Phish Perfect: How ChatGPT Can Help Criminals Get There
Data Breach Today
OCTOBER 25, 2023
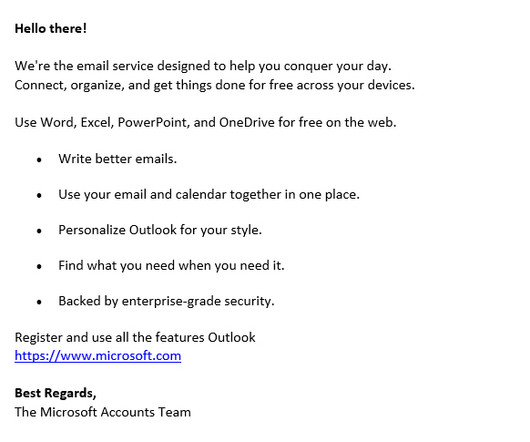
AI Generated Phishing Still Cannot Beat Humans, But Not for Long: IBM ChatGPT can craft almost perfect phishing emails in five minutes, nearly beating a social engineering team with decades of experience, the results of a "nail-biting" experiment by IBM showed. The "humans emerged victorious, but by the narrowest of margins," the report said.




































Let's personalize your content