Security Affairs newsletter Round 460 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.

The Last Watchdog
JULY 30, 2018
DataLocker honed its patented approach to manufacturing encrypted portable drives and landed some key military and government clients early on; the company has continued branching out ever since. All the user needs is a strong password to access to the data. But in certain cases the cloud is not readily accessible.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Information Governance Perspectives
APRIL 5, 2023
John Danenberger, CPCU, is Corporate Counsel at State Farm Insurance and specializes in addressing emerging issues around telematics. In 2015, he successfully transitioned from a military career as a trial attorney for the JAG Corps to working in telematics in corporate America for State Farm Insurance.

IT Governance
AUGUST 3, 2020
Canadian insurer Heartland Farm Mutual says an employee’s email account breached (unknown). Brazilian health insurer Hapvida discloses cyber attack (unknown). Four military schools in Canada targeted in ‘mysterious’ cyber attack (unknown). Group of free VPN apps expose user data on publicly accessible database (20 million).

Data Protection Report
OCTOBER 3, 2021
credit or debit card number, or any financial account number in combination with any required security code, access code or password that would permit access to such financial account.
Security Affairs
MAY 3, 2022
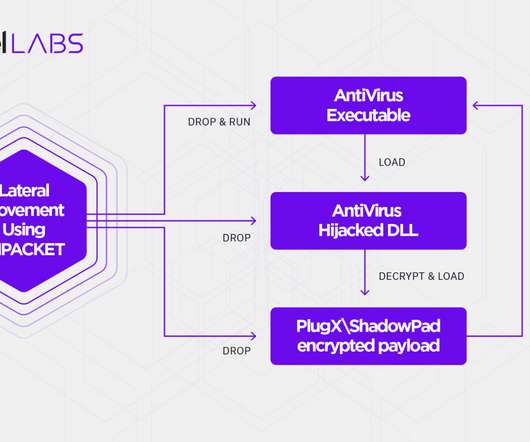
RedFoxtrot has been active since at least 2014 and focused on gathering military intelligence from neighboring countries, it is suspected to work under the PLA China-linked Unit 69010. Experts observed overlap between the TTPs of the Moshen Dragon group with the ones of the Chinese Nomad Panda (aka RedFoxtrot).
IT Governance
NOVEMBER 1, 2022
Meanwhile, be sure to subscribe to our Weekly Round-up to receive the latest cyber security news and advice delivered straight to your inbox. Cyber attacks.
Security Affairs
JUNE 17, 2020
“Our investigation to-date has identified evidence of unauthorized access to our systems from approximately April 15, 2020 until May 24, 2020. Our investigation has also identified evidence of unauthorized access to files containing personal information relating to you.” .” reads the data breach notification.

IT Governance
JULY 1, 2021
Agency for International Development IBM gives school districts grants to harden security against ransomware attacks UK businesses in the South East get access to Police CyberAlarm HSE seeks order to help find who uploaded or downloaded files stolen in cyber attack. million drivers’ details (3.3

Hunton Privacy
MAY 9, 2019
Further, the expanded definition now includes “username or email address in combination with a password or security questions and answers that would permit access to an online account” (without an individual’s name). Method of Notification.

KnowBe4
MARCH 28, 2023
The capacity to craft compelling, well-formed text is in the hands of anyone with access to ChatGPT, and that's basically anyone with an internet connection." In a statement by Xavier Chango, the National Head of Forensic Science, "It's a military-type explosive, but very small capsules." He covers it from all angles!

Krebs on Security
SEPTEMBER 10, 2018
A credit freeze — also known as a “security freeze” — restricts access to your credit file, making it far more difficult for identity thieves to open new accounts in your name. Access to some of these credit lookup services is supposed to be secured behind a login page, but often isn’t.

Krebs on Security
SEPTEMBER 21, 2018
In addition, the law requires the big three bureaus to offer free electronic credit monitoring services to all active duty military personnel. By the same token, freezes do nothing to prevent crooks from abusing unauthorized access to these existing accounts. For more information on doing that with ChexSystems, see this link.

eSecurity Planet
OCTOBER 5, 2021
Access to a range of ransomware tools tailored to remove specific strains of malware. Immediate access to experts for swift resolution of security issues. Digital forensics for insurance, medical, legal, and Fortune 500 companies. Incident report for law enforcement and insurance. Fine-tuning and hardening security.
Hunton Privacy
JUNE 22, 2020
heath records or records of a wellness program or similar program of health promotion or disease prevention, a health care professional’s medical diagnosis or treatment of the consumer or a health insurance policy number.

Hunton Privacy
JUNE 14, 2018
Attorney General Notification: If an entity must notify Colorado residents of a data breach, and reasonably believes that the breach has affected 500 or more residents, it must also provide notice to the Colorado Attorney General.

