haven’t done a good job of defining what it means to have a career in it. Hiring managers who are worried about finding candidates because of the much-discussed cybersecurity skills gap should consider the underlying issue, which I'd like to call the cybersecurity careers gap.

Advertisement
Tech leaders today are facing shrinking budgets and investment concerns. This whitepaper provides insights from over 1,000 tech leaders on how to stay secure and attract top cybersecurity talent, all while doing more with less. Download today to learn more!

Schneier on Security
MAY 8, 2023
At DEF CON this year, Anthropic, Google, Hugging Face, Microsoft, NVIDIA, OpenAI and Stability AI will all open up their models for attack. The DEF CON event will rely on an evaluation platform developed by Scale AI, a California company that produces training for AI applications. Participants will be given laptops to use to attack the models. Any bugs discovered will be disclosed using industry-standard responsible disclosure practices.
Hunton Privacy
MAY 12, 2023
On May 5, 2023, New York Attorney General Letitia James released proposed legislation that seeks to regulate all facets of the cryptocurrency industry. Entitled the “Crypto Regulation, Protection, Transparency, and Oversight (CRPTO) Act,” if enacted the bill would substantially expand New York’s oversight of crypto enterprises conducting business in the Empire State, including as to matters involving privacy and cybersecurity.

Data Breach Today
MAY 8, 2023
Data Leak Comes After Fullerton India Refused to Negotiate With Ransomware Group The LockBit 3.0 ransomware group on Monday leaked 600 gigabytes of critical data stolen from Indian lender Fullerton India two weeks after the group demanded a $3 million ransom from the company. The stolen data includes "loan agreements with individuals and legal companies.

eSecurity Planet
MAY 12, 2023
A vulnerability management policy sets the ground rules for the process, minimum standards, and reporting requirements for vulnerability management. An effective vulnerability management policy can help with the cyclical process of discovering and managing vulnerabilities found within IT hardware, software, and systems. A documented policy enables IT teams to create a trackable and repeatable process that meets the expectations of executives and conforms to compliance requirements.

Speaker: Christophe Louvion, Chief Product & Technology Officer of NRC Health and Tony Karrer, CTO at Aggregage
Christophe Louvion, Chief Product & Technology Officer of NRC Health, is here to take us through how he guided his company's recent experience of getting from concept to launch and sales of products within 90 days. In this exclusive webinar, Christophe will cover key aspects of his journey, including: LLM Development & Quick Wins 🤖 Understand how LLMs differ from traditional software, identifying opportunities for rapid development and deployment.

Dark Reading
MAY 11, 2023
Two years ago, a popular ransomware-as-a-service group's source code got leaked. Now other ransomware groups are using it for their own purposes.

Hunton Privacy
MAY 12, 2023
On May 4, 2023, the Biden-Harris Administration announced new actions to promote responsible American innovation in artificial intelligence (“AI”). The Administration also met with the CEOs of Alphabet, Anthropic, Microsoft and OpenAI as part of the Administration’s broader, ongoing effort to engage with advocates, companies, researchers, civil right organizations, not-for-profit organizations, communities, international partners, and others on critical AI issues.
Data Breach Today
MAY 10, 2023
May Patch Tuesday Fixes 38 Bugs Including 3 Zero Days Microsoft issued an optional patch Tuesday as part of its monthly dump of fixes that addresses for the second time a Secure Boot zero-day vulnerability exploited by BlackLotus UEFI malware. The patch is optional since the attacker must have admin privileges or physical access to the device.
Let's personalize your content