Orange Business Services hit by Nefilim ransomware operators
Security Affairs
JULY 17, 2020
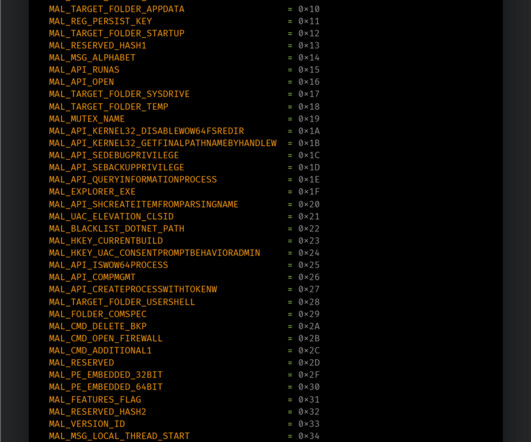
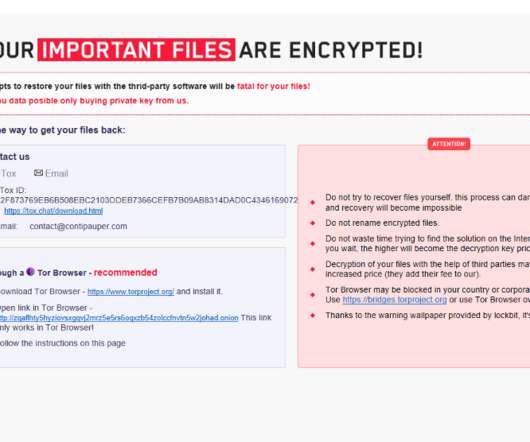
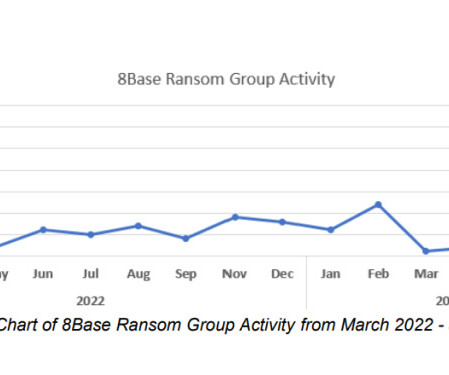
Security researchers at Cyble reported that Nefilim ransomware operators allegedly targeted the mobile network operator Orange. Researchers from Cyble came across a post of Nefilim ransomware operators which were claiming to have stolen sensitive data of Orange S.A., one of the largest mobile networks based in France.













Let's personalize your content