IT Governance
SEPTEMBER 1, 2020
Toronto residents’ CERB payments on hold after fraudulent employment insurance claims (700) Kentucky’s unemployment system suffers another breach (unknown) Defence supplier PULAU Corporation says it has been hacked (unknown) American Payroll Association notifying those affected by cyber attack (unknown). Cyber attacks. Hitachi Chemical Co.

IT Governance
FEBRUARY 14, 2024
Compromised data includes policyholders’ and their families’ civil status, dates of birth and social security numbers, as well as the name of their health insurer and information relating to their contracts. In November 2023, Northwell Health – the largest health system in New York – confirmed that it was affected by the incident.

eSecurity Planet
FEBRUARY 16, 2021
” Or you might see a readme.txt stating, “Your files have been replaced by these encrypted containers and aren’t accessible; you will lose your files on [enter date] unless you pay $2500 in Bitcoin.” A cloud access security broker (CASB) can help manage policy enforcement for your organization’s cloud infrastructure.

IT Governance
JUNE 27, 2019
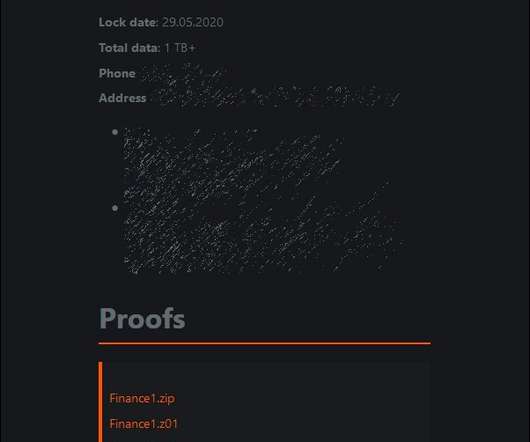
The ransomware was accompanied by a note: “Your files are encrypted with the strongest military algorithms. To access the decoder, the organisation was asked to pay a large ransomin bitcoin. Another way to lessen the burden of recovering from a ransomware attack is to purchase cyber insurance.

IT Governance
MARCH 1, 2022
KG operating with limited service after cyber attack (unknown) Morley Companies, Inc.
Data Protection Report
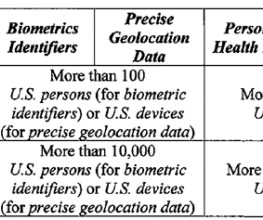
MARCH 7, 2024
government, including the military and Intelligence Community.” government, including the military and Intelligence Community.” (at The IT services provided under the contract involve access to the medical facility’s systems containing the bulk personal health data. What types of data brokerage transactions are in-scope?

DLA Piper Privacy Matters
JUNE 4, 2021
This is a reminder for the automobile industry – and its supporting industries and insurers – to ensure a robust compliance framework to protect that data, and to reconsider processing of such data outside of China. outside of the vehicle; and. other data that may affect national security and public interests.

Krebs on Security
DECEMBER 29, 2022
Several strong themes emerged from 2022’s crop of breaches, including the targeting or impersonating of employees to gain access to internal company tools; multiple intrusions at the same victim company; and less-than-forthcoming statements from victim firms about what actually transpired. com, which was fed by pig butchering scams.

eSecurity Planet
APRIL 26, 2024
Endpoint: Enables access for human users and computer services and commonly includes PCs, laptops, Internet of Things (IoT), and operational technology (OT). Security Elements Security elements protect each element within the network, network access, and the data transmissions. or segregated as cloud or network attached storage (NAS).

IT Governance
APRIL 9, 2024
Other databases contained health insurance data, such as patents’ names, dates of birth, addresses and medical data. EyeCare Services Partners exposes more 3.5 The biggest database in the blob contained 3.1 million patients and 1.6 million unique Social Security numbers. Source (New) Manufacturing USA Yes 1.1

The Last Watchdog
DECEMBER 3, 2018
I have a Yahoo email account, I’ve shopped at Home Depot and Target , my father was in the military and had a security clearance, which included a dossier on his family, archived at the U.S. Office of Personnel Management , I’ve had insurance coverage from Premera Blue Cross and I’ve stayed at the Marriott Marquis in San Francisco.

Security Affairs
MAY 13, 2020
Magellan Health, a for-profit managed health care and insurance firm, was the victim of a ransomware attack. is an American for-profit managed health care company, its customers include health plans and other managed care organizations, employers, labor unions, various military and governmental agencies and third-party administrators.

IT Governance
APRIL 22, 2024
GhostR says it obtained the records from a Singapore-based company with access to the database. Mobile Guardian, which is based in the UK, said that its investigations detected unauthorised access to its systems via an administrative account on its management portal. Account records from the United States were also accessed.

