EU to Force IoT, Wireless Device Makers to Improve Security
eSecurity Planet
NOVEMBER 1, 2021
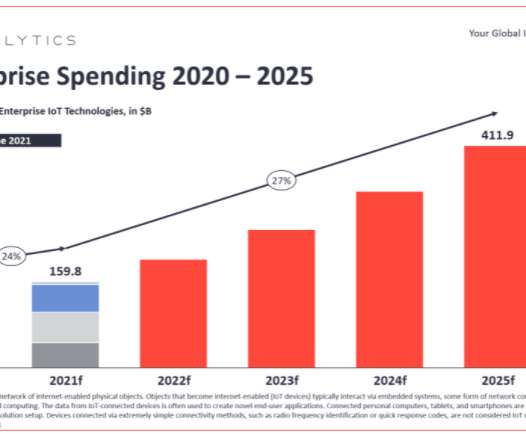
The European Union is poised to place more demands on manufacturers to design greater security into their wireless and Internet of Things (IoT) devices. Manufacturers will be required to adhere to the new cybersecurity safeguards when designing and producing these products. IoT market growth. million devices being shipped.

















Let's personalize your content