Security Affairs newsletter Round 460 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Security Affairs
FEBRUARY 25, 2024
Iran Crisis Russia-Aligned TAG-70 Targets European Government and Military Mail Servers in New Espionage Campaign U.S.

IT Governance
APRIL 9, 2024
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. Publicly disclosed data breaches and cyber attacks: in the spotlight US Environmental Protection Agency allegedly breached: nearly 8.5 Data breached: 8,460,182 accounts.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
IT Governance
SEPTEMBER 6, 2023
IT Governance found 73 publicly disclosed security incidents in August 2023, accounting for 79,729,271 breached records. You can find the full list below, divided into four categories: cyber attacks, ransomware, data breaches, and malicious insiders and miscellaneous incidents.

IT Governance
AUGUST 1, 2023
IT Governance found 87 publicly disclosed security incidents in June 2023, accounting for 146,290,598 breached records. You can find the full list below, divided into four categories: cyber attacks, ransomware, data breaches, and malicious insiders and miscellaneous incidents.

Security Affairs
AUGUST 17, 2021
Colonial Pipeline discloses a data breach of the personal information of thousands of individuals after the ransomware attack that took place in May 2021. SecurityAffairs – hacking, data breach). The post Colonial Pipeline discloses data breach after May ransomware attack appeared first on Security Affairs. Pierluigi Paganini.
IT Governance
NOVEMBER 1, 2022
Welcome to our October 2022 review of data breaches and cyber attacks. By contrast, comparatively little personal data was breached, with our figures confirming that at least 9,990,855 records were compromised. For now, it’s unclear what damage the data could cause if exposed, so we’ve omitted the figure from our tally.

Data Protection Report
OCTOBER 3, 2021
Effective October 1, 2021, an amendment [1] to the Connecticut General Statute concerning data privacy breaches, Section 36a-701b, will impact notification obligations in several significant ways. Required Identity Theft Prevention Services.
Data Protection Report
MARCH 7, 2024
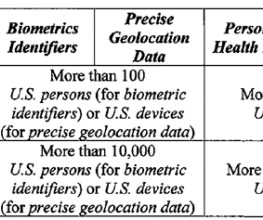
China Cuba Iran North Korea Russia Venezuela What is “personally identifiable data” that is “in combination with each other”? The proposed regulation would define the term to mean any “listed identifier” that is linked to any other “listed identifier.” Note that the only difference between the two examples is the addition of IP addresses.

IT Governance
AUGUST 3, 2020
After mammoth amounts of personal data were leaked in May and June, we’ve seen a reversion to the mean this month. You can find our full list of publicly disclosed data breaches from July in this blog. Bitcoin scam leaks personal data of users from across the globe (248,926). Cyber attacks.

IT Governance
MARCH 11, 2024
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. Data breached: 36 million records. Data breached: 6,935,412 individuals’ data. Data breached: 6.9 Only 3 definitely haven’t had data breached.

IT Governance
APRIL 22, 2024
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. million records from World-Check, a screening database used to screen potential customers for links to illegal activity and government sanctions. Data breached: 5,300,000 records.

IT Governance
JANUARY 23, 2024
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. The data set is a collection of 1 billion credentials sourced from stealer logs and hosted on the illicit.services website. Data breached: 70,840,771 email addresses.

IT Governance
MARCH 1, 2022
Our figures for this month are comparatively low – with 83 data breaches and cyber attacks accounting for 5,127,241 breached records – but there is a sense that we are on the brink of something. First, Russia targeted banks and government departments, then Ukraine hit back, attacking the Moscow stock exchange. Data breaches.
Hunton Privacy
APRIL 3, 2020
s data breach notification law (the “Bill”). Among other requirements, the Bill requires the provision of identity theft prevention services in certain data breaches, establishes a new regulatory reporting requirement in the event of a cognizable data breach affecting 50 or more residents of D.C., Harm Threshold.

IT Governance
JULY 1, 2021
It’s simply the case that in the majority of cases, the breached organisation didn’t reveal how much data was compromised, either because it didn’t know or wasn’t obliged to reveal it publicly. Data breaches. But don’t be fooled by that number – it comes from 106 incidents, which is roughly average for the year. Cyber attacks.

The Last Watchdog
JULY 30, 2018
DataLocker honed its patented approach to manufacturing encrypted portable drives and landed some key military and government clients early on; the company has continued branching out ever since. All the user needs is a strong password to access to the data. You need to rely on external storage to securely transport your data.
Hunton Privacy
MARCH 2, 2023
s ability to assist allies and partners in strengthening cybersecurity, (iv) building coalitions to reinforce global norms of responsible state behavior, and (v) securing global supply chains for information, communications and operational technology products and services that power the U.S. economy.

