Ongoing Raspberry Robin campaign leverages compromised QNAP devices
Security Affairs
JULY 9, 2022
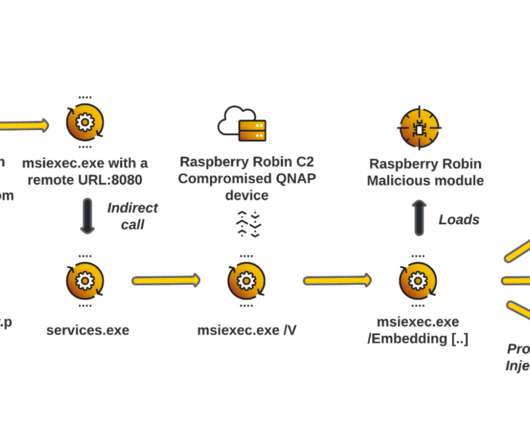
The malware was first spotted in September 2021, the experts observed Raspberry Robin targeting organizations in the technology and manufacturing industries. continues the analysis. The malware uses TOR exit nodes as a backup C2 infrastructure. Initial access is typically through infected removable drives, often USB devices.


















Let's personalize your content