Breach Roundup: US Bans AI Robocalls
Data Breach Today
FEBRUARY 8, 2024
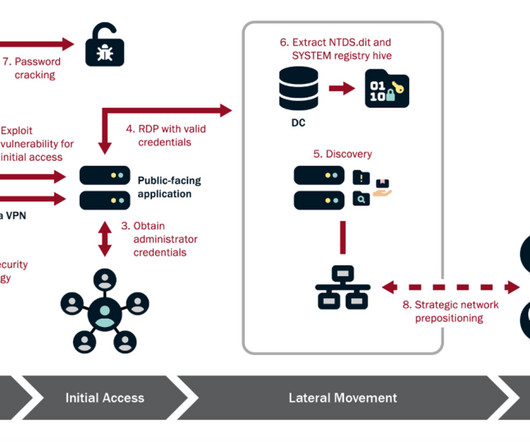
Also: A Widespread Linux Bootloader Vulnerability This week, the U.S. banned AI robocalls, researchers discovered a Linux bootloader flaw, France investigated health sector hackings, the feds offered money for Hive information, Verizon disclosed an insider breach, Germany opened a cybersecurity center, and cyberattack victims reported high costs.


































Let's personalize your content