Security Affairs newsletter Round 450 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
DECEMBER 17, 2023
CISA and ENISA enhance their Cooperation CISA adds Qlik bugs to exploited vulnerabilities catalog Report: 2.6

Security Affairs
DECEMBER 17, 2023
CISA and ENISA enhance their Cooperation CISA adds Qlik bugs to exploited vulnerabilities catalog Report: 2.6
Data Protection Report
MARCH 7, 2024
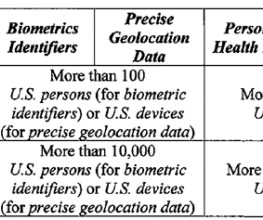
government, including the military and Intelligence Community.” government, including the military and Intelligence Community.” (at A medical facility in the United States contracts with a company headquartered in a country of concern to provide IT-related services. What types of data brokerage transactions are in-scope?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IT Governance
MARCH 11, 2024
Source 1 ; source 2 (Update) IT services Taiwan Yes 2,451,197 RMH Franchise Corporation Source (New) Hospitality USA Yes 1.5 Source 1 ; source 2 (Update) IT services Taiwan Yes 2,451,197 RMH Franchise Corporation Source (New) Hospitality USA Yes 1.5 Source (New) Professional services Netherlands Yes 28.3 TB Paysign, Inc.

The Last Watchdog
NOVEMBER 9, 2020
IoT devices help remotely control our household appliances, power plants, smart buildings, factories, airports, shipyards, trucks, trains and military. The challenge of the moment is that many companies already have their hands full trying to improve their security posture as they migrate their legacy, on premises, IT systems to the cloud.

The Last Watchdog
JUNE 17, 2020
Related: Defending botnet-driven business logic hacks APIs made possible the astounding cloud, mobile and IoT services we have today. A great example of this, Keil points out, is the Open Financial Exchange ( OFX , ) the data-stream format that enables wire transfers to be carried out across the Internet.

Thales Cloud Protection & Licensing
JULY 24, 2018
Originally Featured in Global Military Communications Magazine’s June/July Issue. Its unique capabilities include the design and deployment of equipment, systems and services to meet complex security requirements. Our 2018 Thales Data Threat Report, Federal Edition , issued in conjunction with analyst firm 451 Research, polled U.S.

eSecurity Planet
FEBRUARY 16, 2021
Cybercriminals send millions of malicious emails to at-random organizations and users, but an effective spam filter that continually adapts alongside a cloud-based threat intelligence center can prevent more than 99% of these from ever reaching employees’ desktops. A ransomware attack is about as bad as a cyber attack can get. Spam Filter.
Let's personalize your content