Writing Your First Bootloader for Better Analyses
Security Affairs
SEPTEMBER 3, 2019
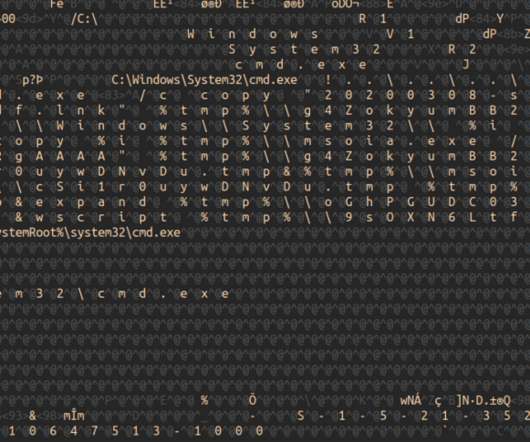
For this reason I believe it would be interesting to understand how MBR works and how is it possible to write a boot loader program, this skill will help you during the analysis of your next Boot Loader Malware. When you press the power button you are providing the right power to every electronic chips who needs it. as -o boot.o





















Let's personalize your content