ARMA International
JANUARY 30, 2020
On December 23, Yahoo News [1] reported on a Department of Defense memo [2] warning military personnel that using direct-to-consumer (DTC) DNA testing could pose “personal and operational risks.” In other words, the Pentagon is concerned about hostile entities using such biometric data to better surveil and track the military.

Information Governance Perspectives
APRIL 5, 2023
Wireless telematics devices and “black box” technologies collect and transmit data on vehicle use, maintenance requirements, and automotive servicing. John Danenberger, CPCU, is Corporate Counsel at State Farm Insurance and specializes in addressing emerging issues around telematics. What’s it like to work in this field?

IT Governance
FEBRUARY 14, 2024
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. Financial information, medical data, health reimbursements, postal addresses, telephone numbers and emails are not thought to have been compromised.

IT Governance
SEPTEMBER 1, 2020
There were a massive 99 data breaches and cyber attacks in August, making it the third-biggest monthly total of the year by number of security incidents. You can find our full list of publicly disclosed data breaches from August in this blog, with incidents affecting UK organisations listed in bold. Data breaches. Cyber attacks.

IT Governance
MARCH 28, 2019
There’s a new compiler at the helm of our monthly list of data breaches, following the departure of IT Governance stalwart Lewis Morgan, who leaves me with some mighty big shoes to fill. Fortunately – or, rather, unfortunately – the new regime has a familiar ring to it, with another mammoth list of data breaches. Data breaches.

Hunton Privacy
AUGUST 2, 2021
On June 16, 2021, Connecticut Governor Ned Lamont signed HB 5310, An Act Concerning Data Privacy Breaches. In passing the law, Connecticut joins a number of other states in expanding the definition of “personal information” in its data breach notification statute. Cybersecurity Safe Harbor (HB 6607).

Schneier on Security
FEBRUARY 28, 2024
In the first week of January, the pharmaceutical giant Merck quietly settled its years-long lawsuit over whether or not its property and casualty insurers would cover a $700 million claim filed after the devastating NotPetya cyberattack in 2017. The 9/11 attacks cost insurers and reinsurers $47 billion. 11, 2001, terrorist attacks.

DLA Piper Privacy Matters
JUNE 4, 2021
Increased scrutiny over connected car and automobile industry data from Chinese regulators, including push towards data localisation. China is a leading marketing for connected and autonomous vehicles, and use and analytics of connected vehicle data has been encouraged by Chinese Government support of big data and AI technology.
Hunton Privacy
JUNE 22, 2020
On July 1, 2020, amendments to Vermont’s data breach notification law, signed into law earlier this year, will take effect along with Vermont’s new student privacy law. Student Data Privacy. Security Breach Notice Act. The number of affected consumers exceeding 5,000 is no longer a basis for providing substitute notice.

Hunton Privacy
JUNE 14, 2018
Recently, Colorado’s governor signed into law House Bill 18-1128 “concerning strengthening protections for consumer data privacy” (the “Bill”), which takes effect September 1, 2018.

eSecurity Planet
MARCH 3, 2023
The initiatives that stand out the most — critical infrastructure security standards, a national data privacy and security law, and liability for security failures — will likely take time and the support of Congress to implement. ” Those fundamental shifts are focused on two core priorities. .”

Collibra
NOVEMBER 2, 2020
The California Consumer Privacy Act (CCPA) came into effect four years after the General Data Protection Regulation (GDPR) was adopted. Despite coming at the heels of the GDPR, the recent California privacy law promptly established and defined its own concepts around consumer-related data. . Geolocation data.

eSecurity Planet
OCTOBER 5, 2021
Malware has been around for nearly 40 years, longer even than the World Wide Web, but ransomware is a different kind of threat, capable of crippling a company and damaging or destroying its critical data. Zero trust is an important new tool to add to all that, essentially walling off your most important data. Data backup.

KnowBe4
MARCH 28, 2023
You can upload your own SCORM training modules into your account for home workers Active Directory or SCIM integration to easily upload user data, eliminating the need to manually manage user changes Find out how 50,000+ organizations have mobilized their end-users as their human firewall. in exponential terms. back in 2020.

KnowBe4
MAY 9, 2023
Grimes, KnowBe4's Data-Driven Defense Evangelist, where he'll share a comprehensive strategy for phishing mitigation. Verizon's Data Breach Report showed that 81% of hacking-related breaches used either stolen and/or weak passwords. New Jersey appellate division judges rejected the insurers' argument that the 2017 attack, which U.S.

