New Bad Magic APT used CommonMagic framework in the area of Russo-Ukrainian conflict
Security Affairs
MARCH 21, 2023
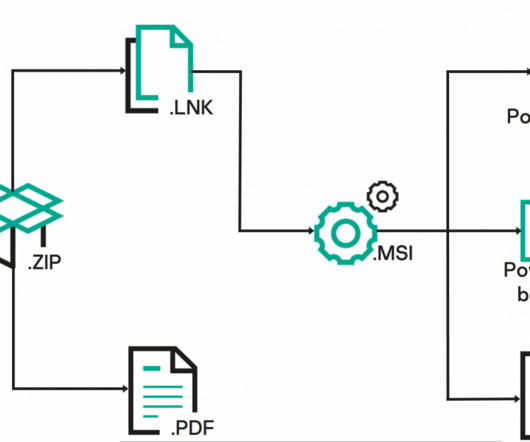
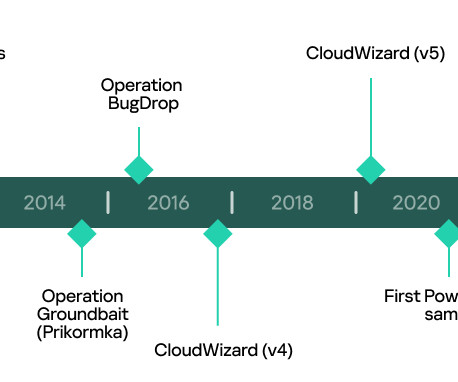
In October 2022, Kaspersky researchers uncovered a malware campaign aimed at infecting government, agriculture and transportation organizations located in the Donetsk, Lugansk, and Crimea regions with a previously undetected framework dubbed CommonMagic. “When started, the backdoor creates a mutex – WinEventCom.
















Let's personalize your content