Why Zero Trust Is the Cloud Security Imperative
Dark Reading
OCTOBER 16, 2023
The security principle of zero trust is the cornerstone of robust cloud security.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 cloud-security zero-trust
cloud-security zero-trust 
Dark Reading
OCTOBER 16, 2023
The security principle of zero trust is the cornerstone of robust cloud security.

Data Breach Today
FEBRUARY 2, 2024
Also: AI in Cloud Security, Integrating Zero Trust Principles into API Deployment In the latest weekly update, ISMG editors discussed the potential role of AI in cloud security, how the recent cyberattack on Microsoft by Russian state hackers highlighted the vulnerabilities associated with legacy systems, and how to secure APIs in the age of zero trust. (..)
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
JANUARY 26, 2024
Payments Expert Troy Leach Joins the Panel to Cover AI, Zero Trust and IoT Security In the latest weekly update, Troy Leach, CSO at Cloud Security Alliance, joins three editors at ISMG to discuss important cybersecurity issues, including how generative AI is enhancing multi-cloud security, AI's influence on authentication processes, and the state of (..)

Data Breach Today
FEBRUARY 27, 2024
Forrester's David Holmes on Why CISOs Must Evaluate Microsegmentation in Cloud Microsegmentation is a fundamental concept in zero trust security, but CISOs should assess its feasibility before diving in.

Data Breach Today
JULY 17, 2023
Naveen Palavalli, Vice President Product Strategy, Netskope on the rise of Zero Trust Networks Naveen Palavalli, Vice President Product Strategy, Netskope discusses the impact that the rise of Zero Trust Networks has had upon Cloud Transformation and Access

Data Breach Today
AUGUST 16, 2023
Cloud-Delivered Security Service Edge Solution Gives Efficient Hybrid Work Security Cisco Secure Access is a security service edge solution that delivers zero trust access to efficiently solve today's challenge of safely connecting anything to anywhere and reimagines the experience to make it better for users, easier for IT and safer for everyone.

Data Breach Today
JUNE 20, 2022
Cloudflare's Zero Trust Platform Offers More Robust Threat Intel, Network Discovery Cloudflare sees opportunity in the growth of zero trust and is integrating recent email and cloud security acquisitions with native data security and network discovery capabilities. "I

Thales Cloud Protection & Licensing
NOVEMBER 6, 2019
In a previous blog post ( [link] ) we explored the relationship between GPDR and applications in the cloud. Trust is generally the foundation and basis of any good relationship, but when it comes to protecting your organization, sometimes a Zero Trust mentality is your best bet. That’s where access management comes in.

Data Breach Today
SEPTEMBER 12, 2022
Implement a Zero Trust Strategy to Secure the Digital Transformation Journey With the increase in remote workers and proliferation of uncontrolled devices, your IT team has been migrating applications to the cloud along with building cloud-native applications to support the speed needed by the business.

Data Breach Today
JUNE 16, 2022
Microsoft's Abbas Kudrati and HCL's Upendra Singh on Zero Trust and Cloud Security Organizations have created significant security challenges by rapidly migrating applications, data and workloads to multiple public clouds over the course of the COVID-19 pandemic, according to Abbas Kudrati of Microsoft and Upendra Singh of HCL.

Data Breach Today
AUGUST 26, 2022
Russian-Based Malware Enables Attackers to Login as Any User and Bypass MFA The recently discovered Russian-linked MagicWeb malware that exploits on-premises Microsoft Active Directory Federated Services servers to persist in compromised systems underscores the benefits of cloud-based infrastructure and a zero trust approach to architecture, security (..)

The Last Watchdog
JUNE 3, 2022
The zero trust approach to enterprise security is well on its way to mainstream adoption. At RSA Conference 2022 , which takes place next week in San Francisco, advanced technologies to help companies implement zero trust principals will be in the spotlight. Zero trust, put simply, means eliminating implicit trust.

The Last Watchdog
SEPTEMBER 21, 2022
Remote work already had an impact on IT strategy and the shift to cloud, including hybrid cloud , well before the onset of Covid 19. Yet, with all these changes, the specter of security breaches remains high. and Eastern Europe, which favor public cloud. Strategy reassessment needed.

The Last Watchdog
JANUARY 30, 2024
This integration signifies a significant leap in Aembit’s mission to empower organizations to apply Zero Trust principles to make workload-to-workload access more secure and manageable. This integration with Aembit enables organizations to secure machine identities as part of a holistic approach to security.”

Data Breach Today
APRIL 4, 2023
Deal Will Give Cradlepoint Robust Portfolio Across SD-WAN and Security Service Edge Cradlepoint has bought seasoned Israeli security veteran Ericom Software to bring SASE, zero trust and cloud security to hybrid 5G and wireline environments.