Thales Cloud Protection & Licensing
FEBRUARY 15, 2018
Barely a day goes by where we don’t hear of a data breach. Affecting big companies and small in virtually every vertical and hitting government institutions at the local, state and federal level, sensitive data is routinely exfiltrated, stolen and leveraged with shocking regularity. For example, are they encrypting their data?

eSecurity Planet
FEBRUARY 16, 2021
Without a comprehensive network segmentation or microsegmentation policy, malicious actors can also move laterally within your organization’s network, infect endpoints and servers, and demand a ransom for access to your data. Attackers will inform the victim that their data is encrypted. How ransomware works. Screenshot example.

IT Governance
JUNE 27, 2019
The ransomware was accompanied by a note: “Your files are encrypted with the strongest military algorithms. Without our special decoder it is impossible to restore the data.”. Cyber security experts and governments urge victims to never pay the ransom.

Krebs on Security
SEPTEMBER 21, 2018
In addition, the law requires the big three bureaus to offer free electronic credit monitoring services to all active duty military personnel. By law, each of the three major credit reporting bureaus must provide a free copy of your credit report each year — but only if you request it via the government-mandated site annualcreditreport.com.

ForAllSecure
MAY 17, 2023
Chris Gray of Deep Watch talks about the view from the inside of a virtual SOC, the ability to see threats against a large number of SMB organizations, and the changes to cyber insurance we’re seeing as a result. VAMOSI: Cybersecurity insurance. cyber insurance as a whole was changing heavily. And why is that?

KnowBe4
MAY 2, 2023
You can upload your own SCORM training modules into your account for home workers Active Directory or SCIM Integration to easily upload user data, eliminating the need to manually manage user changes Find out how 55,000+ organizations have mobilized their end-users as their human firewall. Data breaches are getting larger and more frequent.

Krebs on Security
SEPTEMBER 10, 2018
There are dozens of private companies that specialize in providing consumer credit reports and scores to specific industries, including real estate brokers, landlords, insurers, debt buyers, employers, banks, casinos and retail stores. My guess is the vast majority of Americans have never heard of most of these companies.

KnowBe4
JUNE 6, 2023
of all email-based attacks according to Barracuda's data but are responsible for 66% of all breaches." China's People's Liberation Army (PLA) is increasingly focused on "Cognitive Warfare," a term referring to artificial intelligence (AI)-enabled military systems and operational concepts. This is that fact: ".spear make up only 0.1%

Krebs on Security
DECEMBER 29, 2022
Internal Revenue Service website for months: Anyone seeking to create an account to view their tax records online would soon be required to provide biometric data to a private company in Virginia — ID.me. Super Bowl Sunday watchers are treated to no fewer than a half-dozen commercials for cryptocurrency investing.

Data Matters
APRIL 23, 2018
A high-profile cyber incident may cause substantial financial and reputational losses to an organization, including the disruption of corporate business processes, destruction or theft of critical data assets, loss of goodwill, and shareholder and consumer litigation. Creating an enterprise-wide governance structure.
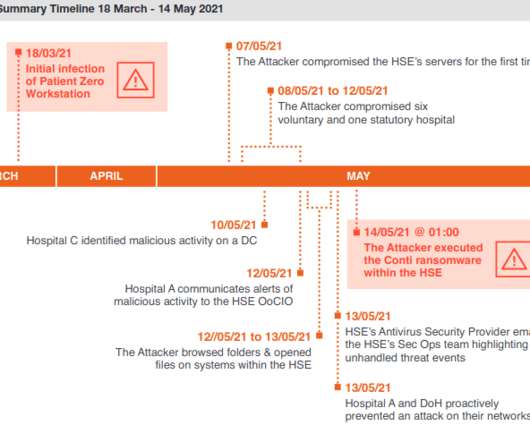
Krebs on Security
DECEMBER 13, 2021
The HSE ultimately enlisted members of the Irish military to bring in laptops and PCs to help restore computer systems by hand. For example, it is unclear how much data would have been unrecoverable if a decryption key had not become available as the HSE’s backup infrastructure was only periodically backed up to offline tape.

eSecurity Planet
APRIL 26, 2024
Effective implementation improves data throughput, system reliability, and overall security for any organization. Network Elements Networks connect physical and virtual assets and control the data flow between them. Storage: Contains user and application data at rest; can be integrated with other elements (server, etc.)
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content