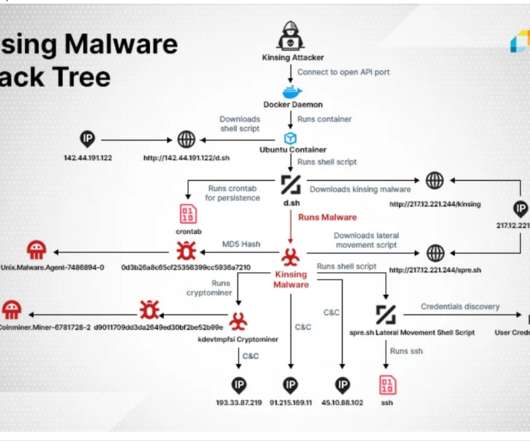
Hackers target Docker servers to deploy the new Kinsing cryptocurrency miner
Security Affairs
APRIL 6, 2020
Experts uncovered a hacking campaign that is breaching Docker clusters to deploy a new crypto-mining malware tracked as Kinsing. Cloud security firm Aqua Security uncovered a hacking campaign carried out during the past months, hackers are scanning the Internet for Docker servers running API ports exposed without a password.











Let's personalize your content