Texas Hospital Says Ransomware Breach Affected 500,000
Data Breach Today
NOVEMBER 11, 2022
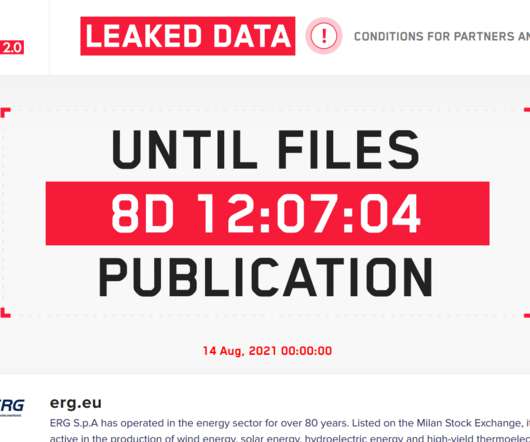
Also: CommonSpirit Health Says Some IT Systems Still Affected 6 Weeks After Attack A recent ransomware attack at a Texas hospital that knocked out phone and email systems for weeks is now even worse following OakBend Medical Center's admission that the hackers downloaded data from the medical records of up to 500,000 individuals.





































Let's personalize your content