IT Governance
AUGUST 1, 2023
million) Milliman Solutions notifies patients of third-party breach involving MOVEit (1.2 million) Milliman Solutions notifies patients of third-party breach involving MOVEit (1.2 million) Milliman Solutions notifies patients of third-party breach involving MOVEit (1.2
Krebs on Security
DECEMBER 13, 2021
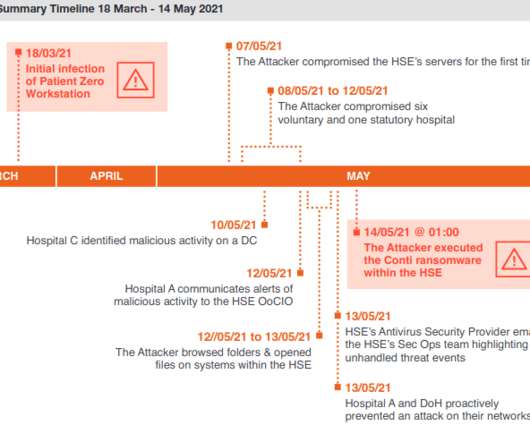
On May 10, one of the hospitals detected malicious activity on its Microsoft Windows Domain Controller, a critical “keys to the kingdom” component of any Windows enterprise network that manages user authentication and network access. Still, the work to restore infected systems would take months.

IT Governance
JANUARY 23, 2024
Microsoft gives all businesses access to AI-powered Office features When Microsoft launched Copilot for Office 365 in November 2023, it required enterprise customers to have at least 300 users. O’Hara & Sons, Inc. It has now removed that requirement, opening up Copilot to businesses of all sizes.

Security Affairs
NOVEMBER 29, 2019
According to Group-IB’s experts, the most frustrating trend of 2019 was the use of cyberweapons in military operations. As for 2019, it has become the year of covert military operations in cyberspace. The threat actor mainly targets insurance, consulting, and construction companies.

IT Governance
MARCH 28, 2019
Chinese hackers target universities in pursuit of maritime military secrets (unknown). Software company Citrix says hackers accessed its internal network (unknown). Email marketing company leaves its mailing list on a publicly accessible database (809 million). Insurance firm AIA Singapore discovers data breach (225).

eSecurity Planet
SEPTEMBER 19, 2022
Since many people use the same passwords or patterns when generating passwords, hackers have more and more opportunities to gain access to sensitive company data. For enterprise organizations with a large workforce that must access a wide variety of applications and databases, the risk is exponentially greater.

Collibra
NOVEMBER 2, 2020
Characteristics of protected classifications under California or federal law such as race, ancestry, national origin, religion, age, mental and physical disability, sex, sexual orientation, gender identity, medical condition, genetic information, marital status, or military status. Biometric information.
Hunton Privacy
MARCH 2, 2023
s ability to assist allies and partners in strengthening cybersecurity, (iv) building coalitions to reinforce global norms of responsible state behavior, and (v) securing global supply chains for information, communications and operational technology products and services that power the U.S. economy.

ForAllSecure
MAY 30, 2023
Obviously, organizations gotten smart to that and they started doing offline backups securing their backups differently, so that they would continue to have access and availability. And without access to that information or those systems, they're not able to continue to operate. VAMOSI: Does Mark typically work with insurance?

ForAllSecure
JANUARY 19, 2022
Simon Moffatt from CyberHut joins The Hacker Mind to discuss how identity and access management (IAM) is fundamental to everything we do online today, and why even multi-factor access, while an improvement, needs to yield to more effortless and more secure passwordless technology that’s coming soon. Something better? Lewis: Good.

Data Matters
APRIL 23, 2018
Using appropriate access controls. Boards should have adequate access to cybersecurity expertise, and discussions about cyber-risk management should be given regular and adequate time on board meeting agendas. Using Appropriate Access Controls. Aligning cyber risk with corporate strategy. Encrypting critical data assets.

eSecurity Planet
FEBRUARY 11, 2021
This creates a lot of opportunities for hackers to gain access to company resources because users often reuse passwords or mirror patterns in creating them. For enterprise organizations with a large workforce that must access a wide variety of applications and databases, the risk is exponentially greater.
Hunton Privacy
APRIL 3, 2020
The Bill also defines personal information to include “a user name or email address in combination with a password, security question and answer, or other means of authentication, or any combination of data elements [listed above] that permits access to an individual’s email account.”. Harm Threshold. Partial GLB/HIPAA Pre-Emption.

The Last Watchdog
JUNE 1, 2020
Clinton: Take for example, restrictions many companies have on the websites employees are permitted to access from their office computers. And they might look into getting insurance to transfer at least some of this risk. Clinton: The insurance industry is large, complex and diversified.

KnowBe4
JUNE 6, 2023
China's People's Liberation Army (PLA) is increasingly focused on "Cognitive Warfare," a term referring to artificial intelligence (AI)-enabled military systems and operational concepts. This involves influencing the thinking of decision-makers, military commanders, and the general public in rival countries. efforts to support Taiwan.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content