The Future of Payments Security
Thales Cloud Protection & Licensing
JANUARY 26, 2021
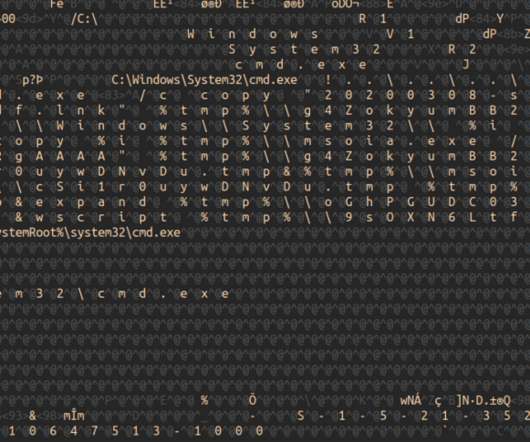
For example, compromised card details are used to make unauthorized purchases online and personal details are used to take over an account or apply for a credit card in someone else’s name. Security researchers often use the term “magecart” to refer to different groups of cybercriminals that perform various types of skimming attacks.


































Let's personalize your content