Crooks stole more than $1.5M worth of Bitcoin from General Bytes ATMs
Security Affairs
MARCH 21, 2023
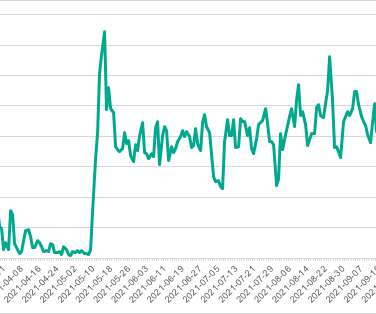
Cryptocurrency ATM manufacturers General Bytes suffered a security incident that resulted in the theft of $1.5M GENERAL BYTES is the world’s largest Bitcoin, Blockchain, and Cryptocurrency ATM manufacturer. The hackers were also able to turn off the two-factor authentication (2FA). worth of cryptocurrency.




















Let's personalize your content