Privacy of Printing Services
Schneier on Security
JULY 11, 2023
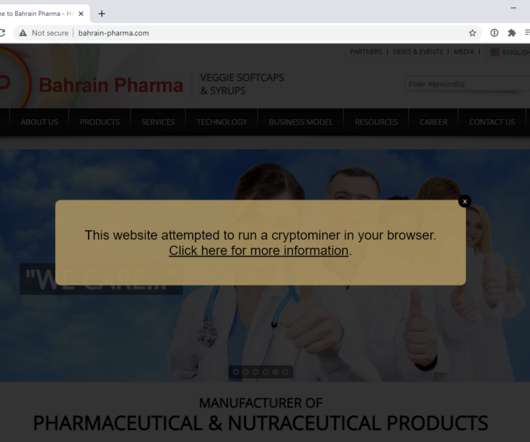
The Washington Post has an article about popular printing services, and whether or not they read your documents and mine the data when you use them for printing: Ideally, printing services should avoid storing the content of your files, or at least delete daily. Some services, like the New York Public Library and PrintWithMe, do both.



















Let's personalize your content