How to Ensure Your Digital Security During the Rugby World Cup
Thales Cloud Protection & Licensing
SEPTEMBER 12, 2019
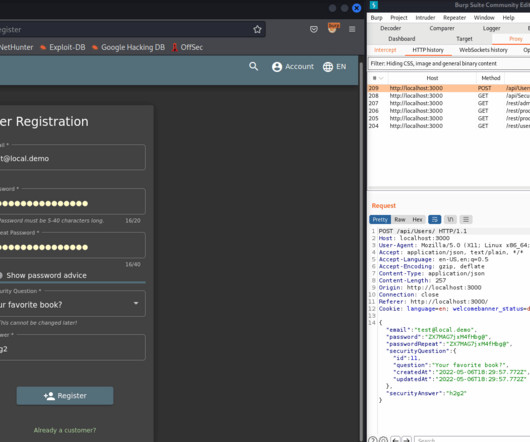
Just a couple of months after that, World Rugby itself announced that one of its training websites had suffered a security breach that exposed subscribers’ account information. That’s why it announced it would pursue two measures designed to strengthen its national digital security posture ahead of these sporting events.
























Let's personalize your content