Data Breach Today
FEBRUARY 9, 2021
Three Examples of How to Overcome Hurdles Three CISOs offer real-world insights on addressing the challenges involved in implementing a "zero trust" framework to enhance security in an era when so many remote employees are accessing applications and data in the cloud as well as within internal networks.
Data Breach Today
JANUARY 8, 2021
This edition of the ISMG Security Report features an analysis of the very latest information about the SolarWinds hack. Also featured are discussions of "zero trust" for the hybrid cloud environment and data privacy regulatory trends.

The Last Watchdog
NOVEMBER 8, 2021
There’s no doubt, the increasing use of telemedicine, the explosion of health-based cloud apps, and innovative medical IoT devices are improving the patient care experience. However, healthcare data ranks at the top of the list for needing improvements in security and privacy protections. Patient data exposures.

The Last Watchdog
SEPTEMBER 26, 2022
Thanks to the emergence of today’s hybrid and multi-cloud environments and factors like remote work, ransomware attacks continue to permeate each industry. As enterprises continue to fall victim to increasingly complex attacks, there’s one topic that cybersecurity professionals and vendors can agree on: the importance of Zero Trust.

The Last Watchdog
JUNE 28, 2022
This is so, despite the fact that the fundamental design of a VPN runs diametrically opposed to zero trust security principles. Guest expert: David Holmes, Analyst for Zero Trust, Security and Risk, Forrester Research. VPNs verify once and that’s it. Pulitzer Prize-winning business journalist Byron V.

Data Breach Today
NOVEMBER 23, 2022
Army has embarked on its zero trust journey for both its information and network operations. Army CIO Dr. Raj Iyer shares how the military and the private sector are partnering to secure cloud infrastructure and solidify threat intelligence capabilities to fight adversaries.

Data Breach Today
OCTOBER 27, 2022
Versa Will Use the Pre-IPO Money to Help Guard the Cloud and Bring ZTNA to Campuses Versa Networks has completed a pre-IPO funding round to build out a cloud security portfolio and bring zero trust functionality to campus and branch settings.

The Last Watchdog
SEPTEMBER 27, 2022
Enterprises are racing to push their digital services out to the far edge of a highly interconnected, cloud-centric operating environment. This has triggered a seismic transition of company networks, one that has put IT teams and security teams under enormous pressure. based supplier of security, cloud and application services.

The Last Watchdog
SEPTEMBER 22, 2023
Tunkelo “We are excited to have this leading global financial institution enter their Zero Trust journey with our help,” said Dr. Teemu Tunkelo , CEO of SSH. Benefits of PrivX •Eliminates static credentials with passwordless authentication and just-in-time access, enabling easy implementation of Zero Trust access management solution.

Data Breach Today
MARCH 6, 2020
Two Cyber Vets Double Click on Hot Topics of RSA Conference Supply chain risk, security in the cloud, zero trust - these were three of the hottest topics at RSA Conference. And they were discussed candidly - and with some humor - when thought-leaders Edna Conway and Wendy Nather entered ISMG Studios.

The Last Watchdog
AUGUST 8, 2023
8, 2023 – DigiCert today announced the expansion of its certificate management platform, DigiCert Trust Lifecycle Manager, to provide full lifecycle support for multiple CAs including Microsoft CA and AWS Private CA, as well as integration with ServiceNow to support existing IT service workflows. Lehi, Utah, Aug. About DigiCert, Inc.

The Last Watchdog
JULY 30, 2021
Company-supplied virtual private networks (VPNs) leave much to be desired, from a security standpoint. Related: How ‘SASE’ is disrupting cloud security. Conversely, Zero Trust has gained some material traction. One start-up, Axis Security , couldn’t be more in the thick of these trends.

Data Breach Today
AUGUST 19, 2021
Menlo Security's Mark Guntrip on How to Learn to 'Defend Differently' On one hand, rapid cloud migration has been a boon to financial services organization. But it's also exposed some security weaknesses.

The Last Watchdog
AUGUST 19, 2022
VPNs are being replaced by zero trust network access, or ZTNA. VPNs encrypt data streams and protect endpoints from unauthorized access, essentially by requiring all network communications to flow over a secured pipe. By contrast, ZTNA never trusts and always verifies. VPNs verify once and that’s it.

The Last Watchdog
JULY 27, 2022
Related: The importance of ‘SaaS posture management’ As digital transformation continues to intensify, organizations are relying more and more on hosted cloud processing power and data storage, i.e. Platform as a Service ( PaaS ,) as well as business tools of every stripe, i.e. Software as a Service ( SaaS. ).

Jamf
FEBRUARY 15, 2022
Learn how the partnership between Jamf Pro and Google BeyondCorp enables you to construct a compliance and security framework around end-user devices, blending Jamf’s device management with Google’s endpoint management security for a comprehensive, cloud-based, Zero Trust solution.

IBM Big Data Hub
JANUARY 10, 2024
Hybrid cloud has become the dominant approach for enterprise cloud strategies , but it comes with complexity and concerns over integration, security and skills. RH OCP provides a common deployment, control and management environment for workloads across a diverse set of infrastructures that underpin a hybrid cloud.

Data Breach Today
JULY 8, 2019
Sandy Dalal of Allergan on Achieving Security Stability Mergers and acquisitions, along with cloud adoption, are rapidly changing the pharmaceutical industry. Sandy Dalal of Allergan talks about how identity and access management, along with zero trust, are bringing security stability.

IT Governance
JANUARY 5, 2024
How networks have evolved and how to secure them Adam Seamons is the information security manager of GRC International Group PLC, after more than 15 years’ experience working as a systems engineer and in technical support. What trends in network security have you noticed recently? You say “traditional” security.

The Last Watchdog
MAY 5, 2022
Let’s walk through some practical steps organizations can take today, implementing zero trust and remote access strategies to help reduce ransomware risks: •Obvious, but difficult – get end users to stop clicking unknown links and visiting random websites that they know little about, an educational challenge. Let’s talk VPNs.

The Last Watchdog
APRIL 5, 2019
The Cloud Access Security Broker (CASB) space is maturing to keep pace with digital transformation. One company still actively innovating as an independent CASB is San Jose, CA-based security vendor CipherCloud. This is especially important within the cloud. The security challenge, however, is now much more pronounced.

Data Breach Today
JUNE 5, 2019
The zero trust model has been around for a decade, and the ideas around it have evolved as applications have left the enterprise perimeter, says Lisa Lorenzin of Zscaler. With mobile apps and cloud computing, enterprises are facing challenges creating secure, trusted access paths.
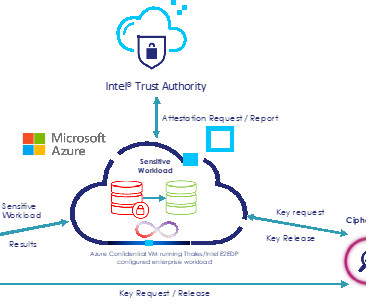
Thales Cloud Protection & Licensing
NOVEMBER 14, 2023
Meanwhile, organizations continue to invest in digital transformation by utilizing the efficiencies and elasticity offered by cloud service providers. Therefore, there is a need to continually raise the bar in cloud security.

Thales Cloud Protection & Licensing
MARCH 24, 2024
Data Security Trends: 2024 Report Analysis madhav Mon, 03/25/2024 - 05:08 Amid ongoing economic uncertainty and a progressively complex threat landscape, businesses are trying to navigate increasingly stringent regulatory requirements while bolstering their security posture.

Thales Cloud Protection & Licensing
AUGUST 1, 2022
As more companies move along the path toward digital transformation, the need for better security has never been more evident. A zero-trust framework is vital to any cloud migration path. Thales has collaborated with fellow global security giant, Palo Alto Networks , to make zero-trust available at scale for businesses.

Krebs on Security
MARCH 15, 2023
Microsoft on Tuesday released updates to quash at least 74 security bugs in its Windows operating systems and software. ” “The vulnerability effectively lets the attacker authenticate as a trusted individual without having to know the person’s password,” Breen said.

Thales Cloud Protection & Licensing
FEBRUARY 17, 2022
Best Practices for a Modern Cloud Security Architecture. Partnering with Thales, Red Hat takes the latest in open source innovation and crafts that into secure, enterprise-ready solutions. I was invited to the 2021 Thales Cloud Security Summit to discuss modern cloud security architecture with Alex Hanway.

The Last Watchdog
DECEMBER 13, 2020
One legacy of the ongoing global pandemic is that companies now realize that a secured and well-supported remote workforce is possible. Related: SASE translates into secure connectivity. SASE can function as security infrastructure and as the core IT network of large enterprises. The makeup of SASE . But it much further.
Thales Cloud Protection & Licensing
OCTOBER 23, 2023
The 2023 Thales Data Threat Report Critical Infrastructure Edition , which includes responses from 365 security leaders and practitioners within critical infrastructure organizations, serves as a fine reminder of the requirement to embed security into the culture of every organization and individual. And only a mere 2.6%
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content